-
 Cloud Security DSPM Identity Microsoft 365
Cloud Security DSPM Identity Microsoft 365Jul 14, 2025
Multi-Cloud Identity: What to Consider
Learn about enhancing multi-cloud security with authentication, access intelligence, automated remediation, unified monitoring, and compliance best practices.

Daniel Miller
5 min read
-
 Cloud Security Threat Research
Cloud Security Threat ResearchJul 09, 2025
Count(er) Strike – Data Inference Vulnerability in ServiceNow
Varonis Threat Labs discovered a high severity vulnerability in ServiceNow’s platform that can lead to significant data exposure and exfiltration.

Neta Armon
10 min read
-
 Cloud Security
Cloud SecurityJun 30, 2025
Cloud Data Security: Best Practices
Unlock the power of cloud data security: discover tips on access, monitoring, compliance, and more to keep your organization safe and thriving.

Daniel Miller
5 min read
-
 Cloud Security DSPM
Cloud Security DSPMJun 25, 2025
A DSPM-First Approach to Kubernetes Security
Unlock true Kubernetes security with DSPM to discover, classify, and protect sensitive data where CSPM falls short.

Daniel Miller
2 min read
-
 Cloud Security Threat Research
Cloud Security Threat ResearchJun 19, 2025
Why Kerberoasting Still Matters for Security Teams
Sometimes the old ones are best... avoided. Explore Kerberoasting and how it remains a relevant attack method.

Simon Biggs
3 min read
-
 Cloud Security
Cloud SecurityJun 12, 2025
Multi Cloud Security: Challenges and How to Solve Them
Uncover powerful strategies to protect multi cloud setups. Solve fragmented visibility, inconsistent policies, growing attack surfaces, and compliance woes.

Daniel Miller
3 min read
-
 Cloud Security
Cloud SecurityMay 13, 2025
Exploring Infrastructure as Code: A Technical Deep Dive
See how Infrastructure as Code (IaC) enhances security, streamlines operations, and optimizes infrastructure management.

Daniel Miller
2 min read
-
 AI Security Cloud Security Microsoft 365
AI Security Cloud Security Microsoft 365May 07, 2025
Enhancing Proactive Security Across SaaS Applications
Discover powerful strategies to secure SaaS apps, Microsoft 365, and AI tools like Copilot. Uncover how to safeguard your data and elevate cloud security.

Daniel Miller
3 min read
-
 Cloud Security Threat Research
Cloud Security Threat ResearchMay 06, 2025
Does AZNFS SUID your needs? A Path to Root Privilege Escalation on Azure AI and HPC Workloads Using an Azure Storage Utility
Discover how a critical bug in AZNFS-mount could let attackers escalate privileges — and why updating to version 2.0.11 is vital for securing Azure Storage.

Tal Peleg
3 min read
-
 Cloud Security
Cloud SecurityApr 25, 2025
Unlocking the Secrets: Ransomware in AWS S3 with SSE-C Encryption
Uncover the secrets of ransomware attacks on AWS S3 with SSE-C encryption. Learn how to safeguard your cloud data from emerging threats.

Daniel Miller
4 min read
-
 Cloud Security Threat Research
Cloud Security Threat ResearchApr 15, 2025
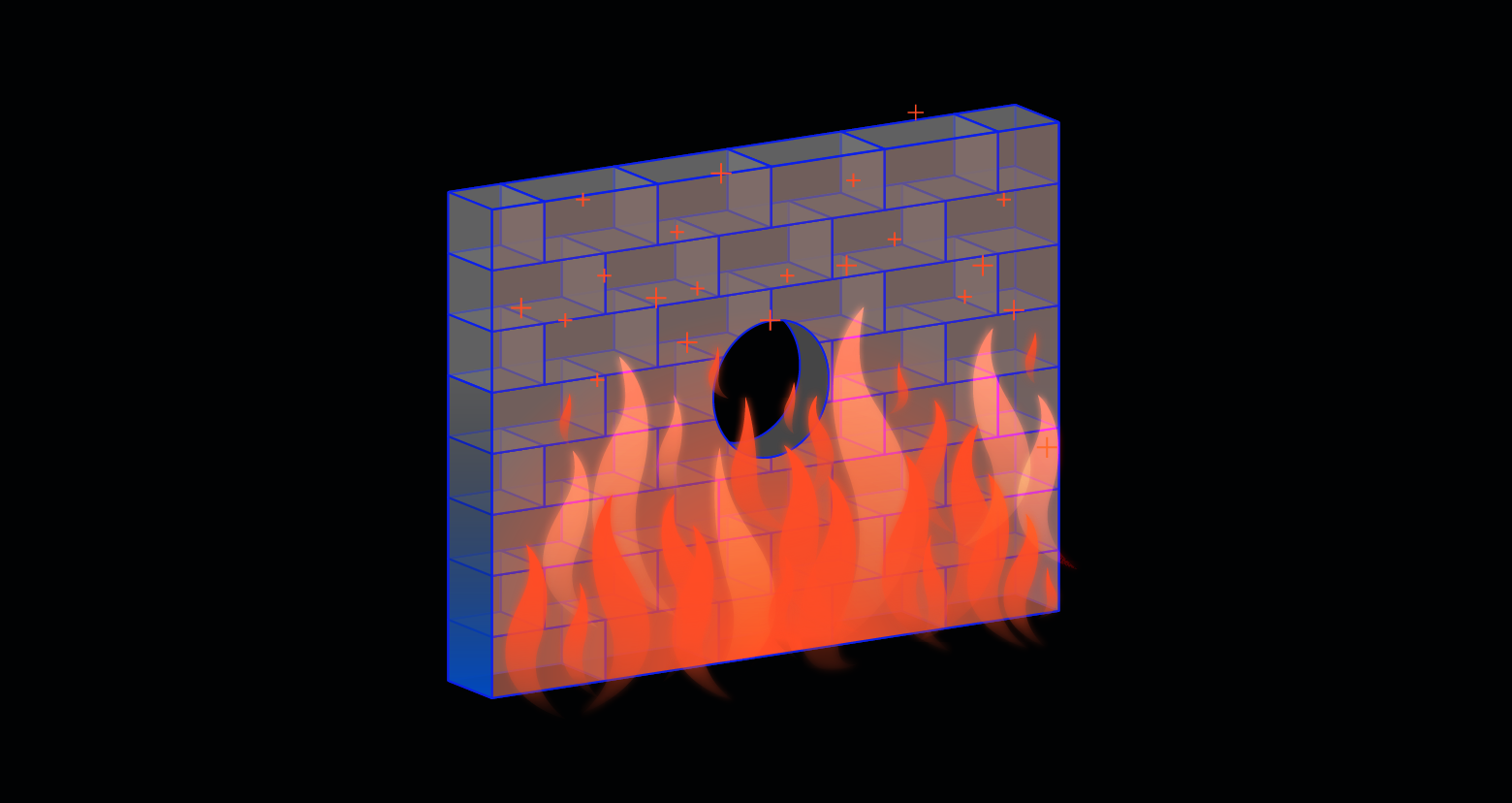
Burning Data with Malicious Firewall Rules in Azure SQL Server
Exploiting a security gap in firewall rule-naming can suddenly delete entire servers and targeted assets when combined with admin actions.

Coby Abrams
4 min read
-
 Cloud Security Threat Research
Cloud Security Threat ResearchApr 15, 2025
Avoid Getting Burned: Identifying and Correcting Common Misconfigurations in Azure Networking and Firewalls
Misconstruing the nuances of Azure Networking and Firewalls can result in security gaps and data exposure.

Coby Abrams
4 min read
SECURITY STACK NEWSLETTER
Ready to see the #1 Data Security Platform in action?
Ready to see the #1 Data Security Platform in action?
“I was amazed by how quickly Varonis was able to classify data and uncover potential data exposures during the free assessment. It was truly eye-opening.”
Michael Smith, CISO, HKS
"What I like about Varonis is that they come from a data-centric place. Other products protect the infrastructure, but they do nothing to protect your most precious commodity — your data."
Deborah Haworth, Director of Information Security, Penguin Random House
“Varonis’ support is unprecedented, and their team continues to evolve and improve their products to align with the rapid pace of industry evolution.”
Al Faella, CTO, Prospect Capital