-
.png) Threat Research
Threat ResearchSep 15, 2022
Fighting Golden Ticket Attacks with Privileged Attribute Certificate (PAC)
Learn how and why to control the Active Directory Environment state with PACRequestorEnforcement, the implications of doing so and how to detect Golden Ticket attacks happening in your network.

Masha Garmiza
4 min read
-
 Varonis Products
Varonis ProductsSep 13, 2022
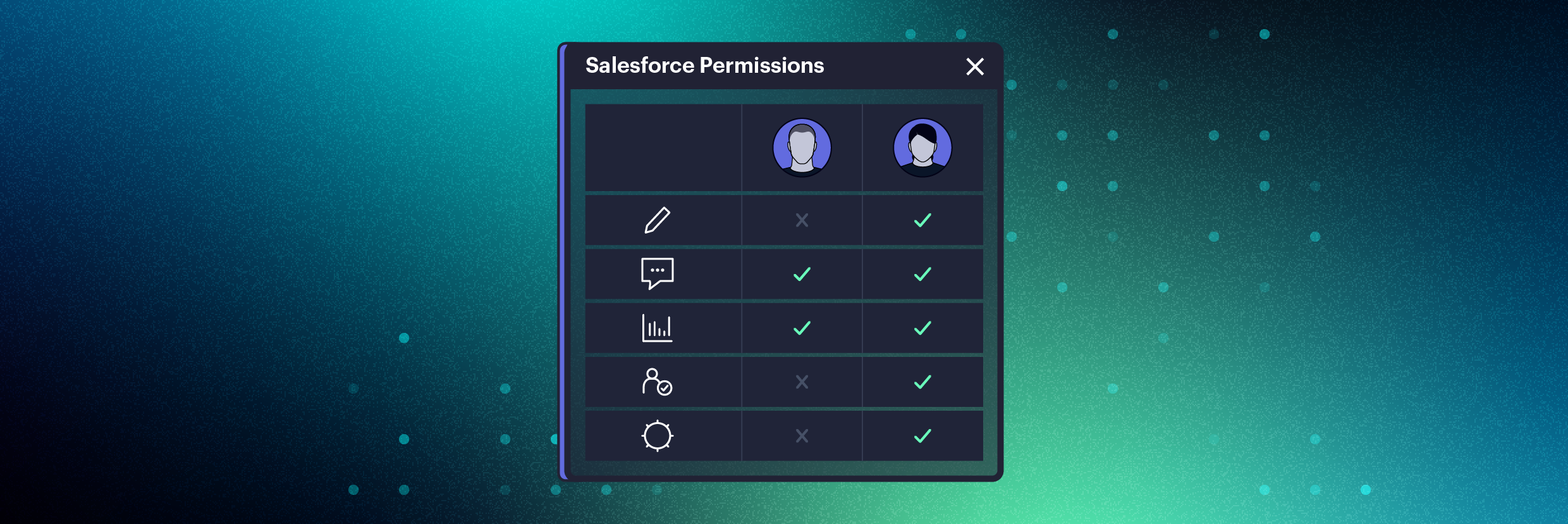
Compare Salesforce user permissions with ease
DatAdvantage Cloud now enables admins to compare two Salesforce users’ effective permissions side-by-side with a simple click of a button.

Nathan Coppinger
2 min read
-
 Data Security
Data SecuritySep 09, 2022
What Is a Data Leak? Definition and Prevention Tips
Learn why data leaks can be devastating for companies and how you can defend against them.

Nolan Necoechea
4 min read
-
 Data Security
Data SecuritySep 09, 2022
What Is Zero Trust? Architecture and Security Guide
Zero trust is a security model that protects against both malicious insiders and external attacks that have breached your perimeter.

Michael Buckbee
8 min read
-
 Privacy & Compliance
Privacy & ComplianceSep 02, 2022
U.S. Privacy Laws: The Complete Guide
This guide breaks down the entirety of the U.S. privacy law ecosystem to help you understand the rights and obligations of citizens and businesses.

David Harrington
9 min read
-
 Privacy & Compliance
Privacy & ComplianceAug 26, 2022
SOC 2 Compliance Definition & Checklist
System and Organization Controls (SOC 2) compliance requires adherence to specific guidelines. This detailed definition and checklist can get you started.

David Harrington
6 min read
-
 Data Security
Data SecurityAug 26, 2022
What is Mimikatz? The Beginner's Guide
Mimikatz is an open-source application that allows users to view and save authentication credentials like Kerberos tickets.

Michael Buckbee
4 min read
-
 Threat Research
Threat ResearchAug 22, 2022
Anatomy of a SolidBit Ransomware Attack
Solidbit is a ransomware variant derived from Yashma and containing elements of LockBit. Discover how Solidbit's capabilities, execution, what file types it targets, and how to tell if you're been infected.

Jason Hill
6 min read
-
 Data Security
Data SecurityAug 19, 2022
How to Use Wireshark: Comprehensive Tutorial + Tips
Learn how to use Wireshark, a widely-used network packet and analysis tool. This tutorial has everything from downloading to filters to packets.

Kody Kinzie
7 min read
-
 Salesforce
SalesforceAug 18, 2022
Your Sales Data Is Mission-Critical: Are You Protecting It?
If you’re like many executives, you might assume your data is secure within those cloud applications. That’s a dangerous assumption, though. Cloud providers are responsible for everything that delivers their application (e.g., their data center); it’s your responsibility to protect the data inside it.

Yaki Faitelson
3 min read
-
 Varonis Products
Varonis ProductsAug 17, 2022
Varonis Maps Cloud Security Alerts to MITRE ATT&CK
In Varonis’ latest update of DatAdvantage Cloud, we’re layering MITRE ATT&CK tactics and techniques over cloud alerts to aid in faster incident response.

Yumna Moazzam
2 min read
-
 Cloud Security
Cloud SecurityJul 22, 2022
How to Create S3 Buckets in AWS with CloudFormation: Step-by-Step Guide
Use AWS CloudFormation to create resources such as S3 buckets. Infrastructure as code enables a repeatable, reliable deployment process. Learn more here.

Daniel Miller
6 min read
SECURITY STACK NEWSLETTER
Ready to see the #1 Data Security Platform in action?
Ready to see the #1 Data Security Platform in action?
“I was amazed by how quickly Varonis was able to classify data and uncover potential data exposures during the free assessment. It was truly eye-opening.”
Michael Smith, CISO, HKS
"What I like about Varonis is that they come from a data-centric place. Other products protect the infrastructure, but they do nothing to protect your most precious commodity — your data."
Deborah Haworth, Director of Information Security, Penguin Random House
“Varonis’ support is unprecedented, and their team continues to evolve and improve their products to align with the rapid pace of industry evolution.”
Al Faella, CTO, Prospect Capital

