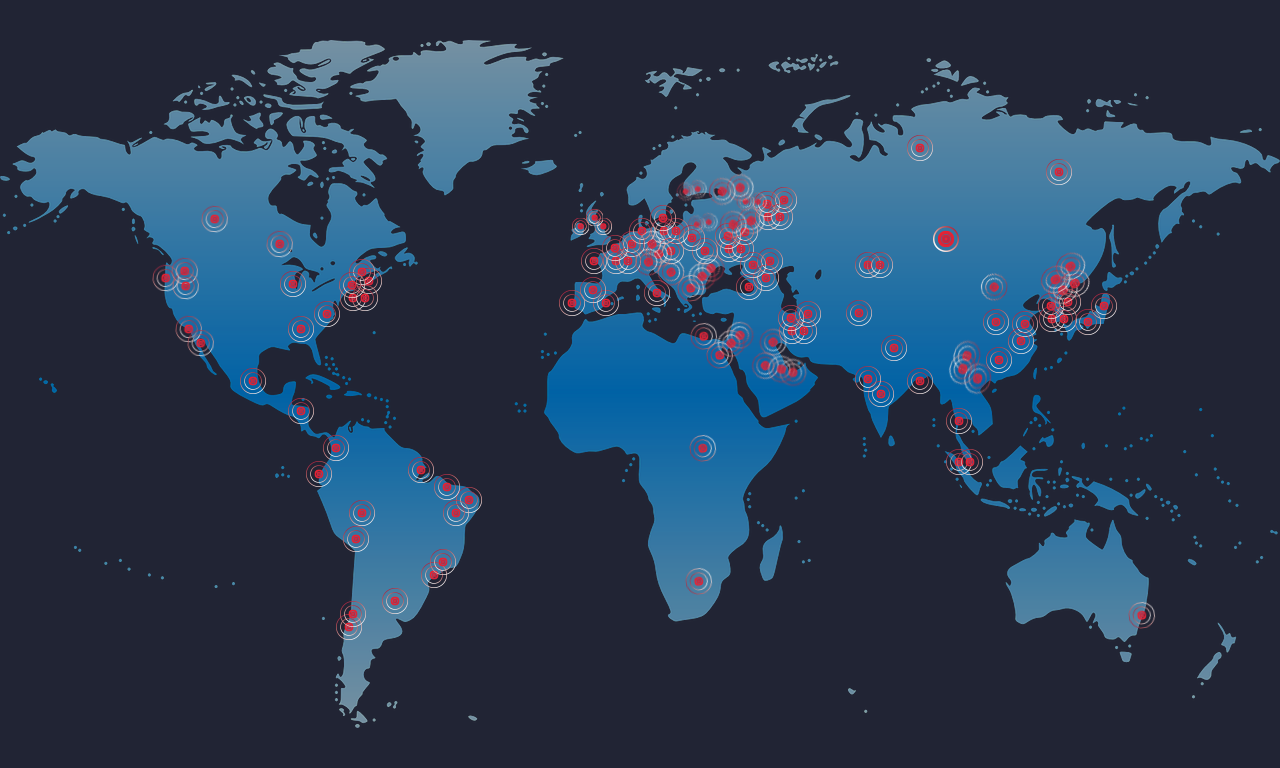
Remember those NSA exploits that got leaked a few months back? A new variant of ransomware using those exploits is spreading quickly across the world – affecting everyone from the NHS to telecom companies to FedEx.
Here’s What We Know So Far
Ransomware appears to be getting in via social engineering and phishing attacks, though vulnerable systems may also be at risk if TCP port 445 is accessible. Unlike most ransomware that encrypts any accessible file from a single infected node, this ransomware also moves laterally via exploit (i.e., EternalBlue) to vulnerable unpatched workstations and servers, and then continues the attack. Unpatched windows hosts (Vista, 7, 8,10, server 2008, 2008 R2, 2012, 2012 R2, and 2016) running SMB v1 are all vulnerable.
Infected hosts are running strains of ransomware, such as Wanna Decrypt0r (more below) that encrypts files and changes their extensions to:
- .WRNY
- .WCRY (+ .WCRYT for temp files>
- .WNCRY (+ .WNCRYT for temp files)
The Ransomware also leaves a note with files named @Please_Read_Me@.txt, or !Please_Read_Me!.txt, and will display an onscreen warning.
Get a Free Data Risk Assessment
Here’s What You Can Do
- Disable SMBv1 while you patch– how to: here
- Block TCP port 445 from outside (or between segments if possible)
- Make sure DatAlert is enabled & up to date
- Patch! – https://technet.microsoft.com/en-us/library/security/ms17-010.aspx
MS17-010, released in March, closes a number of holes in Windows SMB Server. These exploits were all exposed in the recent NSA hacking tools leak. Exploit tools such as EternalBlue, EternalChampion, EternalSynergy and EternalRomance (all part of the Fuzzbunch exploit platform) all drop DoublePulsar onto compromised hosts. DoublePulsar was created by the NSA and is basically a malware downloader, which is used as an intermediary for downloading more potent malware executables onto infected hosts.
If you’re an existing DatAlert customer, you can set up office hours with your assigned engineer to review your threat models and alerts. Don’t have DatAlert yet? Get a demo of our data security platform and see how to detect zero-day attacks.
DatAlert Customers
If you’re a DatAlert Analytics customer, the threat model “Immediate Pattern Detected: user actions resemble ransomware” was designed to detect this and other zero-day variants of ransomware; however, we also strongly recommend that you update the dictionaries used by DatAlert signature-based rules. Instructions for updating your dictionaries are here: https://connect.varonis.com/docs/DOC-2749
If for some reason you can’t access the connect community, here is how to update your dictionaries to include the new extensions for this variant:
Open the DatAdvantage UI > Tools > Dictionaries > Crypto files (Predefined)
Open the DatAdvantage UI > Tools > Dictionaries > Encrypted files (Predefined)
Details
Vulnerabilities
The Malware exploits multiple Windows SMBv1 Remote Code vulnerabilities:
Windows Vista, 7, 8,10, server 2008, 2008 R2, 2012, 2012 R2, 2016 are all vulnerable if not patched and SMBv1 Windows Features is enabled.
https://technet.microsoft.com/en-us/library/security/ms17-010.aspx
Ransomware strains
WCry / WannaCry / WannaCrypt0r / WannaCrypt / Wana Decrypt0r
This outbreak is version 2.0 of WCry ransomware which first appeared in March. Until this outbreak, this ransomware family was barely heard of. Though likely spread via phishing and social engineering attacks, if tcp port 445 is exposed on vulnerable windows machines, that could be exploited using the Fuzzbunch exploit platform.
Other helpful links
- https://blog.avast.com/ransomware-that-infected-telefonica-and-nhs-hospitals-is-spreading-aggressively-with-over-50000-attacks-so-far-today
- https://www.bleepingcomputer.com/news/security/wana-decrypt0r-ransomware-using-nsa-exploit-leaked-by-shadow-brokers-is-on-a-rampage/
- https://www.bleepingcomputer.com/forums/t/646476/wncry-wcry-wanacrypt0r-wana-decrypt0r-ransomware-help-support-topic/
- https://threatpost.com/nsas-doublepulsar-kernel-exploit-in-use-internet-wide/125165/
What should I do now?
Below are three ways you can continue your journey to reduce data risk at your company:
Schedule a demo with us to see Varonis in action. We'll personalize the session to your org's data security needs and answer any questions.
See a sample of our Data Risk Assessment and learn the risks that could be lingering in your environment. Varonis' DRA is completely free and offers a clear path to automated remediation.
Follow us on LinkedIn, YouTube, and X (Twitter) for bite-sized insights on all things data security, including DSPM, threat detection, AI security, and more.