Developed by renowned analyst John Kindervag, Zero Trust is a strategic cybersecurity model that protects critical systems and data. Systems operating under a Zero Trust framework do not initially trust access or transactions from anyone — including internal users behind the firewall — and limit data access to minimize the blast radius of a cyber attack.
The Zero Trust architecture is widely regarded as the most effective approach to preventing data breaches. So much so that the federal government enacted an executive order on improving the nation's cybersecurity, requiring federal agencies and contractors to begin strengthening their cybersecurity defenses and implement a Zero Trust security model. Because of the increase in cyber threats and attacks on vital defense and infrastructure, the order also strongly recommends the private sector follow suit.
Interest in Zero Trust has risen as organizations now have their data strewn across SaaS applications, cloud services, and on-premise networks. In that type of data environment, where no actual perimeter exists, the Zero Trust model shines as the most effective way to manage and secure data.
Implementing Zero Trust gives organizations visibility into their data and the activity around it, making it easy to spot suspicious behavior, even if there has been a breach of other security controls. Here's everything you need to know about Zero Trust, including its benefits, limitations, and how to implement this framework in your organization.
- What is a Zero Trust architecture?
- How Zero Trust works
- Three principles of Zero Trust
- Implementing Zero Trust
- Benefits of Zero Trust
- Limitations of Zero Trust
Get a Free Data Risk Assessment
What is a Zero Trust architecture?
Zero Trust definition:
Zero Trust is a maturity model that places data security controls first and location-centric access rights second. By requiring all requests (regardless of origination ) to be authorized, authenticated, and continuously validated against data controls, a higher level of security can be achieved.
Unlike traditional network security approaches that focus on keeping attackers and cybersecurity threats outside of the network, Zero Trust follows strict identity verification guidelines for every user and device that attempts to access an organization's resources on a network, even if it's an employee, user, or device within the perimeter. This model assumes that an organization's network will be compromised or the perimeter will fail, challenging all users and devices to prove that they're not attackers.
Zero Trust also limits a user's access from inside a network. This means that if an attacker has compromised a user account, they won't be able to move about within a network's applications.
While traditional perimeter networks leverage firewalls, email gateways, and access controls by building multiple layers of security around a network's perimeter, these security approaches are far more susceptible to attacks from users and devices inside the network.
How Zero Trust security works
Zero Trust's purpose:
Zero Trust security is a holistic approach that involves multiple technologies and processes. Zero Trust security aims to protect organizations from advanced threats and data breaches while assisting in compliance with FISMA, HIPAA, GDPR, CCPA, and other core data privacy or security laws.
At the heart of Zero Trust is data security. Data is what hackers are after. This includes data such as personally identifiable data (PII), protected health information (PHI), payment card information (PCI), intellectual property, and other data organizations consider valuable. Zero Trust makes data activity monitoring a priority.
To build the best Zero Trust security strategy, you'll want to focus on these areas:
- Data: A Zero Trust approach starts by protecting data first and then building additional security layers. If an attacker can breach your perimeter controls, exploit a misconfiguration, or bribe an insider, they would have minimal access to valuable data under Zero Trust because rules will be in place to detect and respond to abnormal data access before it becomes a significant breach.
- Networks: Attackers must be able to navigate your network to steal data, but Zero Trust networks make that extremely difficult. By segmenting, isolating, and restricting your network with technology like next-gen firewalls, your Zero Trust network will be much more resistant to hackers and cybercriminals.
- Users: Humans are likely the weakest link in your security strategy. Limit, monitor, and strictly enforce how users access resources on internal and external networks. Verify all user activity on your network before trusting users with access. Monitor users to protect against infrequent but inevitable human mistakes. Whether falling victim to a phishing attack or a proactive malicious insider, a Zero Trust concept for users is critical.
- Workloads: Workload simply means the entire stack of applications and back-end software that enables customers to interface with your business. Unpatched customer-facing applications are a common attack vector. Treat the whole stack — from storage to the operating system to the front-end web interface — as a threat vector and protect it with Zero Trust compliant controls.
- Devices: The number of devices that live on networks has exploded over recent years. From smartphones and PCs to connected IoT devices, each instrument represents a potential entry point attackers might exploit. To create a Zero Trust environment, security teams should isolate, secure, and control every device on a network.
- Visibility and analytics: To enforce Zero Trust principles, empower your security and incident response teams with complete visibility of your IT environment, including network and file activity. You can then employ advanced threat detection and user behavior analytics to stay on top of any potential threats in your network to identify abnormal behavior in real-time.
- Automation and orchestration: Automation helps keep your Zero Trust security systems running and consistently enforcing policies. Humans cannot keep up with the volume of monitoring events necessary to enforce Zero Trust. Automate as much of your remediation, monitoring, and threat-detection systems to save your security and operations teams time and bandwidth.
Three principles of a Zero Trust architecture
Adhering to the three core principles of the Zero Trust security model forms the foundation of creating your Zero Trust cybersecurity environment.
1. Require secure and authenticated access to all resources.
The first main principle of Zero Trust is to authenticate and verify access to all resources. When a user accesses a file share, application, or cloud storage device, re-authenticate that specific user's access to the resource in question.
You must assume that every attempt to access your network is a threat until confirmed otherwise, regardless of the location of access or hosting model. To implement this set of controls, use measures like remote authentication and access protocols, perimeter security, and network access controls.
2. Adopt a least-privilege model for access control.
The least-privilege access model is a security paradigm limiting a user's access only to the spaces and resources essential to performing their job. Limiting individual user permissions prevents attackers from gaining access to large amounts of data via a single compromised account. By restricting access to data, you essentially create micro-perimeters around data, limiting cybercriminals' ability to access sensitive data.
The first step is to discover where you have sensitive data. Then identify where that data is exposed to too many people or to people who don't need access. The next step is to remediate over-permissive access, which is a challenging but worthwhile task. Create new groups and assign data owners to manage the groups and use them as a means to implement least-privileged access.
Audit access and group memberships on a regular schedule put data owners in charge of who can access their data. For example, ensure your IT team doesn't somehow have access to the finance team's data and vice versa.
3. Inspect and log every network and file event.
Zero Trust principles require inspection and verification of everything. But logging every network call, file access activity, and email transmission for potential malicious activity is a significant undertaking that will take a combination of staffing and smartly deployed technology.
Monitoring and logging are arguably the most important principles of maintaining Zero Trust. With monitoring and data security analytics in place, you can tell the difference between a normal login and a compromised user account; you'll know that a ransomware attack is in progress or if a malicious insider is trying to upload files to their cloud drive.
This level of cybersecurity intelligence is challenging to achieve. Most tools in this category require you to code overly complicated rules, or they generate a significant number of false positives. The right system will use individualized baselines per user account and detect abnormal behaviors based on perimeter telemetry, data access, and user account behavior.
Implementing a Zero Trust model
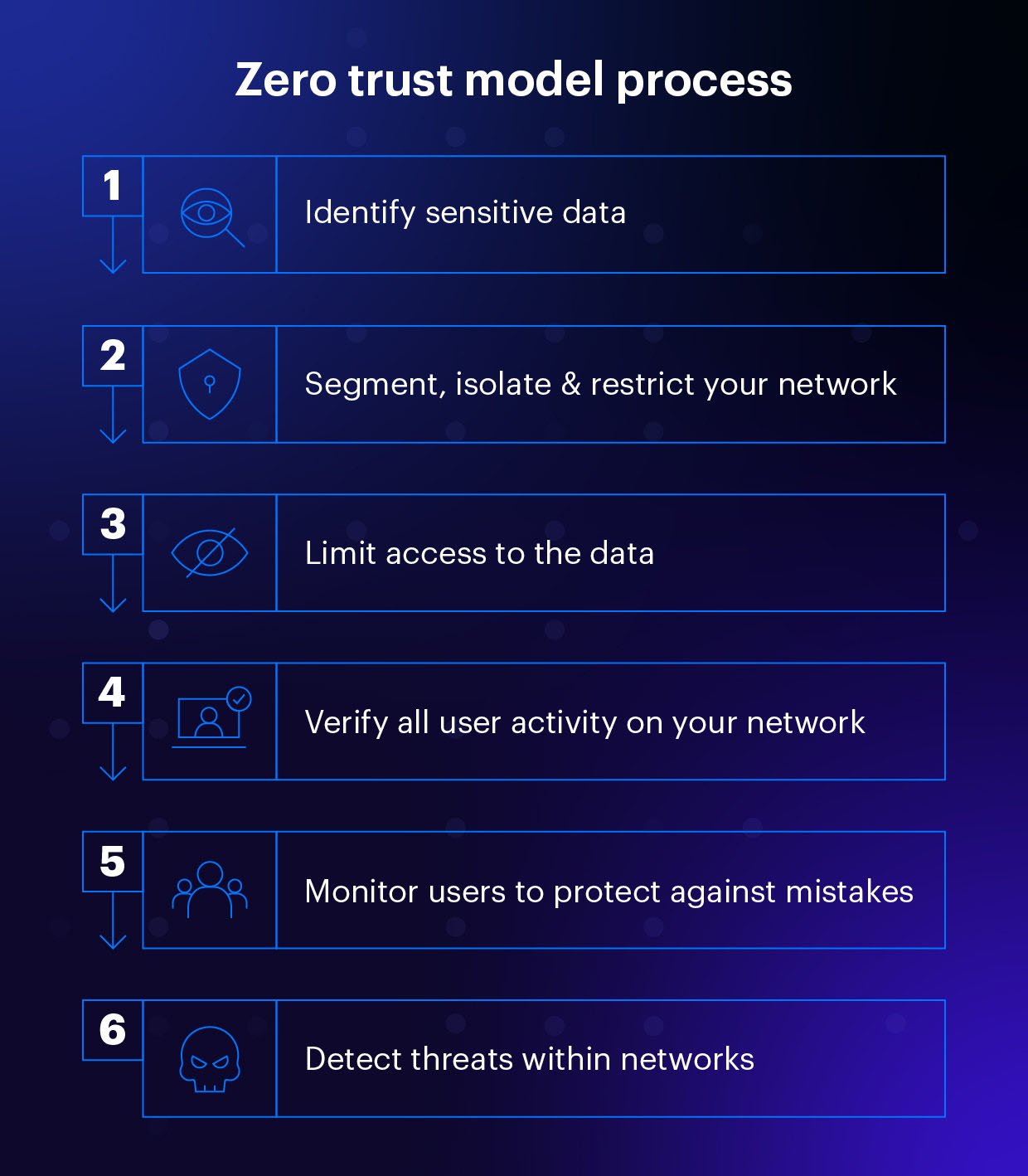
Zero Trust starts with data. Here are some key recommendations for where to start and how to protect your data within the Zero Trust framework.
- Identify Sensitive Data. Figure out where your sensitive data lives. This could be internal departmental folders or places where you store PII or PHI. You need to know where your sensitive data lives and who has access to it before implementing the right Zero Trust protection measures.
- Limit Access. Once you've identified your sensitive data, ensure that only the people who need access have it. This will limit sensitive data exposure and make it more challenging for hackers to gain access to it. You'll want to audit your access permissions on the individual, group, and organizational levels.
- Detect Threats. Finally, you need to detect when suspicious activity is happening with your data or networks. Continuously monitor and log all activity related to data access, including active directory, file and share access, and network perimeter telemetry. Compare the current activity to baselines of prior behavior and apply security analytics and rules to detect abnormal activity that may indicate active cybersecurity threats from internal or external sources.
Benefits of Zero Trust
Implementing Zero Trust can benefit your organization in many ways. Here are some of the core benefits.
1. Greater network and system visibility
Because Zero Trust never assumes that any device or user is trusted, you can decide what resources and activities need coverage in your security strategy. Optimally, all data and computing sources should be protected. Once the proper monitoring is installed to cover resources and activity under a Zero Trust framework, you'll have even more visibility into system activity. You'll now know every access request's time, location, and application involvement and be better equipped to flag and respond to suspicious activity.
2. A more secure remote workforce
Remote work has exploded in the past two years, and with the growing work-from-home workforce, concerns abound. As users and devices access critical data from across the globe and outside the physical workspace, employing Zero Trust helps ensure the security of a distributed workforce.
Zero Trust goes above and beyond traditional firewalls and security measures that aren't necessarily adequate in a remote work environment. Under Zero Trust, identity is attached to users, devices, and applications seeking access, offering robust protection for work and data in any location.
3. Effective ongoing compliance
Zero Trust helps ensure continuous compliance across multiple industries and regulatory frameworks. Every access request being evaluated and logged is a considerable aid in compliance documentation. Tracking the time, location, and applications involved in each access request creates a seamless and transparent audit trail.
With continuous compliance, audits are streamlined as there is a visible chain of evidence for all access requests. This minimizes the effort required to produce evidence, making governance operations faster and more efficient.
Limitations of Zero Trust
It's important to remember that Zero Trust isn't simply a magic bullet in cyber defense. Below are potential limitations that you should be aware of when implementing a Zero Trust model.
1: Coping with BYOD trends and workplaces
In the era of bring-your-own-device (BYOD) policies and environments — along with the "always-on" mentality of many remote employees — organizations need to allow for greater flexibility when it comes to data and system access. Each device has its own properties, requirements, and communication protocols, which need to be tracked and secured under the Zero Trust model. While this is more than feasible, it may require more legwork upfront to configure your Zero Trust security measures in a workplace that relies heavily on BYOD.
2: Accounting for the high number of applications
Another challenging factor to consider when adopting Zero Trust is the number of communication and collaboration applications you use across the organization. You're likely employing versatile and flexible cloud-based apps, but a high number of applications in use can make implementing Zero Trust an uphill battle. Consider what third parties are handling your data, how it's being stored, and whether or not each application is necessary before placing 100+ applications in your tech stack that will all need to be monitored and secured under Zero Trust standards.
3. Authentication doesn't discern the intention
Unfortunately, even if users are fully authenticated, Zero Trust can't determine their intentions. Malicious insiders seeking to damage their own organization may still be able to with the data or systems they are authorized to access. The same principle holds for public-facing web applications. Certain users may sign up for accounts, provide the correct information, and gain proper access. But that doesn't mean that they don't have malicious intentions of compromising systems or data with what access they gain.
Closing thoughts
Because of evolving cybersecurity threats, an increase in remote work, and the explosion of BYOD and IoT, the Zero Trust framework will continue to grow. Taking a data-first approach to security is essential to Zero Trust. The more organizations know where their most sensitive data exists, who can access it, and what they're doing with it, the more effective their defenses can be against today's sophisticated threats. By implementing a Zero Trust architecture, you'll limit the blast radius and damage of a potential cyberattack and take steps toward cybersecurity compliance.
What should I do now?
Below are three ways you can continue your journey to reduce data risk at your company:
Schedule a demo with us to see Varonis in action. We'll personalize the session to your org's data security needs and answer any questions.
See a sample of our Data Risk Assessment and learn the risks that could be lingering in your environment. Varonis' DRA is completely free and offers a clear path to automated remediation.
Follow us on LinkedIn, YouTube, and X (Twitter) for bite-sized insights on all things data security, including DSPM, threat detection, AI security, and more.



-1.png)