Whether you're trying to prevent a breach or meet regulatory requirements — both broader laws like GDPR, as well as regulations specific to your area (CCPA) or industry (HIPAA), protecting your company's data is increasingly difficult as more and more data is created across your organization. It’s important to have the right tools in place to make this as easy and scalable as possible for you.
While a good DSPM can address these challenges, not all DSPM solutions deliver the same outcomes.
Why is DSPM important?
DSPM is designed to protect sensitive data and ensure compliance with regulations across modern environments, including SaaS, cloud-based, and on-premises platforms.
The primary objective of DSPM is to secure sensitive data wherever it resides by combining data discovery, classification, access analysis, and continuous monitoring. Effective DSPM applies these measures in context—connecting data sensitivity with identities, permissions, and activity to understand true risk.
Organizations are rapidly adopting DSPM solutions for three main reasons:
Breach avoidance
As a CISO, it's your responsibility not only to protect against breaches, but also to clearly demonstrate to leadership how risk is being reduced.
This applies equally to SOC analysts and GRC teams. You need to assure stakeholders data security is under control.
But this is an uphill battle. Users create more data every day, and with cloud collaboration and sharing, data exposure tends to increase. AI is only compounding the problem. AI-created data is expected to surpass human-created data in the next three years, according to IDC Global.
If an employee decides to exfiltrate sensitive data, how would you know? If an attacker compromises a user or AI agent, would you have an audit trail to identify exactly what data was affected?
There are two sides of breach avoidance that are important to consider:
- How can I quickly detect suspicious behavior that could lead to a data breach?
- If an attacker gains access—whether external or an insider—how can we limit the damage?
- DSPM solutions should use data-activity monitoring to detect breach activity early and provide access control capabilities to proactively limit the damage a bad actor could do.
Post-breach
Sometimes, despite best efforts, a breach occurs. When that happens, security teams must be able to answer critical questions quickly:
- How did it happen?
- What data was accessed or stolen?
- How can we prevent it from happening again?
The worst possible answer during an incident is “I don’t know.”
Even the best investigators in the world need the right visibility. The best DSPM solutions provide a complete audit trail across SaaS, cloud, and on-prem environments—showing exactly which data was accessed, by whom, and how—so teams can confidently assess impact and respond.
Compliance
Another vital reason for using a DSPM solution is to ensure compliance and prove it.
From GDPR to HIPAA to SEC requirements, every company has data laws and regulations it must adhere to. Most regulations can be broken down into knowing where sensitive data is, limiting who can access it, and monitoring it for threats.
You're accountable not only to leadership, but also to auditors who expect clear evidence that sensitive data is being protected.
For example, healthcare organizations must regularly demonstrate HIPAA compliance, ensuring sensitive data is accessible only to authorized users. Failure to do so can result in penalties reaching millions of dollars.
By reducing data exposure and continuously monitoring access, DSPM becomes a foundational control for meeting compliance requirements.

Picking the right DSPM solution
Considering the significant impact this could have on your company, it's clear that it's not just important to use any DSPM solution. Effective DSPM requires understanding sensitive data in context—combining classification, effective access, and real-time activity.
If any of these elements are missing, risk cannot be accurately assessed and automated remediation becomes impossible.
As the DSPM market expands, there are several key areas to evaluate carefully.
Coverage
One of the first questions to ask is where your organization stores its most sensitive data—and where that data is most exposed.
For many organizations, this includes platforms like Microsoft 365, AWS, Salesforce, Box, Google Drive, GitHub, etc.
Of course, you'll want to choose a tool that covers your most used platforms. However, while broad platform support is important, coverage alone isn’t enough.
Many DSPM solutions focus primarily on IaaS storage, ignoring SaaS and file environments where sensitive data is most actively accessed and shared. Sensitive data sprawls across SaaS and IaaS storage platforms alike, and the more collaborative the platform, the higher the risk of exposure.
Our philosophy at Varonis is to focus on the platforms where our customers have most of their sensitive data (Google Drive, Microsoft 365, Salesforce, etc.) and provide deep coverage for those specific tools.
Accuracy
Accuracy is also essential when dealing with risk findings.
If a DSPM solution surfaces inaccurate or misleading results, trust erodes quickly—and security teams are forced to manually validate findings, defeating the purpose of automation. Additionally, false positives lead to alert fatigue and stalled remediation.
Instead, look for DSPM solutions that provide complete, contextual, and current insights with behavioral baselining and anomaly detection rather than relying on static rules.
The ability to tune findings and prioritize true risk is critical to optimizing the signal-to-noise ratio.
Scale
There's a huge difference between auditing a few terabytes and securing petabytes of enterprise data. This is why scale is such an important factor and can cause a lot of problems if the DSPM solution isn't built for it.
Sampling and periodic scans may work in limited scenarios, but ultimately, they result in an incomplete view of the data. Sampling and periodic scans create blind spots by design, making it impossible to maintainaudit-grade compliance, enforce precise policies, and respond effectively to a breach.
Remediation
The point of finding risk is to eliminate it.
Passive DSPM vendors surface problems. Outcome-driven DSPM solutions, like Varonis, fix them.
Built-in, automated remediation means issues can be resolved at the push of a button, or sometimes even without any action at all. It allows organizations to remove excessive access, fix misconfigurations, and enforce least privilege continuously—without manual tickets or third-party workflows.
A data-first approach with Varonis
At Varonis, our goal isn’t to overwhelm teams with findings. Instead, we deliver measurable security outcomes.
Even when you’re not logged in, Varonis continuously discovers risk, fixes exposure, and monitors activity across your data estate.
Real-time visibility
It's important to see the status of your data, as it exists right now.
This not only keeps you up to date but also enables proactive risk reduction in fast-changing SaaS, cloud, and hybrid environments.
Varonis delivers real-time, contextual visibility with several features and functions.
Continuous data discovery
Varonis is constantly scanning your data, stored both on-premise and in the cloud, even surfacing instances that you may not know you had.
You can then view the results of these scans on real-time dashboards, showing discovery insights, concentrations of sensitive data, and where that data is exposed.
This provides a complete, current, and contextual view of data risk, making it easy to digest insights and prioritize remediation.
Automated data classification
A key part of staying compliant is being able to see exactly what sensitive data is stored and where.
Varonis combines AI classification, sophisticated pattern matching, and exact data matching to accurately classify your data and drastically reduce false positives.
This includes all common regulations and standards like GDPR, SOX, PCI, and HIPAA.
On-demand compliance reports help you track compliance with relevant regulations and can be shared directly with auditors and compliance teams.
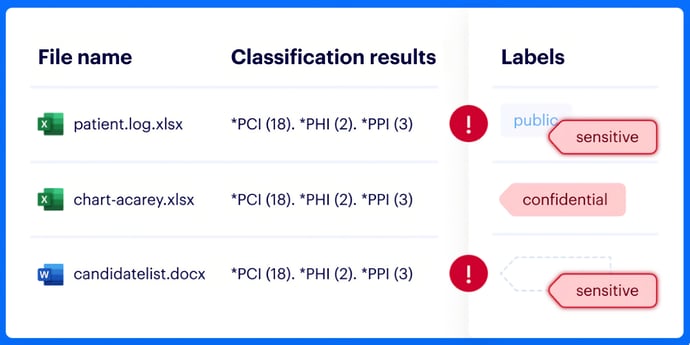
Sensitivity labels
Instead of manually labeling data, you define policies, and Varonis applies and maintains labels automatically.
If a policy changes, data that no longer matches the policy will be automatically relabeled.
Varonis also compares existing labels with classification results to identify misclassified data.
Simplify permissions management
In addition to understanding data sensitivity, it’s critical to know who can actually access sensitive data.
Varonis maps permissions across data stores and normalizes them into a simplified permissions model, making it easier to understand exposure without being an expert in every platform’s permission model.
We correlate classification results with permissions to identify stale permissions and where data is exposed org-wide, externally, and publicly.
Reduce your blast radius
Reducing blast radius means understanding how identities, permissions, and activity intersect with sensitive data. By correlating people with permissions and activity, you can identify where sensitive data is overexposed and at risk. This enables proactive decisions that limit how much damage any compromised identity can cause.
Varonis analyzes data access and activity across the organization and can automatically remove excessive, external, public, and stale permissions without disrupting business operations.
You can use ready-made policies or tailor them to your organization. Once configured, Varonis automatically and continuously enforces your new rules, keeping your data as secure as possible.
Least privilege automation
DSPM only delivers real value when it actively reduces exposure.
Least privilege automation continuously analyzes data access across environments, and intelligently decides who needs access to what data.
This reduces blast radius automatically, without manual workflows and without introducing business risk.
Threat detection and response
Our behavioral-based threat models are refined using large datasets, which means they are accurate and improve over time as we analyze more data.
By baselining normal behavior across users, service accounts, and applications, Varonis detects abnormal activity and triggers automated responses to stop threats before data is exfiltrated.
Audit trail of events
Managing investigations can be overwhelming without the right context. Varonis aggregates, normalizes, and enriches events across data stores, identities, and platforms.
Our searchable data activity log makes it easy to investigate incidents, whether by your team or ours. Search for resources, folders, emails, and objects, and see everything that's been created, updated, uploaded, or deleted.
Events are enriched with contexts like device name, geolocation, and identity to make it even simpler and help you make better decisions.
Incident response team
Varonis provides proactive monitoring and response through managed data detection and response (MDDR) to help investigate and contain threats as soon as they emerge.
We watch your data so you don’t have to and partner with your team to investigate incidents and stop breaches.
Posture management
Varonis proactively surfaces misconfigurations that could expose sensitive data to risk. The Varonis posture management dashboard explains the risk each misconfiguration poses and enables remediation directly from the Varonis UI— strengthening your data security posture without manual effort.
Third-party app risk management
With Varonis, security teams can easily discover all the third-party apps connected to their corporate SaaS platforms and gain a clear view of the risks they pose.
We identify each app's blast radius, monitor app activity, and reduce the attack surface by removing unsanctioned or unused app connections — right from a single console.
Connect cross-cloud identities and close off-boarding gaps
Varonis automatically links user accounts, including personal accounts, across all your services into a single identity. These insights help security teams safely offboard ex-employees and contractors, uncover shadow identities, and reduce identity based risk across cloud environments.
DSPM dashboards
By combining your classification results, permissions, and user access activity, Varonis provides a comprehensive and centralized view of your data with out-of-the-box and customizable dashboards.
The Varonis DSPM dashboards can serve as your organization's real-time view of data risk. Use these dashboards to continuously visualize and assess your security posture and track progress over time.
See where there are unnecessary pathways to data and monitor changes to risk over time so you can reduce threats to your sensitive data as your environments evolve.
DSPM delivers real security outcomes
For organizations prioritizing data security, DSPM is a concept to pay attention to.
Choosing the right DSPM solution can reduce exposure, prevent breaches, accelerate investigations, and simplify compliance. By focusing on coverage, accuracy, and scale, organizations can distinguish passive DSPMs from outcome driven platforms and select the best solution for their company.
We are confident that our DSPM features are the best in the market, and deliver true value across four areas:
- Real-time visibility
- Simplify compliance
- Reducing the blast radius
- Threat detection and response
Curious to learn more? Explore the DSPM features built into our Data Security Platform to see how automated DSPM delivers real security outcomes.
What should I do now?
Below are three ways you can continue your journey to reduce data risk at your company:
Schedule a demo with us to see Varonis in action. We'll personalize the session to your org's data security needs and answer any questions.
See a sample of our Data Risk Assessment and learn the risks that could be lingering in your environment. Varonis' DRA is completely free and offers a clear path to automated remediation.
Follow us on LinkedIn, YouTube, and X (Twitter) for bite-sized insights on all things data security, including DSPM, threat detection, AI security, and more.






-1.png)

