Across industries, organizations are deploying chatbots and AI agents, developing AI applications, and leveraging a multitude of AI platforms, models, and agentic frameworks to accelerate productivity and create new product offerings. AI adoption is accelerating faster than security teams can keep up.
While 83% of organizations report using AI, only 13% have strong visibility into how AI interacts with sensitive data. This leaves organizations blind to a new breed of threats.
This shift introduces new threats, such as supply chain poisoning and indirect prompt injection from untrusted repositories, for example, a compromised GitHub repository could trick an agent into exfiltrating secrets or access to codebases.
Gartner®, Emerging Tech: The Future of AI Security Is in Securing Agent Actions, Not Prompts
Most solutions only address isolated risks or focus on discovery alone, resulting in fragmented visibility, reactive controls, and blind spots across AI build and runtime. AI security platforms have emerged to enable organizations to secure everything they build and run with AI across the entire AI data lifecycle.
AI security is fragmented
AI systems introduce new attack surfaces, new threat vectors, and new operational risks that span users, applications, data, and models themselves.
Fundamentally, AI systems are different from the technologies security teams have traditionally protected. They are:
- More dynamic, adapting behavior over time based on inputs, context, and learning
- More scalable, operating at machine speed and volume rather than human pace
- More autonomous, capable of taking actions without direct human initiation
- More connected, integrating with enterprise data stores, APIs, and workflows
These characteristics dramatically increase the blast radius of security incidents while making effective security and governance far more difficult. Security teams struggle to answer critical questions about their organization’s AI usage:
- What sensitive data can AI systems access?
- Are agents and LLMs configured properly?
- Are AI systems behaving abnormally?
- Are AI tools and their usage in compliance with regulations and frameworks?
A new approach
A technical platform approach is necessary because tracking AI usage with committees, policies, and spreadsheets is too manual and unreliable to scale.
A platform doesn’t tackle the problem one aspect at a time. Instead of focusing on creating an inventory of AI systems for example, a platform approach can apply AI security posture management (AI-SPM) to understand vulnerabilities and misconfigurations of each component of the inventory while simultaneously providing AI detection and response (AIDR) capabilities through monitoring. On their own, point solutions don’t scale to keep pace with the growing complexity of AI use. CISO’s and their teams need to have the complete visibility and control layer together.
In its Top Strategic Technology Trends for 2026 report, Gartner writes, “AI adoption has introduced new security risks that traditional tools cannot address. Organizations face threats like prompt injection, shadow AI, and data misuse in both third-party and in-house AI.”
At Varonis, we believe these risks emerge not from isolated failures, but from how AI systems interact dynamically with data, users, and other systems at scale.
What is an AI Security Platform?
Rather than focusing on a single control or risk area, an AI Security Platform (AISP) provides centralized visibility, enforcement, and monitoring across AI systems, data, users, and agents. They complement governance programs by enforcing policies in practice and extending traditional security by addressing AI specific behaviors and risks that legacy tools were never designed to manage.
These platforms are designed to:
- Discover AI usage and deployments across the enterprise
- Assess and manage AI security posture
- Enforce policies and guardrails at runtime
- Detect and respond to AI-related threats
- Provide auditability and governance for compliance
This comprehensive, platform approach evolves AI security from fragmented solutions to an end-to-end approach to the entire AI lifecycle.

Core capabilities of AI Security Platforms
Centralized AISPs focus on a set of foundational capabilities that allow organizations to secure AI across its lifecycle, at scale. According to the 2025 Gartner Top Strategic Technology Trends for 2026: AI Security Platforms,3 “AISP comprises two pillars: AI usage control (AIUC) and AI application security (AIAS). AIUC secures third-party AI usage while AIAS protects custom-built AI applications.”
At Varonis, we believe these two capability areas together address both how AI is used across the organization and how AI systems themselves are secured. This platform level approach reflects the reality that AI risk does not exist in a single layer. It spans users, data, applications, models, and increasingly autonomous agents—all of which must be governed and protected in a coordinated way.
AI usage control
AIUC focuses on how AI services, tools, and capabilities are used across the enterprise. This category is designed to help organizations understand where AI is being used, what it can access, and whether that usage aligns with security, privacy, and compliance expectations.
AIUC capabilities include:
- AI discovery and inventory
- AI access control
- Sensitive data protection
- Risky AI usage detection
- Content moderation
- Automated AI security testing
AI application security
While AI usage control focuses on consumption, AIAS addresses the security of AI systems themselves. This category is concerned with how AI applications are built, configured, integrated, and operated, especially as they become more autonomous and interconnected.
AIAS capabilities include:
- AI discovery and inventory
- AI security posture management
- MCP (Model Context Protocol) security
- Rogue agent detection
- Multimodal security guardrails
- Automated AI security testing
AI security doesn’t exist in a vacuum
Securing AI is no longer about deploying isolated controls. Instead, it requires a unified platform that can connect AI usage to application behavior, data access, and policy enforcement. AI usage alone doesn’t tell the whole story. An AI agent may not appear risky until you understand what data it can access and what controls are in place.
By combining AI usage control, AI application security, and data security within a single platform, organizations can move from fragmented, reactive defenses to proactive protection suited for a world in which AI systems are more autonomous, interconnected, and integral to the business.
Secure AI and the data that powers it with Varonis Atlas
AI security cannot live in silos or point solutions. As organizations scale AI, they also scale their AI blast radius. Taking a unified approach to AI security that understands not only how AI behaves, but also what actions it can take and what data it can access and act upon.
An overview of the Atlas platform's coverage throughout the entire AI security lifecycle.
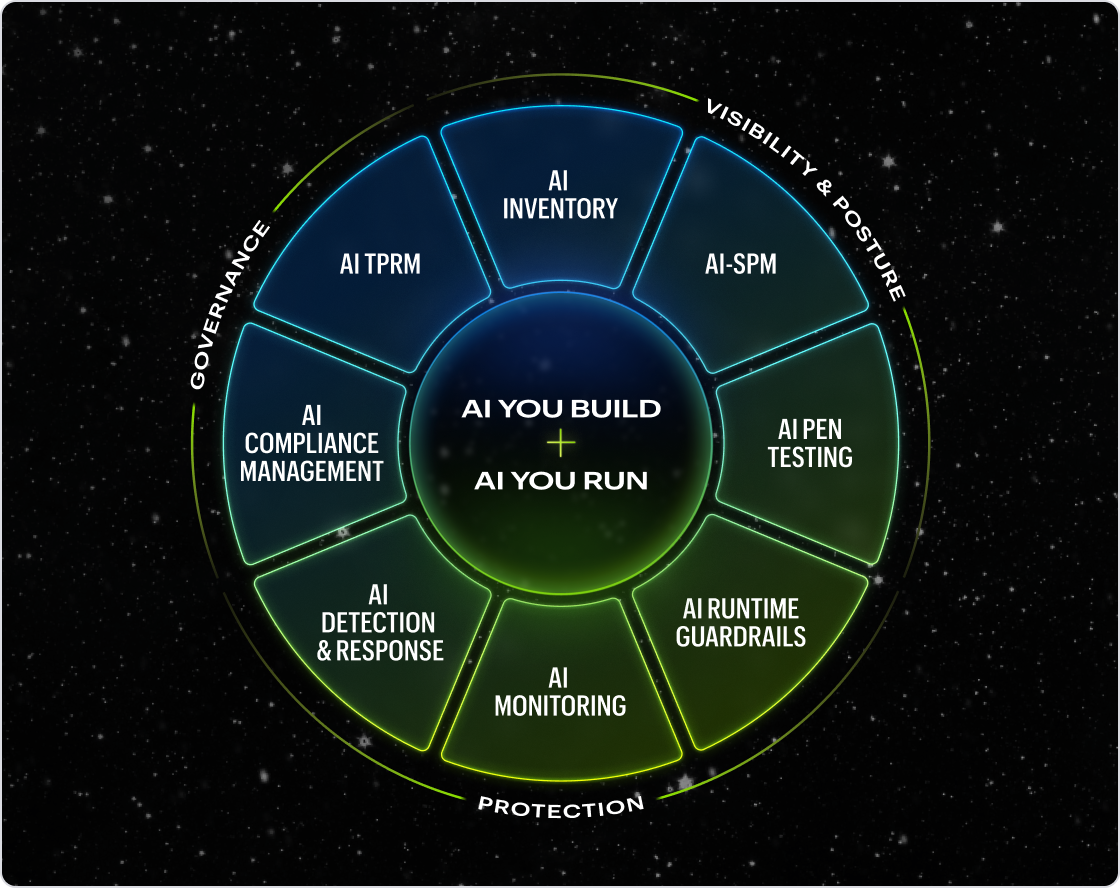
An overview of the Atlas platform's coverage throughout the entire AI security lifecycle.
Varonis Atlas is an end-to-end AI Security Platform that helps organizations see and control AI across the enterprise. Atlas is the only platform that covers the entire AIsecurity lifecycle — from discovery and posture management to runtime protection and compliance — in a single solution. Atlas connects to any AI system organizations build or run, including hosted AI platforms, custom LLMs, agentic frameworks, chatbots, and embedded AI. And because Atlas is built alongside the Varonis Data Security Platform, it brings data context that no standalone AI security tool can match.
Varonis Atlas is available today. Begin with a free trial with full access to Atlas’ AI inventory, posture management, security testing, runtime guardrails, and compliance reporting functionality.
Sources:
- Gartner, Emerging Tech: The Future of AI Security Is in Securing Agent Actions, Not Prompts, Mark Wah, David Senf, February 20, 2026.
- Gartner, Top Strategic Technology Trends for 2026, Gene Alvarez, Bart Willemsen, Frank Buytendijk, Gary Olliffe, Bill Ray, Samantha Searle, Tori Paulman, October 18, 2025.
- Gartner, Top Strategic Technology Trends for 2026: AI Security Platforms, Dennis Xu, Marissa Schmidt, Bart Willemsen, Gene Alvarez, Neil MacDonald, Kevin Schmidt, October 18, 2025.
GARTNER is a trademark of Gartner, Inc. and/or its affiliates.
What should I do now?
Below are three ways you can continue your journey to reduce data risk at your company:
Schedule a demo with us to see Varonis in action. We'll personalize the session to your org's data security needs and answer any questions.
See a sample of our Data Risk Assessment and learn the risks that could be lingering in your environment. Varonis' DRA is completely free and offers a clear path to automated remediation.
Follow us on LinkedIn, YouTube, and X (Twitter) for bite-sized insights on all things data security, including DSPM, threat detection, AI security, and more.








