A new infostealer called Storm appeared on underground cybercrime networks in early 2026, representing a shift in how credential theft is developing. For under $1,000 a month, operators get a stealer that harvests browser credentials, session cookies, and crypto wallets, then quietly ships everything to the attacker's server for decryption.
To understand why enterprises should care, it helps to know what changed. Stealers used to decrypt browser credentials on the victim's machine by loading SQLite libraries and accessing credential stores directly. Endpoint security tools got good at catching this, making local browser database access one of the clearest signs that something malicious was running.
Then Google introduced App-Bound Encryption in Chrome 127 (July 2024), which tied encryption keys to Chrome itself and made local decryption even harder. The first wave of bypasses involved injecting into Chrome or abusing its debugging protocol, but those still left traces that security tools could pick up.

Stealer developers responded by stopping local decryption altogether and shipping encrypted files to their own infrastructure instead, removing the telemetry most endpoint tools rely on to catch credential theft. Storm takes this approach further by handling both Chromium and Gecko-based browsers (Firefox, Waterfox, Pale Moon) server-side, where StealC V2 still processes Firefox locally.
Collected data includes everything attackers need to restore hijacked sessions remotely and steal from their victims: saved passwords, session cookies, autofill, Google account tokens, credit card data, and browsing history. One compromised employee browser can hand an operator authenticated access to SaaS platforms, internal tools, and cloud environments without ever triggering a password-based alert.
Storm's forum listing.
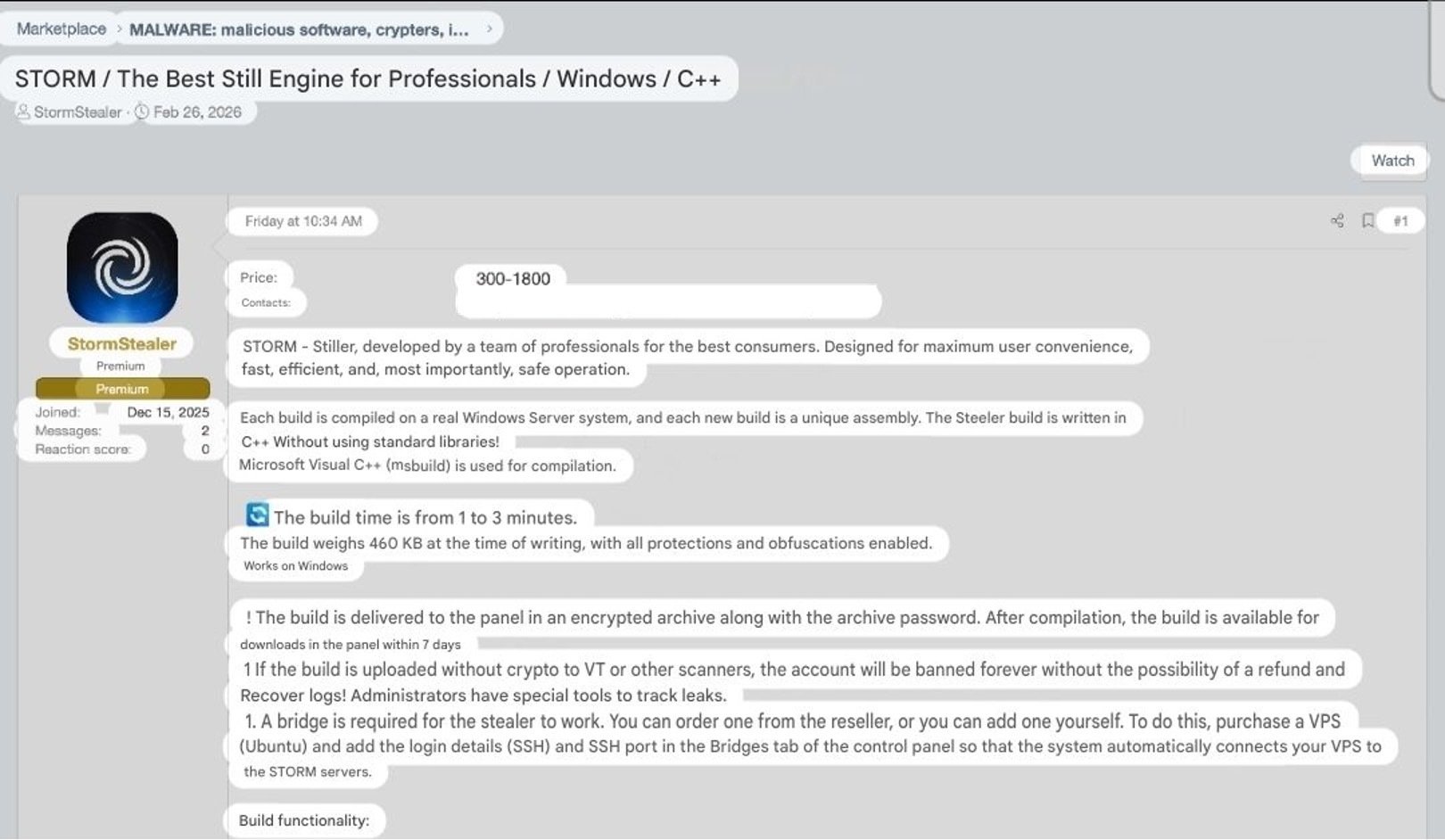
Storm's forum listing.
Cookie restore and session hijacking
Once Storm has decrypted the browser data, stolen credentials and session cookies are dumped directly into the operator's panel. Where most stealers require buyers to manually replay stolen logs, Storm automates the next step. Feed in a Google Refresh Token and a geographically matched SOCKS5 proxy, and the panel silently restores the victim's authenticated session.
Cookie restore panel with a completed session hijack.
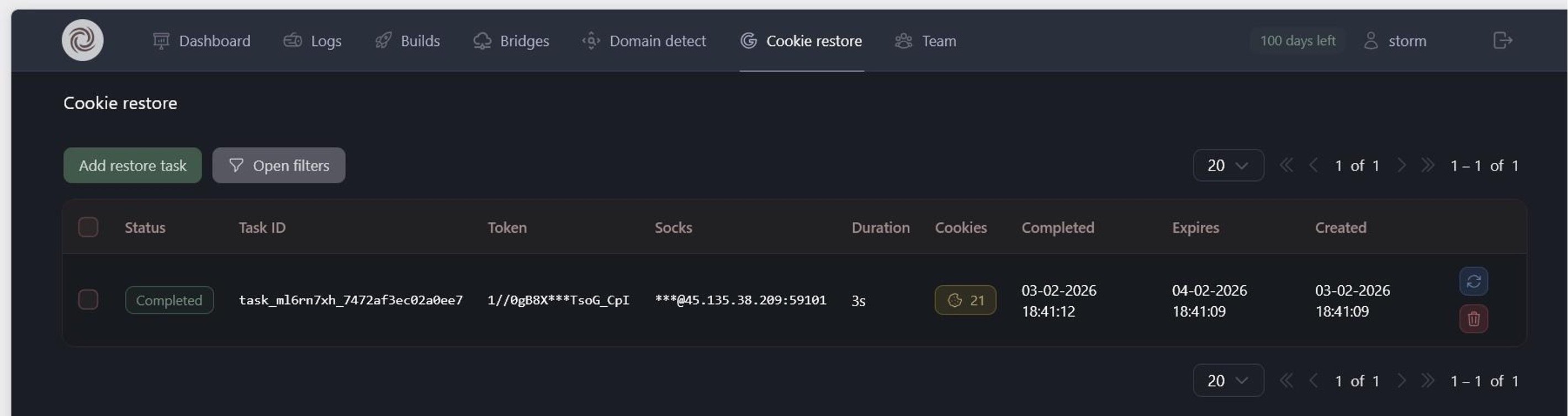
Cookie restore panel with a completed session hijack.
Varonis Threat Labs has covered this class of attack before. Our Cookie-Bite research demonstrated how stolen Azure Entra ID session cookies render MFA irrelevant, giving attackers persistent access to Microsoft 365 without ever needing a password. The SessionShark analysis showed how phishing kits intercept session tokens in real time to defeat Microsoft 365 MFA. Storm's cookie restore is the same underlying technique, productised and sold as a subscription feature.
Collection and infrastructure
Beyond credentials, Storm grabs documents from user directories, pulls session data from Telegram, Signal, and Discord, and targets crypto wallets through both browser extensions and desktop apps. System information and screenshots are captured across multiple monitors. Everything runs in memory to reduce the chance of detection.
Build configuration with collection modules and file grabber rules.
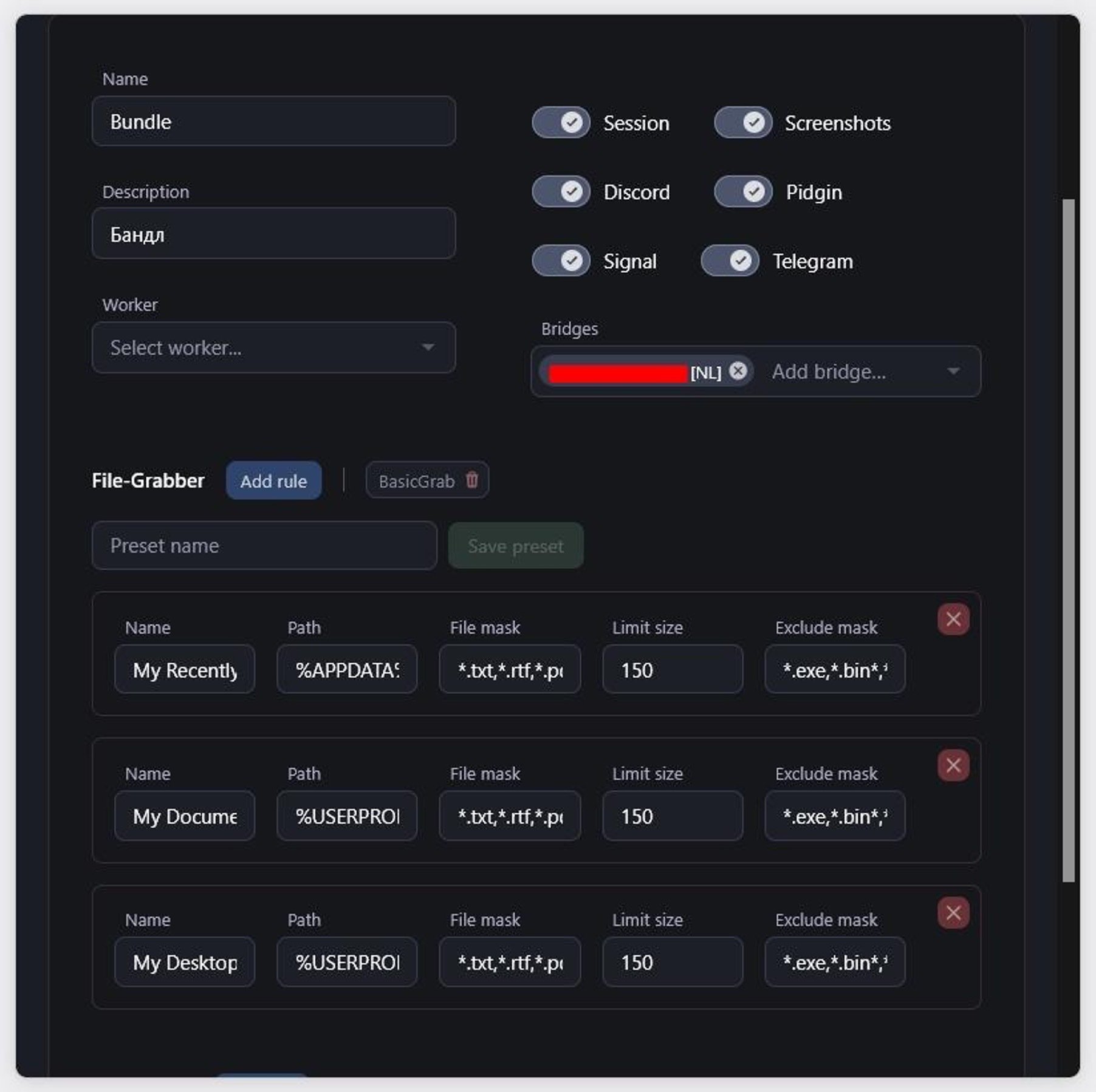
Build configuration with collection modules and file grabber rules.
On the infrastructure side, operators connect their own virtual private servers (VPS) to Storm's central servers, routing stolen data through infrastructure they control rather than a shared platform. This keeps the central servers insulated from takedown attempts, because law enforcement or abuse reports hit the operator's node first.
Team management supports multiple workers with permissions covering log access, build creation, and cookie restoration, so a single Storm licence can support a small cybercriminal operation with divided responsibilities.
Domain detection auto-labels stolen credentials by service, with rules visible for Google, Facebook, Twitter/X, and cPanel, making it straightforward for operators to filter and prioritise the accounts they want to exploit first.
Domain detection rules.
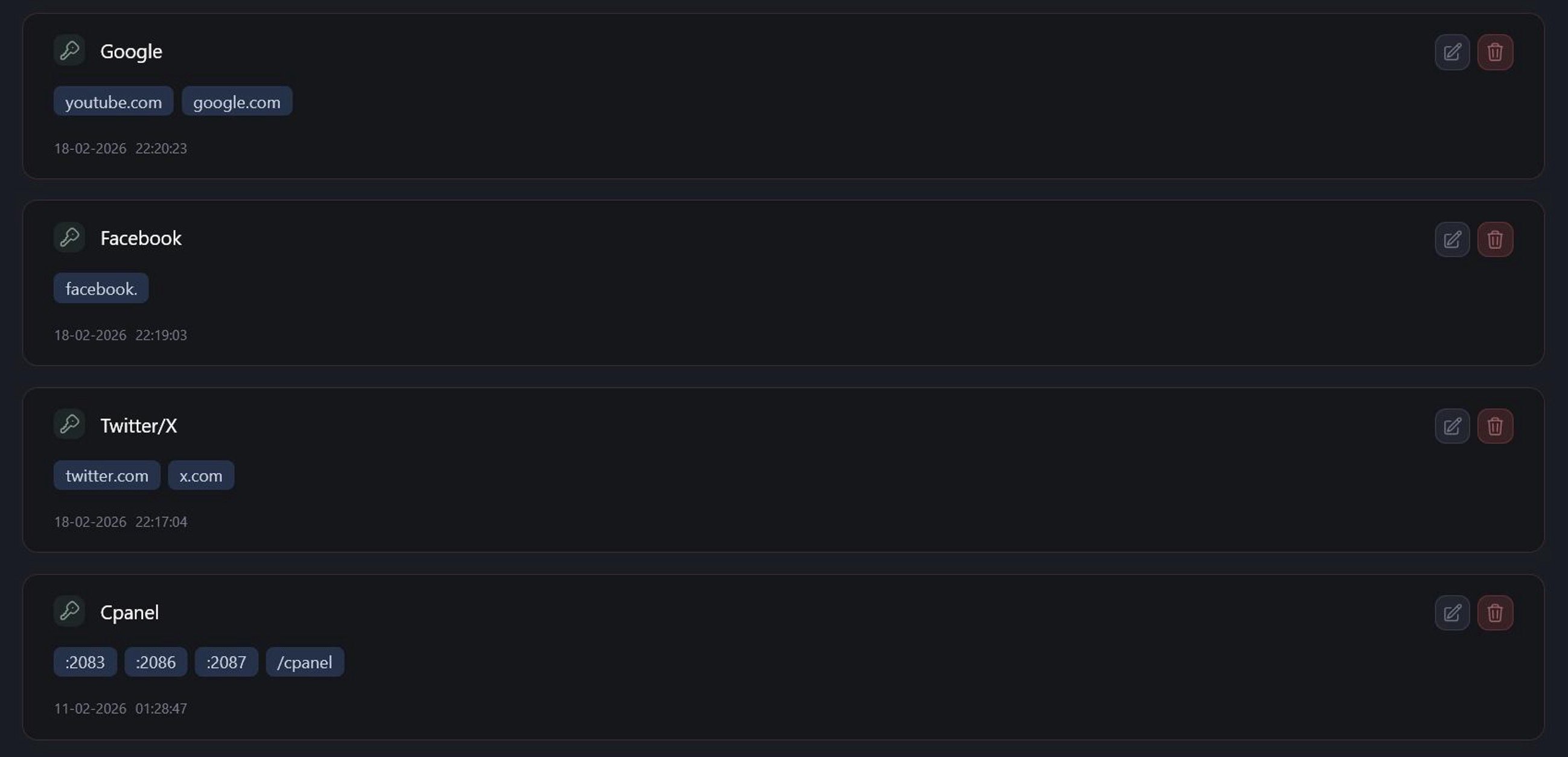
Domain detection rules.
Active campaigns and pricing
At the time of investigation, the logs panel contained 1,715 entries spanning India, the US, Brazil, Indonesia, Ecuador, Vietnam, and several other countries. Whether all of these represent real victims or include test data is difficult to confirm from panel imagery alone, but the varied IPs, ISPs, and data sizes look consistent with active campaigns.
Credentials tagged to Google, Facebook, Twitter/X, Coinbase, Binance, Blockchain.com, and Crypto.com appear across multiple entries, the kind of data that typically ends up on the credential marketplaces that feed account takeover, fraud, and initial access for more targeted intrusions.
Storm’s log panel.
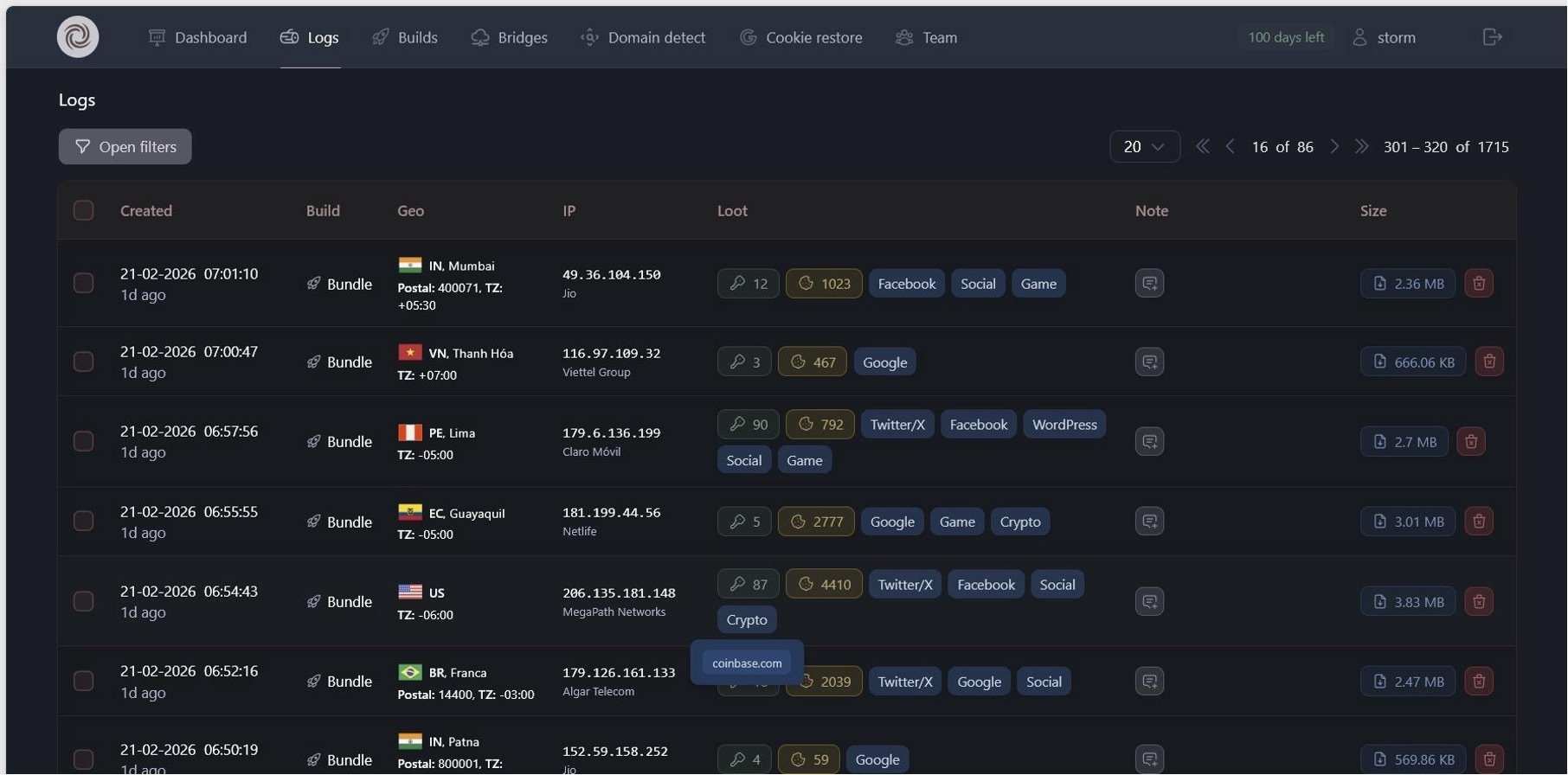
Storm’s log panel.
Log entries with cryptocurrency exchange hits.
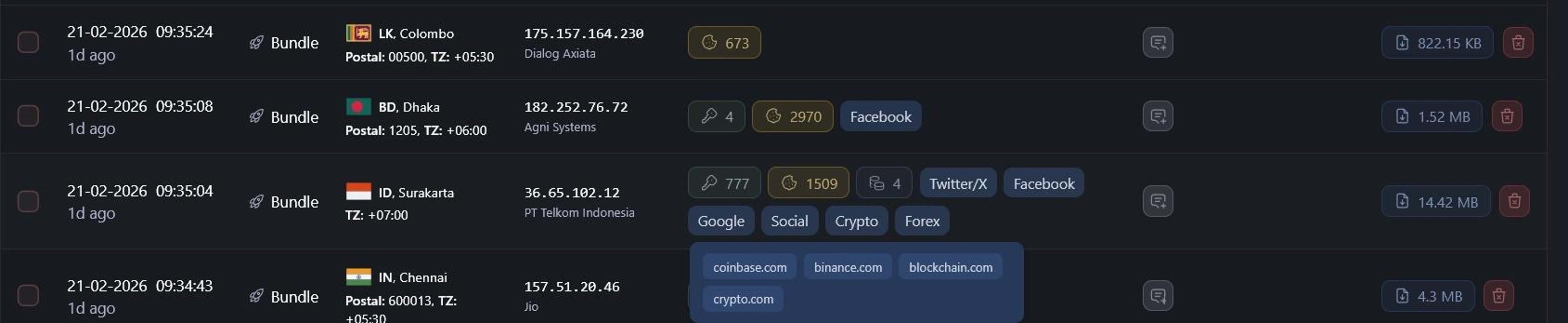
Log entries with cryptocurrency exchange hits.
Storm is sold on a tiered subscription: $300 for a 7-day demo, $900/month standard, $1,800/month for a team license with 100 operator seats and 200 builds. A crypter is required on top. Builds keep running after a subscription expires, so deployed stealers continue harvesting data regardless of the operator’s license status.
The different prices and packages.
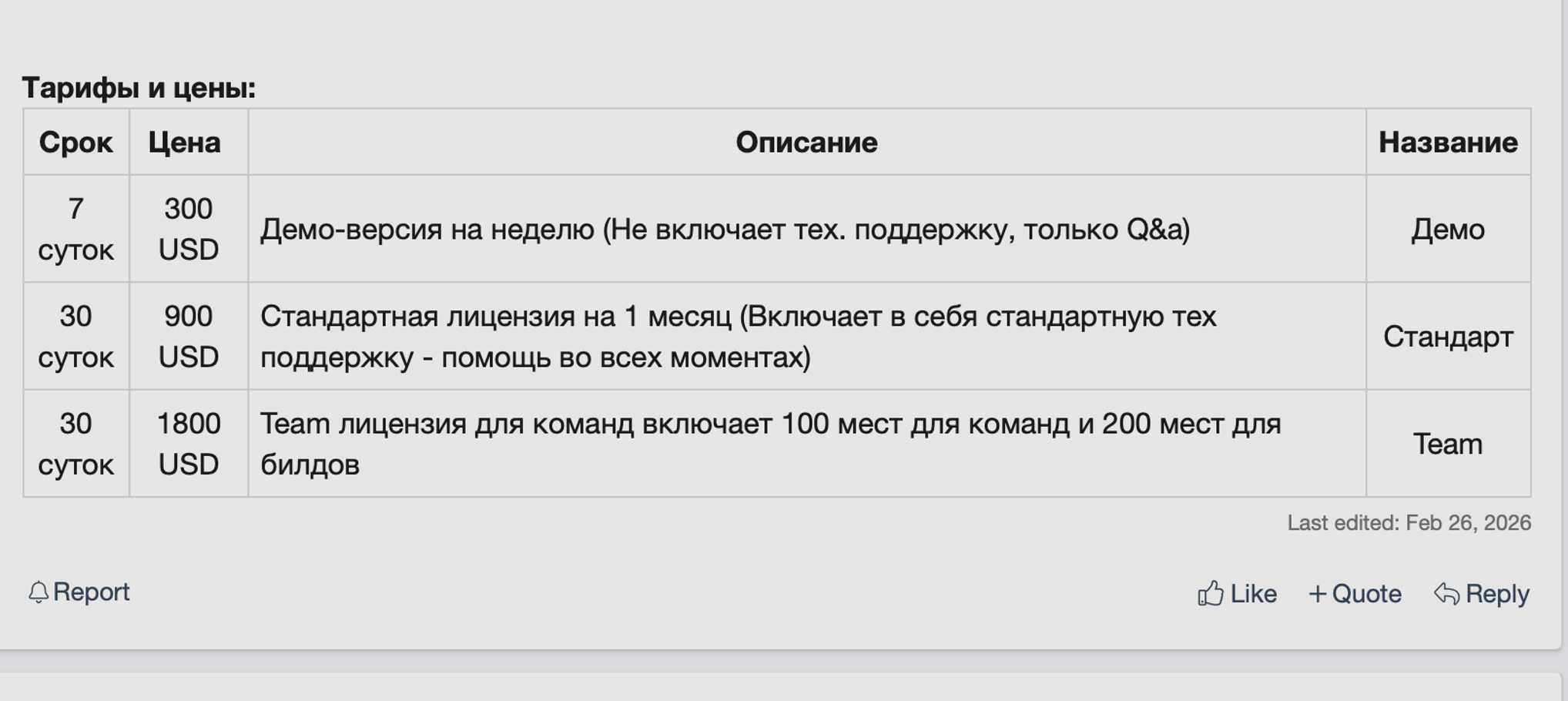
The different prices and packages.
Detecting stolen sessions
Storm is consistent with a broader shift in the stealer market. Server-side decryption enables attackers to avoid tripping endpoint tools designed to catch traditional on-device decryption, and session cookie theft has been replacing password theft as the primary objective for a while now. The credentials and sessions that stealers like Storm harvest are the start of what comes next: logins from unfamiliar locations, lateral movement, and data access that breaks established patterns.
Indicators of compromise
-
Forum handle: StormStealer
-
Forum ID: 221756
-
Account registered: 12/12/25
-
Current version: v0.0.2.0 (Gunnar)
-
Build characteristics: C++ (MSVC/msbuild), ~460 KB, Windows only
MITRE ATT&CK mapping
T1555.003
Server-side decryption of Chromium and Gecko browser databases
T1539
Credentials in Files
T1552.001
Targets crypto wallets, messenger sessions, Discord tokens
Data from Local System
T1005
File grabber collects documents from configurable directories
Collection
Screen Capture
T1113
Multi-monitor screenshots captured in memory via GDI API
System Information Discovery
T1082
OS, CPU, RAM, GPU, network adapters, launch method
Exfiltration
Exfiltration Over C2 Channel
T1041
Collected data compressed and transmitted via bridge nodes
Execution
Loader executes .ps1 payloads with -exec bypass
Command and Control
Ingress Tool Transfer
T1105
What should I do now?
Below are three ways you can continue your journey to reduce data risk at your company:
Schedule a demo with us to see Varonis in action. We'll personalize the session to your org's data security needs and answer any questions.
See a sample of our Data Risk Assessment and learn the risks that could be lingering in your environment. Varonis' DRA is completely free and offers a clear path to automated remediation.
Follow us on LinkedIn, YouTube, and X (Twitter) for bite-sized insights on all things data security, including DSPM, threat detection, AI security, and more.








