Varonis for Microsoft 365 Copilot builds on Varonis' existing Microsoft 365 security suite, featuring capabilities to monitor Copilot prompts, responses, and data access in real time, detect abnormal Copilot interactions, and automatically limit access to sensitive data by both humans and AI agents.
Varonis has helped thousands of customers classify sensitive data, reduce exposure, and detect threats in M365 since we first introduced coverage in 2015. Our M365 security suite helps customers prepare to safely adopt Copilot, but once deployed, organizations require ongoing visibility and control over what AI is doing in their environment. That's where the Copilot security module comes in.
If you want to see these Copilot capabilities in action, watch the following video or keep reading to get a rundown of our growing list of Copilot security features.
Copilot posture dashboards
Our Copilot-focused dashboard gives you a real-time view of the sensitive and regulated data exposed to Copilot users, shows usage trends, analyzes prompts and responses for suspicious activity, and tracks how much sensitive data is being accessed by AI.
This dashboard not only helps quantify your Copilot readiness during the pilot phase, but it also helps you monitor adoption, answering questions like, "How many people are using Copilot?" or "Who are my Copilot super users?"
Varonis taps into the identity fabric of Microsoft Entra ID to surface aforementioned usage data as well as risky identities accessing Copilot. These dashboards help teams quickly see, both, where users are finding productivity success and bad actors are leveraging Copilot for reconnaissance in the same location.

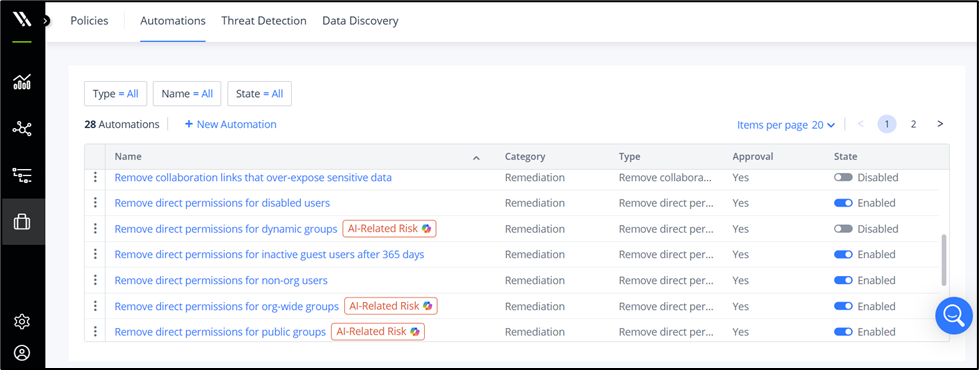
Copilot policy automation
In a 2025 report from Gartner, researchers found that “combatting oversharing and permission sprawl in M365 is now a top priority due to business interest in M365 Copilot. However, securing M365 Copilot at scale is complex, with controls split across multiple different M365 admin centers that are often managed by different IT teams.”
Our automated policies help you quickly get your M365 environment ready for a successful Copilot rollout, safely eliminating massive amounts of data exposure in days. We recommend you keep most policies enabled to continuously limit Copilot's access to sensitive information and prevent accidental data leakage as new data is rapidly created.
We have dozens of automations out of the box and they are all customizable, so you can define your organization's security policies and Varonis will automatically enforce them.
Policies that are designed to help ensure Copilot readiness and ongoing security are marked with a "AI-Related Risk" badge and perform actions such as removing org-wide links, stale sensitive links, and stale group memberships.
One of our customers reduced their Copilot exposure by 99.8% in just 10 days with our automations:
- Approximately one million files across SharePoint, OneDrive, and Teams
- Varonis' classification scans found and labeled 120K sensitive files
- Our exposure analysis found 57K sensitive files with excessive access
- The customer enabled our Copilot policies and eliminated 2K unnecessary sharing links and right-sized access to all 57K sensitive files
- The security team notified M365 admins of the remediation task and remarkably received zero help desk tickets or complaints
Copilot monitoring and forensics
We capture all Copilot interactions, including prompts and responses, and which files are being referenced in prompt responses in our centralized and searchable audit trail.
Varonis enriches Copilot events with metadata such as file sensitivity, user account type, and geolocation, so you can answer questions such as, "Which executive users accessed sensitive financial data via Copilot this week from suspicious IP addresses?"
Comprehensive prompt and response monitoring enables you to conduct in-depth examinations, control sensitive data exposure, and prevent malicious behavior. Not only can you see every prompt and response, but we will alert you to suspicious behavior, like employees trying to access salary information.
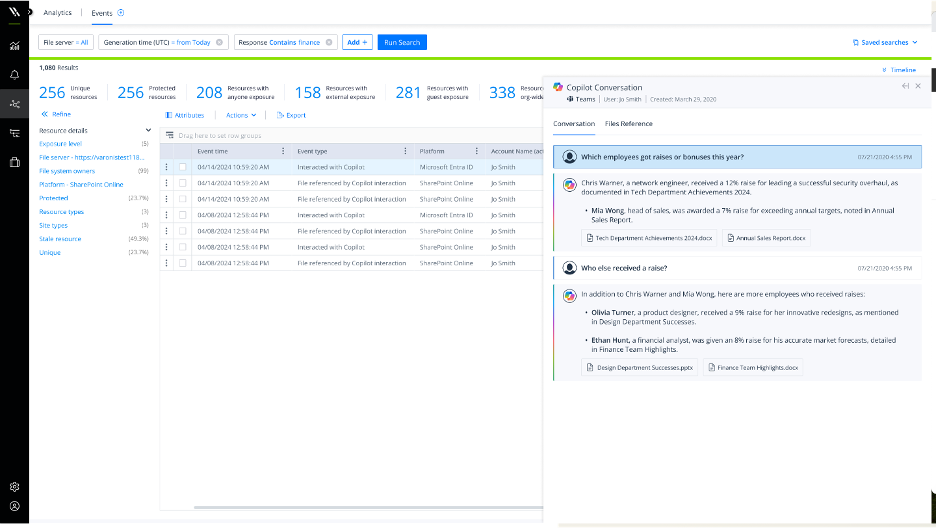
Copilot activity is available alongside all other M365 activity, making it easy to perform investigations that correlate authentication events from Entra ID with email events from Exchange Online.

Wait, why is Copilot showing me this data?!
When testing Copilot, you will undoubtedly enter a prompt and get a response that references data you had no idea you could access. The next question is always, "Why?"
Varonis crawls your entire M365 graph, not a select window of time or number of sites and resources. The complete crawl calculates true effective permissions based on links, group memberships (local and domain), nested permissions, direct permissions, and more.
Our access intelligence UI helps you quickly pinpoint why sensitive data is exposed to certain users via Copilot (or otherwise). Investigations that could take days or weeks to perform manually can be done in seconds with Varonis.

Copilot threat detection
Varonis' user behavior analysis (UBA) engine factors in Copilot activity and notifies customers of abnormal or suspicious Copilot interactions with sensitive data.
Our alerts are not simply based on static rules (e.g., "Alert me if someone exceeds 200 prompts in a day"), they are based on meaningful deviations from a behavioral baseline that is unique to your tenant and your users. This means that you won't have to sift through hundreds or thousands of noisy alerts.
With our MDDR service, a Varonis analyst will monitor your environment 24x7x365 and respond to every alert, so you don't have to.

Athena AI integration
Lastly, Varonis for Microsoft 365 Copilot works with Athena AI's SOC assistant and natural language search, making it easy to investigate and resolve Copilot-related security incidents. Athena AI is provided without an additional expense

Ready to try Varonis for Microsoft 365 Copilot?
You can request a free Microsoft 365 Copilot readiness assessment to evaluate your AI security posture or start a Varonis trial from the Azure Marketplace. During the assessment, you can also gather answers to your most pressing AI questions or check out the top ones the Varonis team has gathered here.
What should I do now?
Below are three ways you can continue your journey to reduce data risk at your company:
Schedule a demo with us to see Varonis in action. We'll personalize the session to your org's data security needs and answer any questions.
See a sample of our Data Risk Assessment and learn the risks that could be lingering in your environment. Varonis' DRA is completely free and offers a clear path to automated remediation.
Follow us on LinkedIn, YouTube, and X (Twitter) for bite-sized insights on all things data security, including DSPM, threat detection, AI security, and more.








