Data security posture management is a multi-faceted practice that requires a single source of truth.
Security teams are increasingly challenged to mitigate data security and privacy risks across their hybrid and multi-cloud environments. They need to know where sensitive data lives and if it’s exposed — whether that’s through excessive permissions, misconfigurations, offboarding gaps, etc.
A customizable DSPM dashboard allows organizations to easily assess their data security posture with an intuitive interface.
TL;DR
- DSPM dashboards centralize data risk visibility.
- They focus on data, not infrastructure.
- They identify exposure, misconfigurations, and risky behavior.
- Customization prioritizes relevant risks and indicators.
- Role-based access limits dashboard visibility
Core concepts: DSPM dashboard
A data security posture management (DSPM) dashboard is a way for security teams to understand data risk across their environment from a single view. Rather than focusing on infrastructure or perimeter defenses, a DSPM dashboard centers on where sensitive data lives, who can access it, and how that risk changes over time.
This data-centric perspective differs from infrastructure-level views. Infrastructure dashboards typically focus on assets, configurations, and system health. DSPM dashboards focus on data sensitivity, exposure, and access paths, regardless of where the data is stored.
What can a DSPM dashboard do?
Easily spot risks such as:
- Sensitive data exposure: See exactly where PII, PHI, and other regulated data is concentrated and overexposed org-wide, externally, or even to anyone on the internet.
- Misconfigurations: Assess security posture across SaaS apps and get recommendations for how to reduce your attack surface and eliminate pathways to sensitive data.
- Suspicious data activity: Get alerts of abnormal behavior, such as accessing an excessive number of Salesforce account records, or when we see risk activity like external users added to internal Slack channels, or sensitive GitHub repos made public.
- Policy violations: Identify policy violations, such as terminated contractors accessing data or admins logging in without MFA.
- Stale and risky identities: Surface stale users and offboarding gaps of current data access that is no longer needed.
- Suspicious privileged account activity: Get enhanced monitoring for privileged accounts.
Continuous risk requires continuous assessment
Security measures need to be every bit as dynamic as the threats they’re protecting against. New data is created daily, and users gain or lose access as roles change. A single sharing or permission change can significantly increase exposure. Continuous assessment ensures these changes are evaluated as they happen.
Risk emerges outside formal processes. Files are shared, integrations are added, and settings are adjusted without security involvement. Continuous assessment helps surface these risks even when they occur outside formal workflows.
Context is required to assess risk. Access to sensitive data is not inherently risky. Risk depends on context, including data sensitivity, user role, and behavior over time. Ongoing assessment provides the context needed to evaluate whether activity is expected or concerning.
Timing limits impact. The sooner data risk is identified, the easier it is to contain. Continuous assessment reduces the gap between when risk is introduced and when it is detected, helping organizations limit exposure before it escalates.
Custom features in the Varonis DSPM dashboard
Simply drag and drop your desired security widgets into a customizable dashboard to monitor the data risks you care most about. This versatile dashboard helps you quickly visualize your data security posture and prioritize risk reduction.
Drag and drop desired widgets onto your custom dashboard.
Drag and drop desired widgets onto your custom dashboard.
Drill into data exposure
See where sensitive and critical data may be at risk — either through excessive sharing or misconfigurations. Drill down from these widgets to get a detailed view of the exact data that is exposed internally, externally, or publicly, see who has access and what their permissions are, and view any activity on that data.
Drill down into exposed sensitive data to see exactly who has access.
Drill down into exposed sensitive data to see exactly who has access.
Dive directly into any critical misconfigurations that open your organization up to risk and use the recommendations provided by Varonis to begin fixing issues before a bad actor can take advantage of them.
Drill down into dashboard widgets to gain additional insight.
Drill down into dashboard widgets to gain additional insight.
Role-based access control
We preach access control, so of course we practice it.
Role-based access is enforced on your custom dashboard. If you have a role that can only view and manage specific aspects of the platform — such as the CRM admin or a security analyst — that user will only be able to see role-relevant data. All other information is hidden.
Assign specific roles to control access in Varonis.
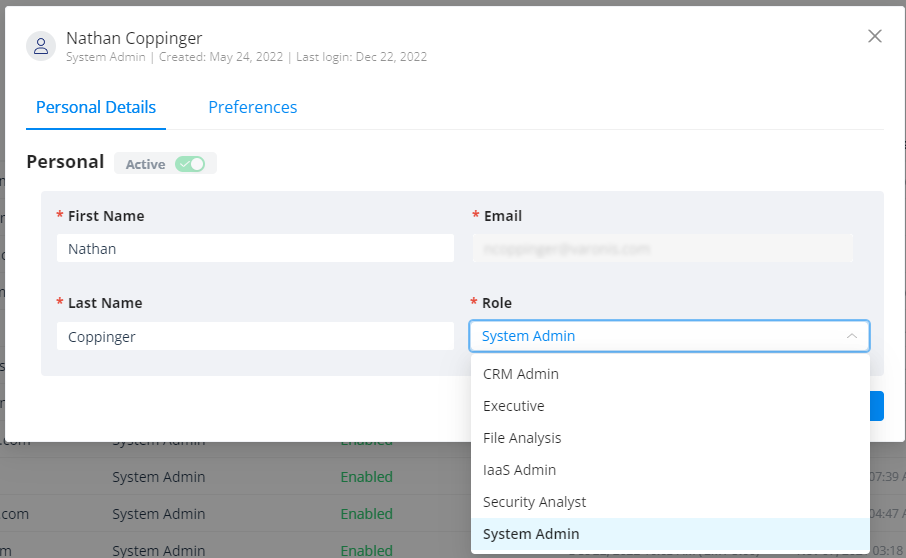
Assign specific roles to control access in Varonis.
Out-of-the-box dashboards
The customizable DSPM dashboard adds to a library of out-of-the-box dashboards in Varonis that monitor specific key risk indicators (KRIs).
Along with our overview dashboard, these pre-built dashboards cover many of the basic KRIs needed to protect data and detect threats.
Data Protection dashboard
The new Data Protection dashboard provides a dedicated view of both sensitive data exposure and risks all in one place.
- Clearly see where you have sensitive data and where it is exposed.
- Monitor sharing to ensure sensitive information doesn’t end up shared with the entire organization, or even the entire internet.
- See recommendations for where your configurations could be improved to close security gaps.
Varonis tracks data exposure across your SaaS environment to give you a continual, real-time view of your data security posture.
Our Data Protection dashboard shows you where your data is exposed from a single view.
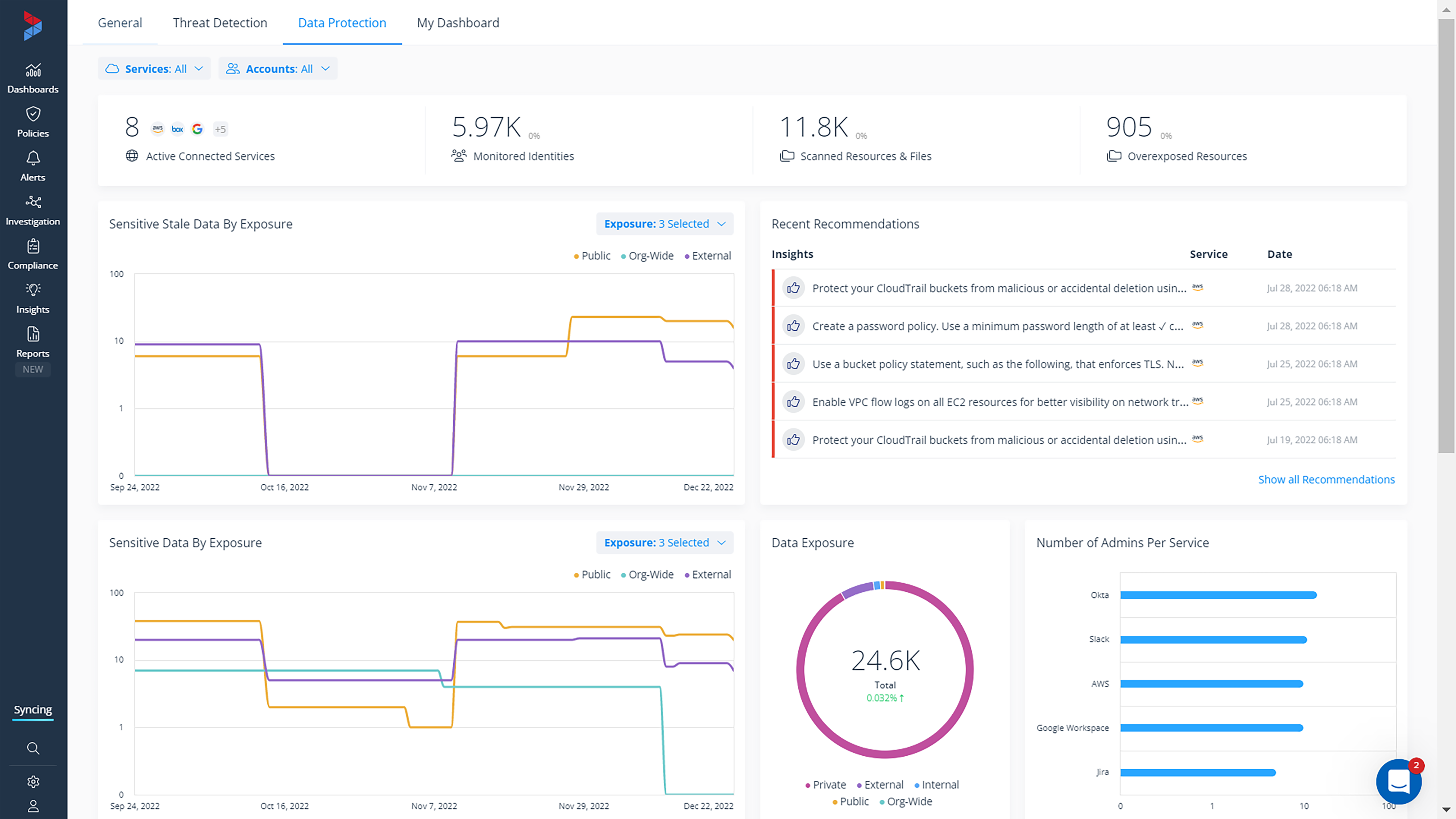
Our Data Protection dashboard shows you where your data is exposed from a single view.
Threat Detection dashboard
The new Threat Detection dashboard provides security admins with a snapshot of everything happening in your environment from a security standpoint. Admins can see their open alerts, policy violations, misconfiguration insights, users triggering multiple alerts, and more — all from a single dashboard view.
Our Threat detection dashboard surfaces potential threats.
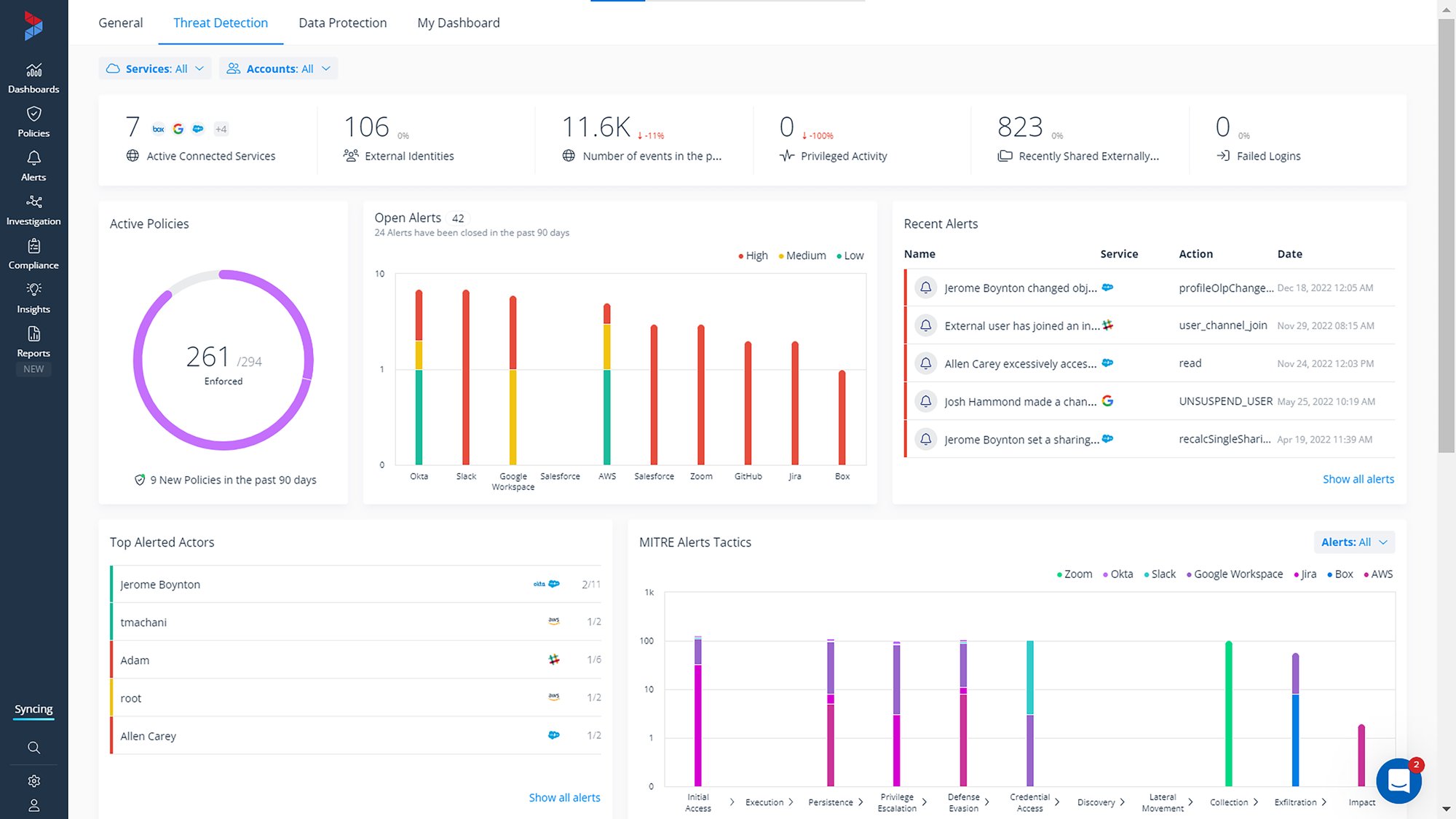
Our Threat detection dashboard surfaces potential threats.
Varonis alerts are mapped to the latest MITRE ATT&CK tactics and techniques and provide a visualization of the most used MITRE tactics we spot in your environment. Admins can use this to understand how threats are potentially infiltrating their environment so they can begin to harden their defenses.
Varonis shows you the number of alerts related to each MITRE ATT&CK tactic.
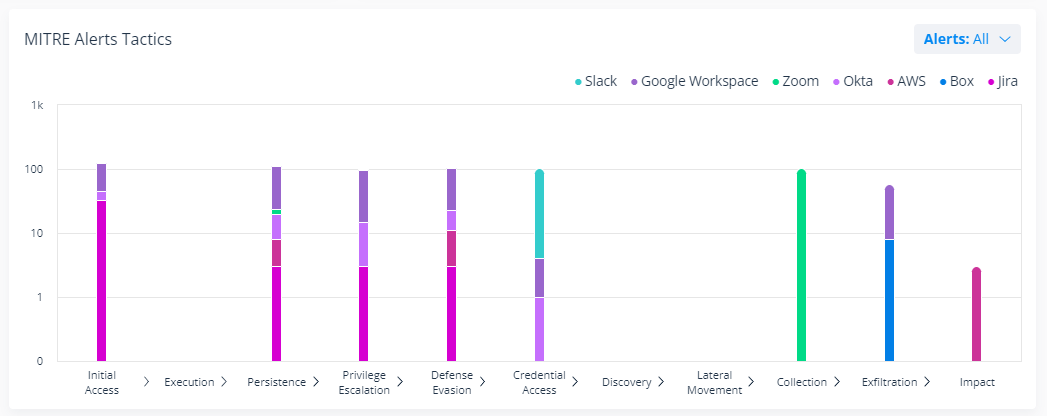
Varonis shows you the number of alerts related to each MITRE ATT&CK tactic.
Get a free Data Risk Assessment
If you’re interested in seeing where your data security posture stands, try Varonis for free. In minutes, we can get you up and running to help you visualize data exposure and sharing risks across critical SaaS and IaaS platforms including Salesforce, AWS, Google Workspace, Box, GitHub, Zoom, Okta, Slack, and Jira.
Reach out today to request a free Data Risk Assessment.
FAQs about DSPM dashboards
What is the primary purpose of a DSPM dashboard?
A Data Security Posture Management (DSPM) dashboard serves as a centralized, real-time interface for visualizing and assessing data risks across hybrid and multi-cloud environments. It enables security teams to identify where sensitive data resides, determine if it is exposed through excessive permissions or misconfigurations, and track remediation progress over time. By aggregating these insights, organizations can continuously monitor their attack surface and prioritize actions to protect regulated information.
Why is it important to have a customizable view of data security posture?
Customization allows users to prioritize high-value assets and evolving threats within their specific SaaS and IaaS infrastructure. This flexibility ensures that the dashboard remains a relevant and effective tool for decision-making as the organization’s data landscape changes.
What types of risks can I track on a customizable security dashboard?
These dashboards allow organizations to monitor a variety of key risk indicators, from sensitive data exposure to critical misconfigurations to suspicious user behavior. Specific widgets can track stale identities, policy violations, and abnormal activities. This visibility helps teams spot vulnerabilities across platforms like Salesforce, AWS, and Google Workspace before they are exploited.
How does role-based access control (RBAC) function within the dashboard?
Role-based access control restricts dashboard visibility so that users only see data and widgets relevant to their specific job responsibilities. For example, a CRM administrator will only view risks associated with their specific platform, while a security analyst may have a broader view of the entire environment. This approach enforces the principle of least privilege, ensuring that sensitive security insights are kept confidential and are only accessible to authorized personnel.
Can the dashboard help with active threat detection?
Yes, advanced dashboards integrate threat detection by providing snapshots of open alerts, policy violations, and users triggering multiple alarms. Alerts can be mapped to industry standards like MITRE ATT&CK tactics to help admins understand how potential threats are attempting to infiltrate the environment. This context allows security teams to drill down into specific incidents and take immediate action to harden defenses against active attacks.
What should I do now?
Below are three ways you can continue your journey to reduce data risk at your company:
Schedule a demo with us to see Varonis in action. We'll personalize the session to your org's data security needs and answer any questions.
See a sample of our Data Risk Assessment and learn the risks that could be lingering in your environment. Varonis' DRA is completely free and offers a clear path to automated remediation.
Follow us on LinkedIn, YouTube, and X (Twitter) for bite-sized insights on all things data security, including DSPM, threat detection, AI security, and more.


-1.png)


.png)
.png)

