-
 Cloud Security Data Security Ransomware Threat Research
Cloud Security Data Security Ransomware Threat ResearchMar 12, 2025
Mind Games: How Social Engineering Tactics Have Evolved
Instead of using advanced tools or complex scripts, skilled threat actors infiltrate systems and steal data using the most effective weapon of all — words.

Varonis Threat Labs
7 min read
-
 Threat Research
Threat ResearchMar 05, 2025
Salt Typhoon: The Threat Group Behind Major Cyberattacks
Varonis Threat Labs profiles Salt Typhoon, an APT group that is responsible for a series of breaches targeting U.S. infrastructure and government agencies.

Joseph Avanzato
5 min read
-
 Threat Research
Threat ResearchFeb 13, 2025
Astaroth: A New 2FA Phishing Kit Targeting Gmail, Yahoo, AOL, O365, and Third-Party Logins
Discover how Astaroth phishing kits bypass security, offer bulletproof hosting, and how Varonis protects businesses from advanced cyber threats.

Daniel Kelley
2 min read
-
 Threat Research
Threat ResearchJan 29, 2025
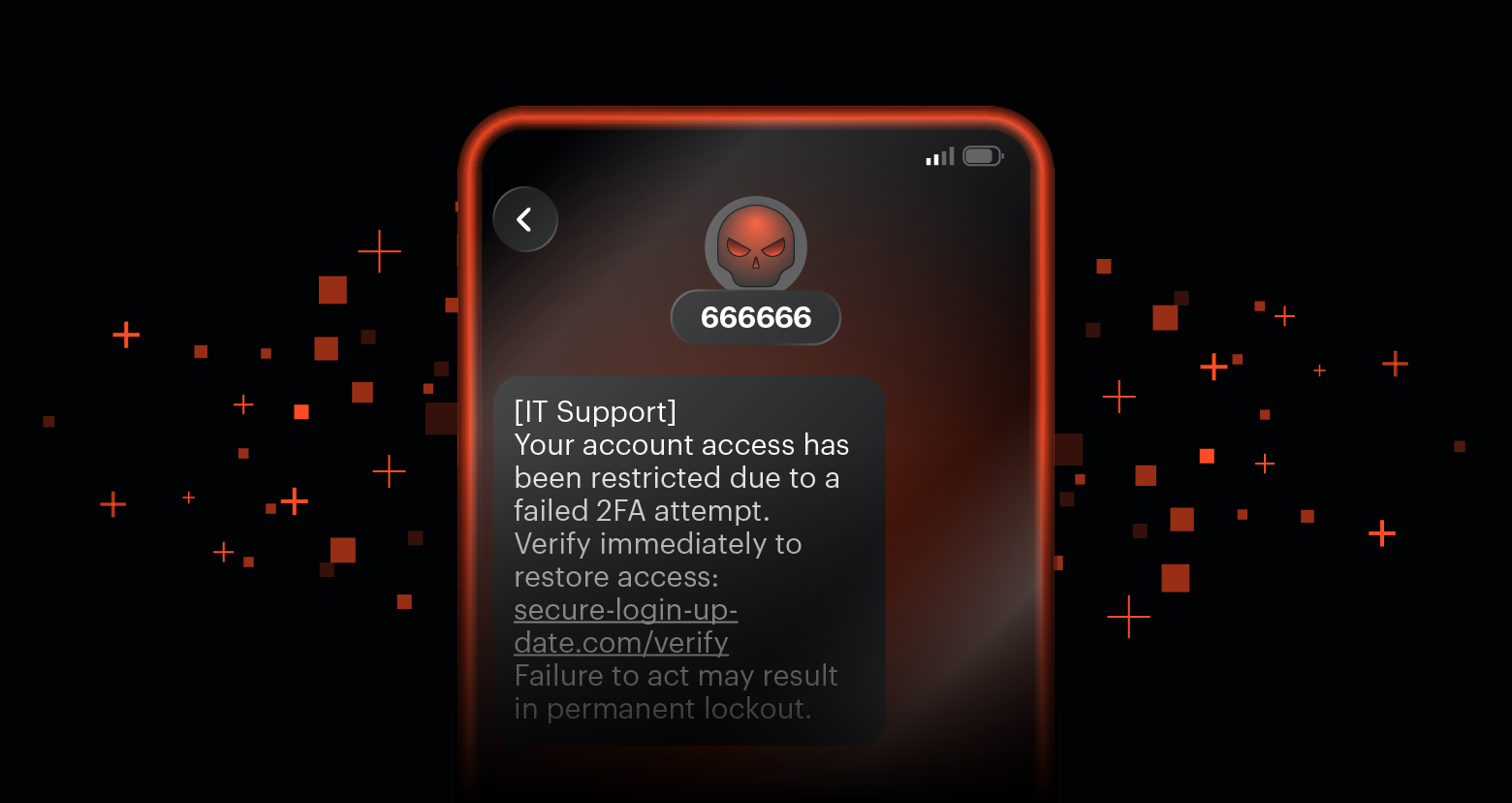
Devil-Traff: A New Bulk SMS Platform Driving Phishing Campaigns
Discover how the Devil-Traff bulk SMS platform fuels phishing attacks with spoofing and automation.

Daniel Kelley
2 min read
-
 Threat Research
Threat ResearchJan 06, 2025
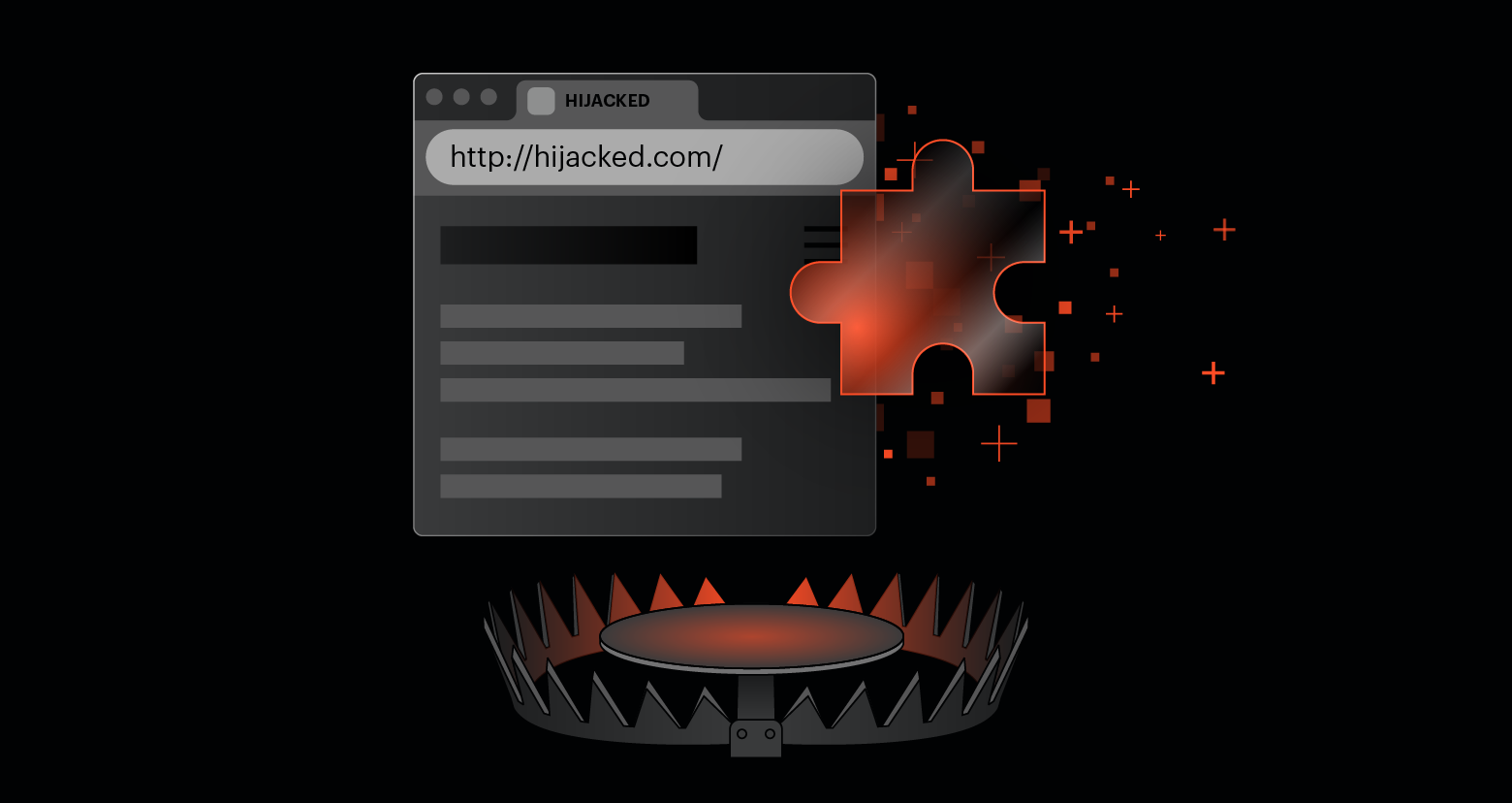
Meet PhishWP — The New WordPress Plugin That’s Turning Legit Sites into Phishing Traps
Discover how PhishWP, a malicious WordPress plugin, turns trusted sites into phishing traps and how to protect yourself with Varonis.

Daniel Kelley
3 min read
-
 Data Security Threat Research
Data Security Threat ResearchNov 26, 2024
Caught in the Net: Unmasking Advanced Phishing Tactics
Learn new, advanced phishing tactics being used by attackers and how your organization can combat them.

Tom Barnea
4 min read
-
 Threat Research
Threat ResearchNov 14, 2024
Varonis Discovers New Vulnerability in PostgreSQL PL/Perl
Varonis discovered a vulnerability (CVE-2024-10979) in the Postgres trusted language extension PL/Perl that allows setting arbitrary environment variables in PostgreSQL session processes.

Varonis Threat Labs
2 min read
-
 Threat Research
Threat ResearchNov 12, 2024
GoIssue — The Tool Behind Recent GitHub Phishing Attacks
Discover how GoIssue targets GitHub users, posing significant risks to developers and organizations.

Daniel Kelley
2 min read
-
 Active Directory Microsoft 365 Threat Research
Active Directory Microsoft 365 Threat ResearchNov 10, 2024
New Organizational Messages Feature in Microsoft 365 a Potential Risk
The new organizational messages feature for Microsoft 365 enhances how IT and security teams communicate with users at scale, but also generates risks.

Shawn Hays
3 min read
-
 Threat Research
Threat ResearchSep 26, 2024
New CVEs in OpenPrinting CUPS Software
A series of vulnerabilities in OpenPrinting CUPS Software indicates an attack vector for RCE, one of the worst possible consequences for a vulnerability.

Varonis Threat Labs
3 min read
-
 Threat Research
Threat ResearchSep 16, 2024
Data Theft in Salesforce: Manipulating Public Links
Varonis Threat Labs uncovered a vulnerability in Salesforce's public link feature that threat actors could exploit to retrieve sensitive data.

Nitay Bachrach
6 min read
-
 Threat Research
Threat ResearchJul 18, 2024
The Power and Peril of RMM Tools
Discover real-world examples of remote monitoring and management (RMM) tool exploits and how to protect your organization from these attacks.

Tom Barnea
4 min read
SECURITY STACK NEWSLETTER
Ready to see the #1 Data Security Platform in action?
Ready to see the #1 Data Security Platform in action?
“I was amazed by how quickly Varonis was able to classify data and uncover potential data exposures during the free assessment. It was truly eye-opening.”
Michael Smith, CISO, HKS
"What I like about Varonis is that they come from a data-centric place. Other products protect the infrastructure, but they do nothing to protect your most precious commodity — your data."
Deborah Haworth, Director of Information Security, Penguin Random House
“Varonis’ support is unprecedented, and their team continues to evolve and improve their products to align with the rapid pace of industry evolution.”
Al Faella, CTO, Prospect Capital