-
 Data Security
Data SecurityMar 29, 2020
5 Cybersecurity Concerns of Industry Insiders
We asked professionals attending two of the world’s biggest cybersecurity conferences – RSA in San Francisco and Infosecurity in London – five questions to gauge their opinions and attitudes about current cybersecurity concerns and issues. Read on to discover what we found!

Rachel Hunt
3 min read
-
 Data Security
Data SecurityMar 29, 2020
Zero-Day Vulnerability Explained
Find out how zero-day vulnerabilities become zero-day exploits and zero-day attacks, and how to defend your network from zero-day attacks and exploits.

Michael Buckbee
3 min read
-
 Data Security
Data SecurityMar 29, 2020
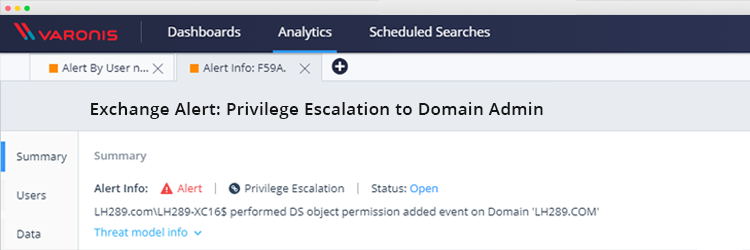
Exchange Vulnerability: How to Detect Domain Admin Privilege Escalation
Researchers recently uncovered a vulnerability in Exchange that allows any domain user to obtain Domain admin privileges that allow them to compromise AD and connected hosts. Here’s how the attack...

Michael Buckbee
1 min read
-
 Data Security
Data SecurityMar 29, 2020
Working in Cybersecurity: A Day in the Life
Explore what working in cybersecurity is like through expert Q&As, career paths, required skills, and tips for breaking into this growing field.

Rob Sobers
19 min read
-
 Data Security
Data SecurityMar 29, 2020
What Certifications Should I Get for IT?
Elevate your IT knowledge and credentials by using our IT certification flowcharts to find the right certification for your experience level and interests.

Rob Sobers
2 min read
-
 Data Security
Data SecurityMar 29, 2020
Maximize your ROI: Maintaining a Least Privilege Model
TL;DR: Managing permissions can be expensive. For a 1,000 employee company, the overhead of permissions request tickets can cost up to $180K/year. Automating access control with DataPrivilege can save $105K/year...

Michael Buckbee
5 min read
-
 Data Security
Data SecurityMar 29, 2020
11 Popular Programming Languages to Open Doors
This extensive list of programming languages includes an overview of each language, its common uses, career options, fields, origin, features and resources.

Rob Sobers
8 min read
-
 Data Security
Data SecurityMar 29, 2020
12 Ways Varonis Helps You Manage Mergers and Acquisitions
A well-constructed Merger & Acquisition (M&A) playbook reduces the overall time, cost and risk of the upcoming merger and/or acquisition. Gartner advises that organizations who intend to grow through acquisitions...

Michael Buckbee
6 min read
-
 Data Security
Data SecurityMar 29, 2020
Which Cybersecurity Career Is Right For Me?
Finding the right career path in the cybersecurity industry isn’t always easy. We interviewed cybersecurity experts to find out what inspired them!

Rob Sobers
1 min read
-
 Data Security
Data SecurityMar 29, 2020
The World in Data Breaches
The number of lost or stolen data records varies around the world. Using data from the Breach Level Index, we visualized where these records are concentrated based on the locations of the organizations that reported them. Take a look!

Rob Sobers
2 min read
-
 Data Security
Data SecurityMar 29, 2020
CISM vs. CISSP Certification: Which One is Best for You?
CISM and CISSP are two of the most highly regarded certifications for cybersecurity leaders and practitioners, but their requirements aren’t trivial. Both require a significant investment of time and money – so It’s important to determine which is right for you. Take a look at our comparison of the two to learn more.

Michael Buckbee
3 min read
-
 Data Security
Data SecurityMar 29, 2020
Koadic: Implants and Pen Testing Wisdom, Part III
One of the benefits of working with Koadic is that you too can try your hand at making enhancements. The Python environment with its nicely organized directory structures lends itself to...

Michael Buckbee
4 min read
SECURITY STACK NEWSLETTER
Ready to see the #1 Data Security Platform in action?
Ready to see the #1 Data Security Platform in action?
“I was amazed by how quickly Varonis was able to classify data and uncover potential data exposures during the free assessment. It was truly eye-opening.”
Michael Smith, CISO, HKS
"What I like about Varonis is that they come from a data-centric place. Other products protect the infrastructure, but they do nothing to protect your most precious commodity — your data."
Deborah Haworth, Director of Information Security, Penguin Random House
“Varonis’ support is unprecedented, and their team continues to evolve and improve their products to align with the rapid pace of industry evolution.”
Al Faella, CTO, Prospect Capital