With cyberattacks and data breaches on the rise, companies of all sizes need to place an emphasis on securing their technology assets. However, assembling a full-time in-house IT security team may not be feasible due to budget constraints and competing priorities.
The smart solution, in this case, is to look at partnering with an SOC, or security operations center. A SOC is an outsourced office that is completely dedicated to analyzing traffic flow and monitoring for threats and attacks.
Get the Free Pen Testing Active Directory Environments EBook
Here you'll learn about what is SOC and the basic functions of a SOC as well as the different models and roles involved. It's important to know what the best practices are for SOC security so that you can research your options and choose the best vendor.
- What is a Security Operations Center?
- Benefits of a SOC
- How SOCs Operate: 7 Key Responsibilities
- SOC Job Roles
- SOC Models
- SOC Best Practices
- SOC FAQs
What is a Security Operations Center?
Security Operations Centers (SOCs) are a centralized location within the organization that houses a security team responsible for monitoring the company's security posture and any cybersecurity threats. The SOC helps to protect all areas of the company's IT infrastructure including but not limited to: networks, software, and existing data. SOCs carry out several functions to meet the main goal of defending against cyber-attacks.
A security operation center functions on an on-going, 24/7/365 basis to track events logged within the organization's system and decide how these events will be handled. They are typically backed by a team of security analysts, engineers and managers who work together to immediately respond to security threats.
Basically, you can fully rely on this team to deal with security problems in real time and keep your network protected. The security operations center also continuously seeks ways to improve the organization's security posture and how to prevent future cyber-attacks. An SOC is a wise investment to consider if you want to sleep peacefully at night knowing your network is continuously protected from hackers.
Benefits of a SOC
With technology playing such a key role in every industry worldwide, cybersecurity must be a priority for all organizations. The SOC model has proven to be effective in many situations, and we'll explore some of the key benefits below. Just keep in mind that by outsourcing your IT security activities, you do inherit a certain level of risk.
Cost-Effectiveness
For most companies, employee salary is the biggest cost in their budget. Employing an entire team of cybersecurity professionals requires a huge up-front and ongoing investment. By adopting the SOC model, you are paying for a service instead with clear terms and less liability.
Less Downtime
When a website or application goes down, it often means lost revenue or a negative hit against a company's reputation. Using a SOC can minimize those effects and shorten the time to incident resolution. Even the most reliable uptime monitoring tools aren't perfect, so having a security operations center in place builds redundancy into your network. Your internal staff has so many competing priorities that it might be beneficial to outsource cybersecurity activities to a SOC.
Customer Trust
A single data breach, like the Capital One data breach, can cause a customer to think twice about trusting a company with their private information. With so little room for error, putting a security operations center to work monitoring systems around the clock provides a sense of trust to all those who rely on the network and data.
How SOCs Operate: 7 Key Responsibilities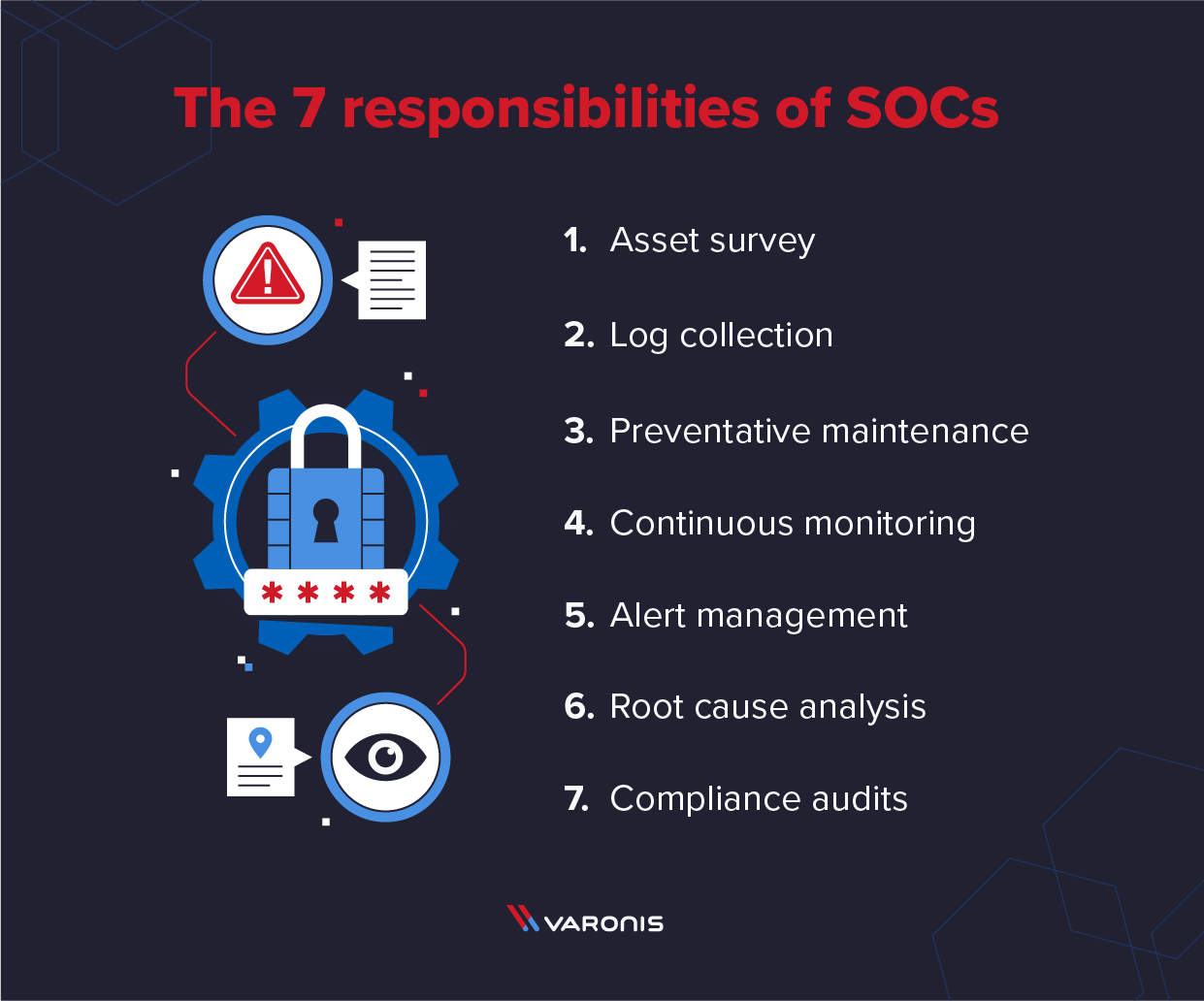
Until the recent rise of cloud computing, standard security practice was for a company to choose a traditional software malware scanning solution either via download or, in ancient days, a CD-ROM that arrived via mail. They'd add to that a firewall installed at the edge of the network, and trust that those measures would keep their data and systems safe. Today's reality is a far different environment, with threats being cast all across the net as hackers invent new ways to launch profitable and sophisticated attacks like ransomware.
A SOC operates as a centralized function within an organization employing people and utilizing tools to continuously monitor security posture to detect and prevent suspicious malware and cybersecurity incidents. In this context, it provides a layer of rented expertise to a company's cybersecurity strategy that operates 24/7 so that networks and endpoints are constantly being monitored. If a vulnerability is found or an incident is discovered, the SOC will engage with the on-site IT team to respond to the issue and investigate the root cause.
There is a core set of operational functions that a SOC must perform in order to add value to an organization. Individual SOCs conduct various activities and functions internally no matter what model they choose to operate under. However, there is a core set of operational functions that a SOC must perform in order to add value to an organization. We have termed these as the seven competencies and will outline them here.
- Asset Survey: For a SOC to help a company stay secure, they must have a complete inventory of what resources they need to protect. Otherwise, they may not be able to protect the full scope of the network. An asset survey should identify every server, router, firewall under enterprise control, as well as any other cybersecurity tools actively in use.
- Log Collection: Data is the most important thing for a SOC to function properly and logs serve as the key source of information regarding network activity. The SOC should set up direct feeds from enterprise systems so that data is collected in real-time. Obviously, humans cannot digest such large amounts of information, which is why log scanning tools powered by artificial intelligence algorithms are so valuable for SOCs, though they do pose some interesting side effects that humanity is still trying to iron out.
- Preventative Maintenance: In the best-case scenario, the SOC can prevent cyberattacks from occurring by being proactive with their processes. This includes installing security patches and adjusting firewall policies on a regular basis. Since some cyberattacks begin as insider threats, a SOC must also look within the organization for risks also.
- Continuous Monitoring: To be ready to respond to a cybersecurity incident, the SOC must be vigilant in its monitoring practices. A few minutes can be the difference between blocking an attack and letting it take down an entire system or website. SOC tools run scans across the company's network to identify potential threats and other suspicious activity.
- Alert Management: Automated systems are great at finding patterns and following scripts. But the human element of a SOC proves its worth when it comes to analyzing automated alerts and ranking them based on their severity and priority. SOC staff must know what responses to take and how to verify that an alert is legitimate.
- Root Cause Analysis: After an incident occurs and is resolved, the job of the SOC is just beginning. Cybersecurity experts will analyze the root cause of the problem and diagnose why it occurred in the first place. This feeds into a process of continuous improvement, with security tools and rules being modified to prevent future occurrences of the same incident.
- Compliance Audits: Companies want to know that their data and systems are safe but also that they are being managed in a lawful manner. SOC providers must perform regular audits to confirm their compliance in the regions where they operate.
SOC Job Roles
For those with a background in cybersecurity, a SOC provider is a perfect place to build a career. Let's run through some of the primary positions involved in running a SOC.
SOC Manager
SOC Managers are the leaders of their organization. The means top-level responsibilities fall to them, including hiring/firing, budgeting, and setting priorities. They typically report directly to the executive level, especially the chief information security officer (CISO).
Compliance Auditor
The compliance auditor plays a key role in the standardization of processes within a SOC. They essentially function as the quality control department, ensuring that SOC members are following protocols and adhering to government or industry regulations.
Incident Responder
Incident Responders are the people who are paid to react to alerts as soon as possible. They use a wide range of monitoring services to rank the severity of alerts, and once one has been deemed a full-scale issue, they engage with the affected enterprise to begin recovery efforts.
SOC Analyst
A SOC analyst is responsible for reviewing past incidents and determining the root cause behind them. They typically have many years of professional experience in cybersecurity and are critical to understanding the technical aspects behind breaches and how to prevent them.
Threat Hunter
These are the proactive members of the team who run tests across a network to identify areas of weaknesses. The goal is to find vulnerabilities before a hacker can exploit them with an attack and improve overall data security.
SOC Models
Up to this point, we've been focused on an external SOC processor model where the company in question is paying for an outside SOC provider to manage their cybersecurity needs. However, there are several other SOC architecture models that can function in a similar fashion.
Dedicated or Internal SOC
The enterprise sets up its own cybersecurity team within its workforce. If you decide to run your own dedicated SOC, you'll need the personnel and expertise to fulfill all SOC job roles from manager down to analyst.
Virtual SOC
The security team does not have a dedicated facility and often works remotely. Under a virtual SOC model, the SOC manager role becomes even more critical in terms of coordinating individuals across multiple locations.
Global or Command SOC
A high-level group that oversees smaller SOCs across a large region. Large, globally-distributed organizations often favor the global SOC model as it allows them to implement strategic initiatives and standardize procedures down to the threat hunter and analyst levels.
Co-Managed SOC
The enterprise's internal IT is tightly coupled with an outsourced vendor to manage cybersecurity needs jointly. This is one of the most cost-effective models, as you won't have to employ every role and can work with your partner's compliance auditor to ensure proper procedures.
SOC Best Practices

As the SOC model has matured and evolved over recent years, standard best practices are emerging in terms of how best to operate a SOC. Whether you're operating your internal SOC or looking for a SOC provider, here are some key best practices to implement.
Implementing Automation
SOC teams have to be as efficient as possible. That means they can't waste all of their time reading log entries and watching traffic flows. Instead, they need to implement automation security operations center computer tools that use artificial intelligence to identify patterns and point them to what matters.
Cloud Approach
In the old days, you could slap a firewall at the edge of your data center and trust that everything inside was protected. But with the cloud computing movement, SOCs need to look at a wider scope. They should analyze how all pieces of a cloud infrastructure interact and where the vulnerabilities could be hiding.
Think Like a Hacker
Cybercriminals are always looking to invent new forms of attack that companies and individuals won't see coming. In order to stay ahead of them, cybersecurity SOC teams need to take the same creative approach. If they spend all day worrying about antiquated threats, they will be blind to the new types of attacks lingering on the horizon. Penetration and chaos testing are crucial security operations center activities, as they force teams to look for vulnerabilities that exist in unexpected places.
SOC FAQs
Q: Why do you need a security operation center?
A: An SOC is vital to protect data, systems, and other enterprise resources. With a SOC arrangement, you can be assured that your network is safeguarded from attacks so that your employees can focus on their core activities instead of worrying about cybersecurity.
Q: What should a SOC monitor?
A: SOC tools and teams should monitor all traffic on a network from external sources. This means that every server, router, and database must be within the scope of the security operations center team.
Q: What is the difference between NOC and SOC?
A: A NOC is a network operations center. A NOC is focused primarily on minimizing downtime and meeting service level agreements, whereas a SOC looks deeper into cybersecurity threats and vulnerabilities.
Q: What is the difference between SOC and SIEM?
A: SIEM stands for Security Information and Event Management a software application that helps group events together for analysis and that can help provide context to security events. A SOC is a group of people and tools that work together while a SIEM is a tool they use.
Closing Thoughts
Employing a SOC--whether internal or outsourced--is one of the best ways to protect critical networks and data from both external and insider threats. A SOC can help you take preventative measures, limit the damage of hacks, and assess the cyber kill chain if one does take place. And by working with an experienced SOC partner like Varonis, you'll be able to get all the benefits of a SOC on a cost-efficient basis.
What should I do now?
Below are three ways you can continue your journey to reduce data risk at your company:
Schedule a demo with us to see Varonis in action. We'll personalize the session to your org's data security needs and answer any questions.
See a sample of our Data Risk Assessment and learn the risks that could be lingering in your environment. Varonis' DRA is completely free and offers a clear path to automated remediation.
Follow us on LinkedIn, YouTube, and X (Twitter) for bite-sized insights on all things data security, including DSPM, threat detection, AI security, and more.







-1.png)

