-
 Threat Research
Threat ResearchMay 11, 2026
Feeding Frenzy: RCE on Azure Cosmos for PostgreSQL
See how an Azure Cosmos for PostgreSQL vulnerability enabled remote code execution, its implications, and essential security best practices.

Coby Abrams
4 min read
-
 Threat Research
Threat ResearchMay 08, 2026
Canvas Attackers Compromise 275M Students, Teachers, and Staff
The Canvas breach reveals how cybercriminals are targeting education: learn how the attack unfolded, what data was exposed, and the risks ahead.

Joseph Avanzato
3 min read
-
 Email Security
Email SecurityMay 06, 2026
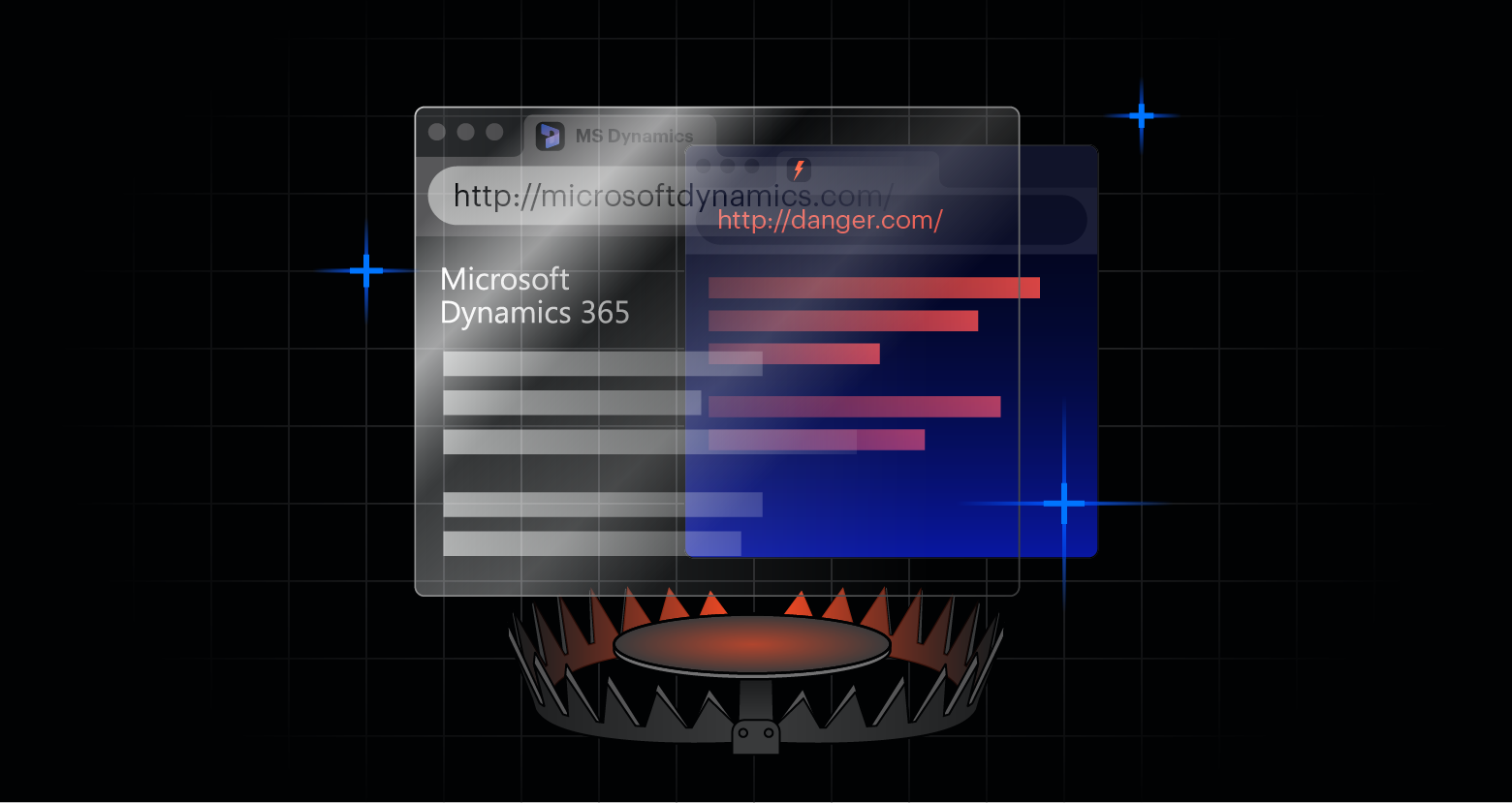
Abuse of Microsoft Dynamics Redirects Delivers Phishing Payloads at Scale
Varonis Interceptor stopped a phishing campaign abusing Microsoft Dynamics redirects, highlighting how attackers are leveraging trusted SaaS infrastructure to evade email defenses.

Meagan Huebner
3 min read
-
 AI Security Data Security
AI Security Data SecurityMay 05, 2026
AI Isn’t the Risk, Uncontrolled AI Is
Discover what it takes to secure AI and why most approaches fall short.

David Gibson
13 min read
-
 AI Security Threat Research
AI Security Threat ResearchApr 29, 2026
Meet Bluekit: The AI-Powered All-in-One Phishing Kit
Discover Bluekit, the AI-driven phishing kit that centralizes phishing operations with advanced features like automated domain registration and an AI Assistant.

Daniel Kelley
3 min read
-
 Threat Research
Threat ResearchApr 22, 2026
The "Success" Illusion: How Cross-Tenant ROPC Can Gaslight Your SOC and Poison Data
Discover how attackers exploit cross-tenant ROPC to create misleading login events, undermining your security and data integrity without breaching your systems.

Varonis Threat Labs
3 min read
-
 AI Security
AI SecurityApr 21, 2026
AI Security Platforms: Centralized Visibility, Enforcement and Monitoring for AI Systems
Discover how AI Security Platforms help organizations securely scale AI with centralized visibility, runtime enforcement, and end‑to‑end monitoring.

Meagan Huebner
4 min read
-
 AI Security Varonis Products
AI Security Varonis ProductsApr 20, 2026
Securing AI Application Development
Uncover where sensitive data leaks in AI development and the practical steps to reduce risk and scale safely.

Eugene Feldman
6 min read
-
.png) Threat Research
Threat ResearchApr 20, 2026
The Vercel Breach: Steps To Protect Your Organization
Vercel disclosed a major breach exposing customer environment secrets via a compromised AI tool. Learn what happened, why it matters, and the steps to protect your organization.

Chen Levy Ben Aroy
3 min read
-
 Threat Research
Threat ResearchApr 17, 2026
The Invisible Footprint: How Anonymous S3 Requests Evade AWS Logging
Learn how anonymous S3 requests evaded AWS CloudTrail logging via VPC endpoints, the risks to enterprises, and how AWS addressed the issue.

Maya Parizer
4 min read
-
 AI Security Data Security
AI Security Data SecurityApr 15, 2026
The Map is Not the Territory: The Impact of Anthropic Mythos on Data Security
Claude Mythos is a meaningful moment. But the real danger isn't the explosion of CVEs. It's what attackers find when they exploit them.

Brian Vecci
3 min read
-
 AI Security
AI SecurityApr 14, 2026
How Varonis Atlas Enables ISO/IEC 42001 Compliance
Learn how Varonis Atlas helps operationalize ISO/IEC 42001 with AI inventory, risk management, continuous monitoring, and audit-ready evidence.

Shawn Hays
5 min read
SECURITY STACK NEWSLETTER
Ready to see the #1 Data Security Platform in action?
Ready to see the #1 Data Security Platform in action?
“I was amazed by how quickly Varonis was able to classify data and uncover potential data exposures during the free assessment. It was truly eye-opening.”
Michael Smith, CISO, HKS
"What I like about Varonis is that they come from a data-centric place. Other products protect the infrastructure, but they do nothing to protect your most precious commodity — your data."
Deborah Haworth, Director of Information Security, Penguin Random House
“Varonis’ support is unprecedented, and their team continues to evolve and improve their products to align with the rapid pace of industry evolution.”
Al Faella, CTO, Prospect Capital