Any security practitioner that has had to perform forensic analysis on a cybersecurity incident likely describes the process as “searching for a needle in a stack of needles.” Even Tony Stark’s magnet isn’t going to help. Anyone who has used a SIEM or any other monitoring system to figure out how gigabytes of data was stolen knows how difficult that task can be.
Varonis leverages Solr to optimize and streamline the process of analyzing data related to a cybersecurity incident. Solr makes the stack of needles smaller – enabling security teams to analyze incidents faster.
How is Varonis using Solr?
The Solr server is a repository for the most current Varonis log and alert data, making searches in the Varonis WebUI lightning fast. The Varonis WebUI presents the searches in a clean and customizable view that you can filter and narrow down to find the correct needle in that stack of needles.
New events and alerts are available in the Varonis WebUI immediately, and Solr indexes the data as it is received. The Varonis WebUI correlates and contextualizes the data into understandable and actionable alerts, which can combine seemingly unrelated events into a clear picture of a coordinated cyberattack.
The new Solr search engine starts providing data while the search is running. The search field has autocomplete, so you can see possible search parameters as you type, just like in Google. You can save searches, set your favorite filters or queries, and easily access them again in the future.
What are the Advantages of Solr?
Solr is an open-source search optimized database that is used throughout the software industry. With the new WebUI powered by Solr, customers are seeing faster alerts, easier forensic analysis, and quicker query return.
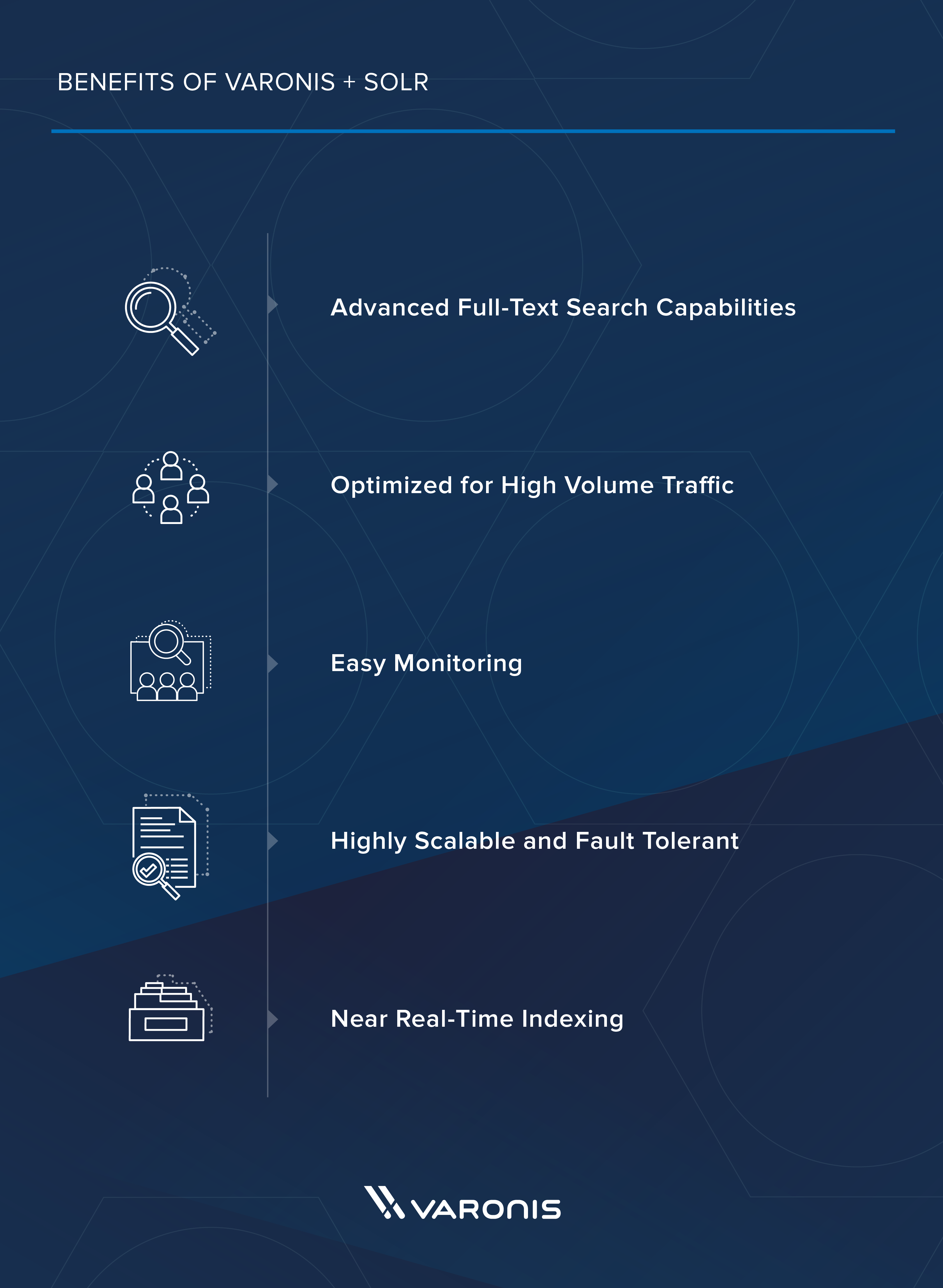
Some of the features of Solr that Varonis uses are:
- Advanced Full-Text Search Capabilities: Solr uses the Lucene search engine to implement powerful and optimized searching and indexing
- Optimized for High Volume Traffic: Solr has proven its capability to operate at extremely large scales all over the world
- Easy Monitoring: Solr includes self-monitoring tools via Java Management Extensions (JMX) for system performance and uptime monitoring
- Highly Scalable and Fault-Tolerant: Solr scales up and down easily depending on your loads and use cases. Rebalancing and fault tolerance are built into Solr out of the box
- Near Real-Time Indexing: Solr can index and search at the same time
The Varonis WebUI is an awesome tool for advanced alerting and investigating cybersecurity incidents. The WebUI is fast and easy to navigate, but the real power is how Varonis analyzes the data and uses advanced threat models to paint an easy to understand picture of cybersecurity attacks.
See the new Varonis WebUI in a free 1:1 Demo – and experience how fast and easy responding to cybersecurity threats with Varonis can be.
What should I do now?
Below are three ways you can continue your journey to reduce data risk at your company:
Schedule a demo with us to see Varonis in action. We'll personalize the session to your org's data security needs and answer any questions.
See a sample of our Data Risk Assessment and learn the risks that could be lingering in your environment. Varonis' DRA is completely free and offers a clear path to automated remediation.
Follow us on LinkedIn, YouTube, and X (Twitter) for bite-sized insights on all things data security, including DSPM, threat detection, AI security, and more.







-1.png)

