Data Security Posture Management (DSPM)
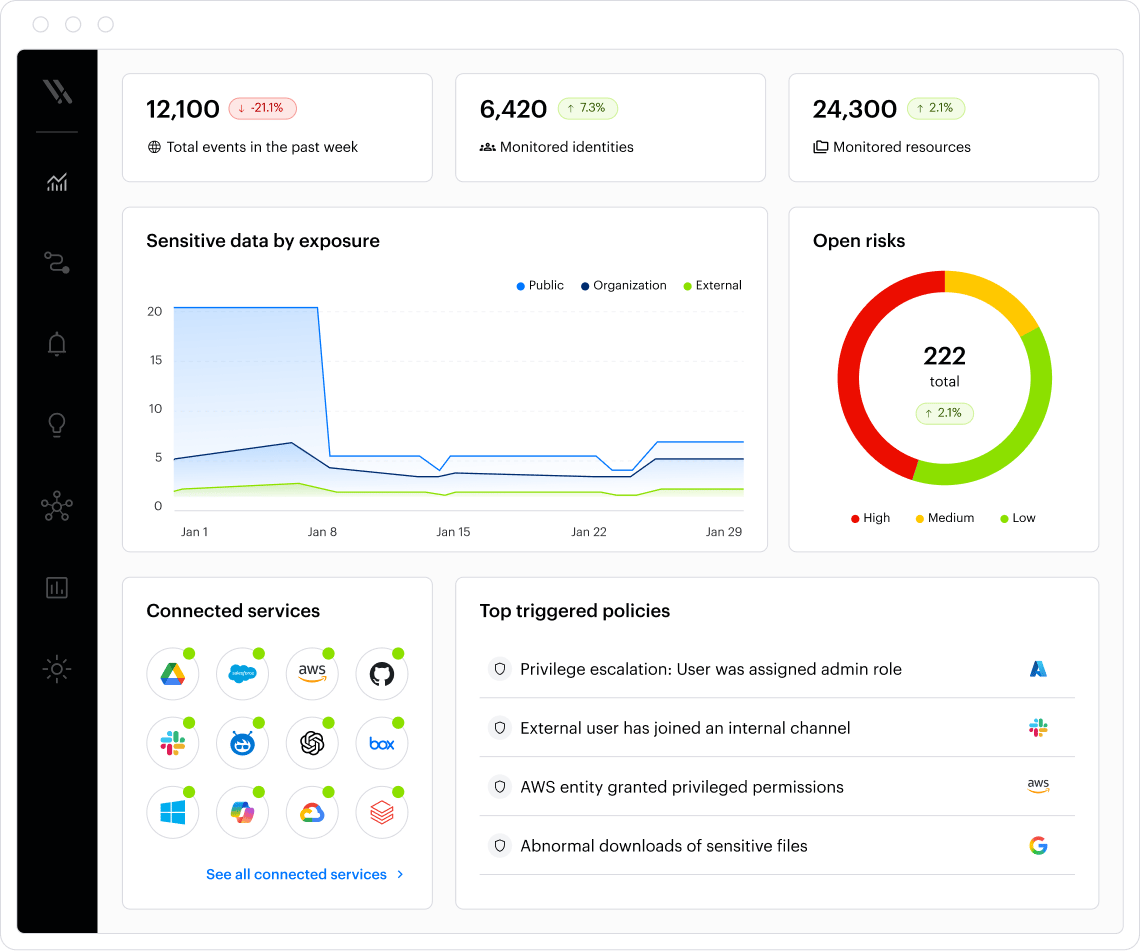
Discover, map, monitor, and protect data wherever it lives. Varonis' #1-rated DSPM is the only solution that automatically remediates risk, enforces policies, and detects threats in real-time.
- Cloud-native
- Automated
- Broad coverage
Trusted by thousands of companies
Varonis is named a Customers' Choice in the 2025 Gartner Peer Insights™ Voice of the Customer for Data Security Posture Management.
Gartner® and Peer Insights™ are trademarks of Gartner, Inc. and/or its affiliates. All rights reserved. Gartner® Peer Insights™ content consists of the opinions of individual end users based on their own experiences, and should not be construed as statements of fact, nor do they represent the views of Gartner or its affiliates. Gartner does not endorse any vendor, product or service depicted in this content nor makes any warranties, expressed or implied, with respect to this content, about its accuracy or completeness, including any warranties of merchantability or fitness for a particular purpose.

You found sensitive data, now what?
Comprehensive coverage
- File storage
- SaaS apps & email
- IaaS & databases
Automated remediation
- Remove excessive permissions
- Fix risky misconfigurations
- Apply labels and enforce DLP policies
Award-winning threat detection
- Alert on abnormal behavior
- Automate threat response
- Get 24x7x365 MDDR coverage
Automation was one of the huge factors. Our security risk in general is 10 times lower than it was before.
Data discovery and classification
Battle-tested in complex multi-petabyte environments for militaries and Fortune 100 companies, Varonis gives you complete, current, and contextual data classification. Integrate with Microsoft Purview to apply labels and enforce DLP.
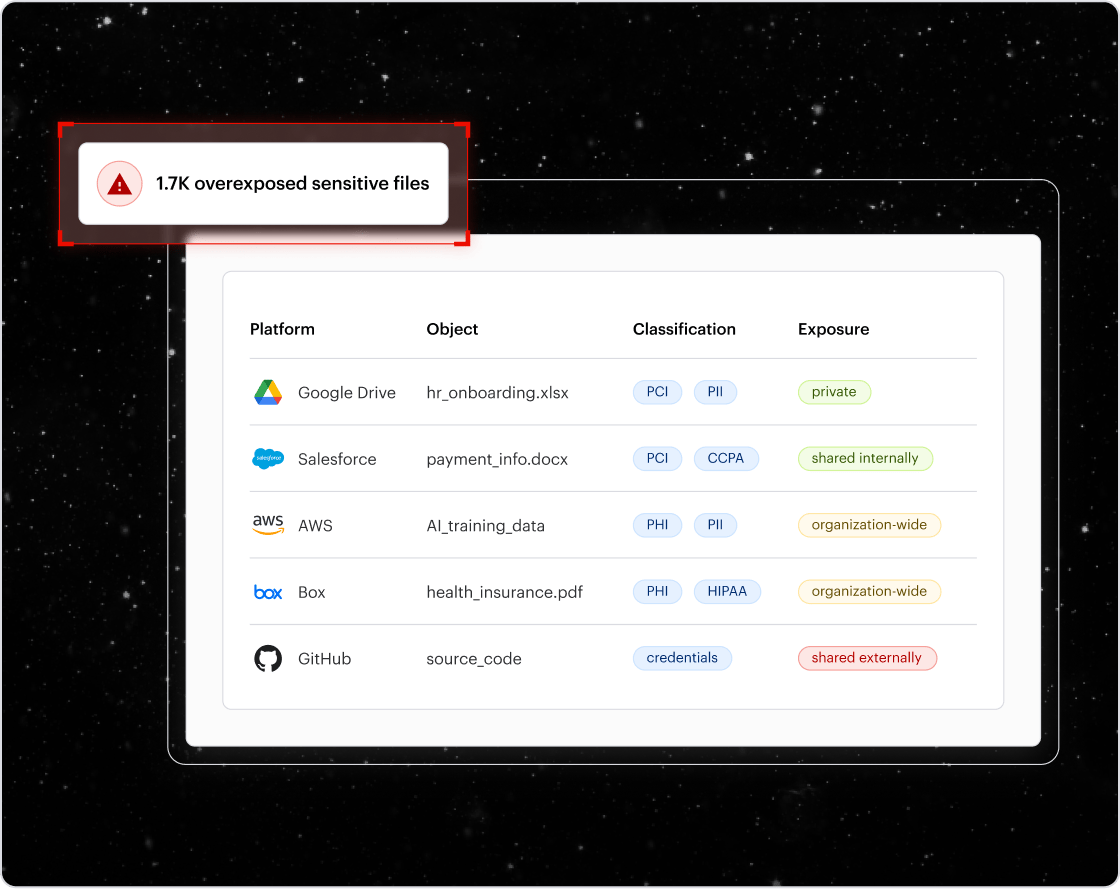
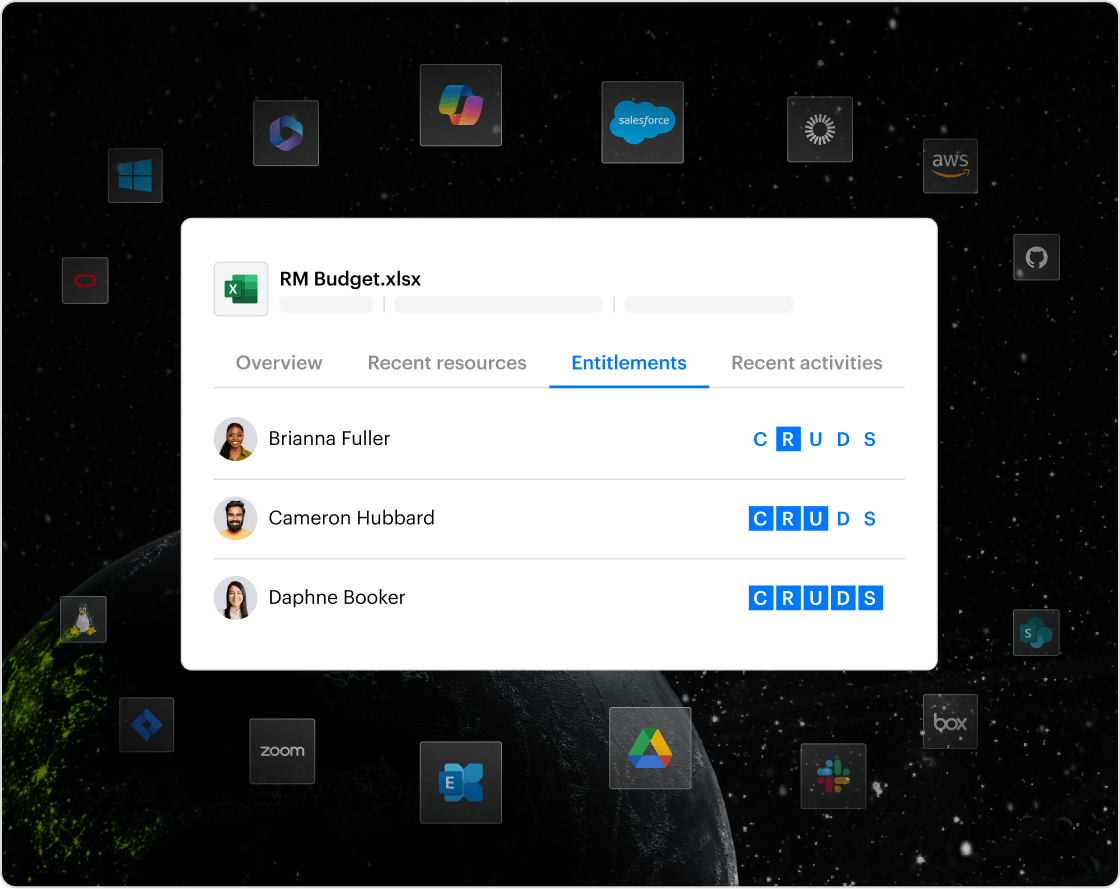
Access intelligence
Know who has access to your sensitive data at all times. The Varonis access graph factors in entitlements, group memberships, sharing links, muting permissions, and more, giving you the most accurate view of data risk on the planet.
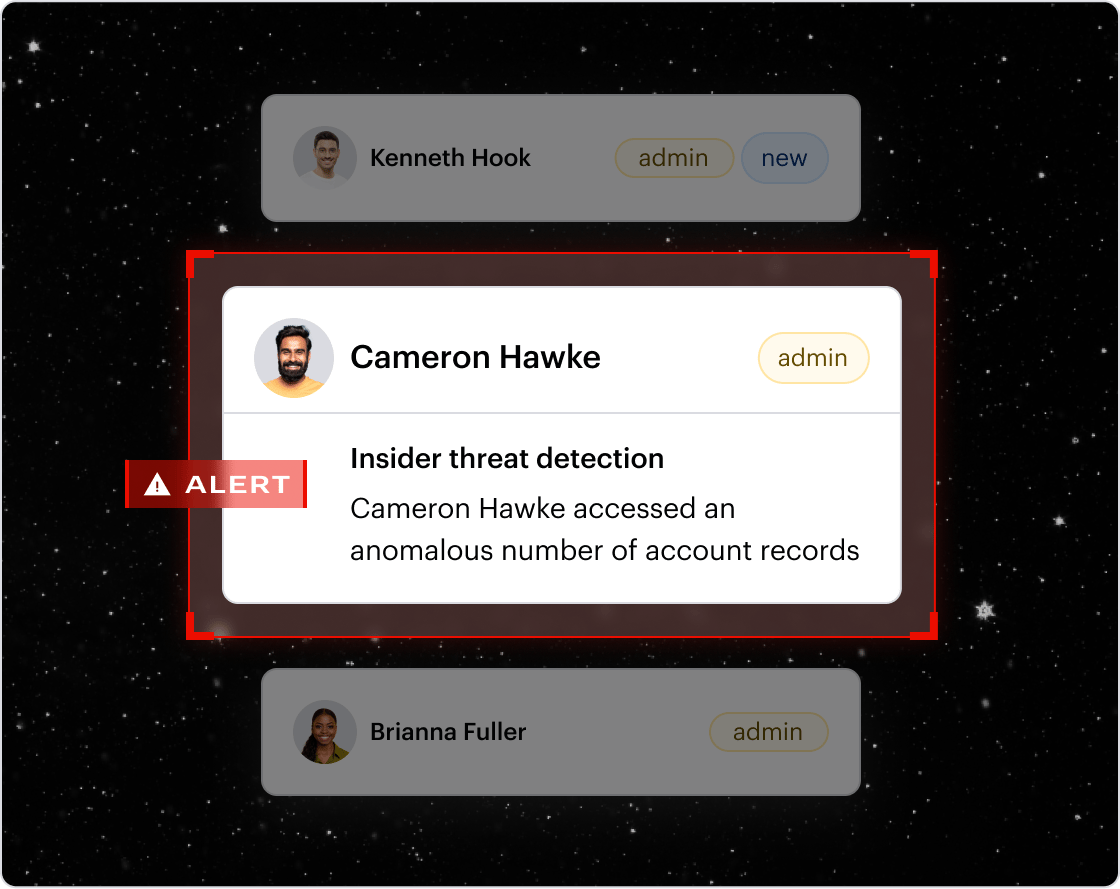
Data detection and response (DDR)
Get a searchable forensic audit trail of data access activity, permissions changes, link sharing, email send/receive, authentication events, and much more. Varonis builds a behavior baseline for every user and responds to threats.
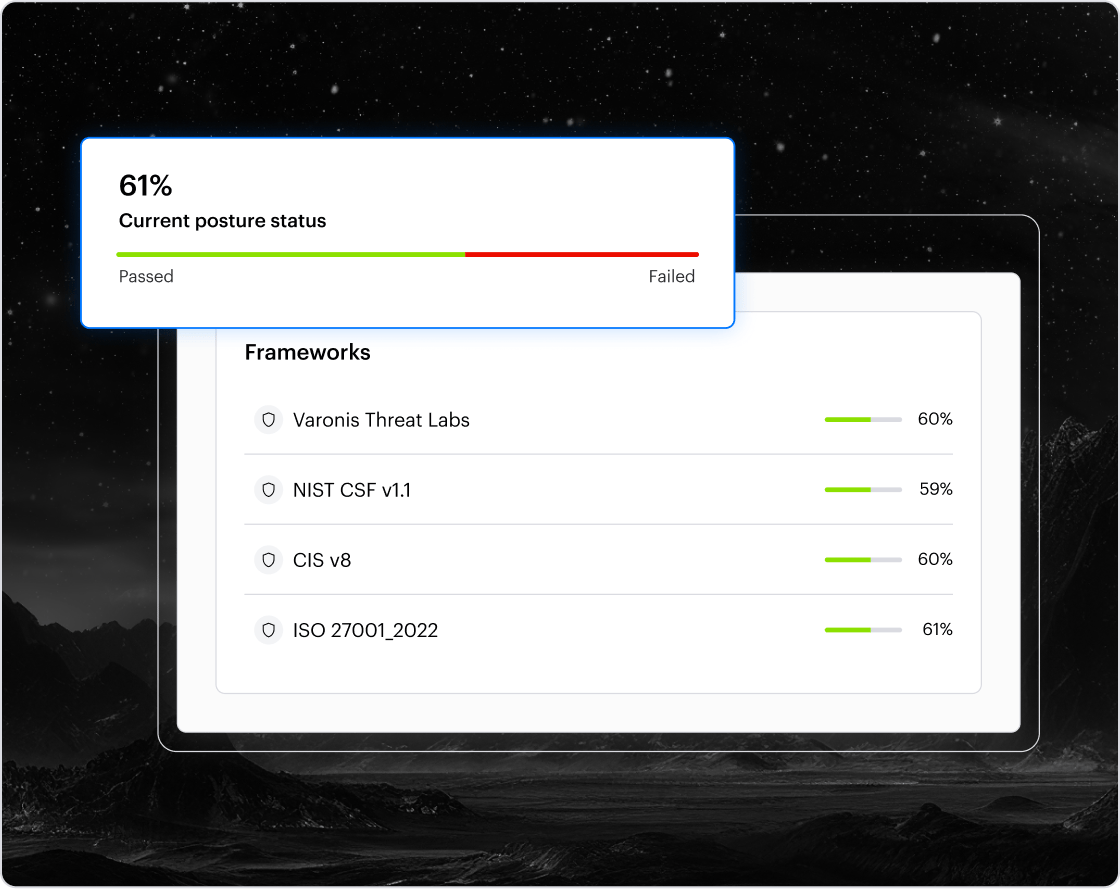
Compliance management
Measure your data security posture against common frameworks and regulations such as HIPAA, GDPR, CCPA, NIST, and ITAR. Ensure compliance with accurate out-of-the-box classifiers, policies, activity auditing, and reports.
Our customers have spoken
Protect your data, wherever it lives.
One platform for complete data security across multi-cloud, SaaS, hybrid, and AI.
Frequently Asked Questions
DSPM or data security posture management provides organizations visibility into where sensitive data is, who has access to that data, how it is being used, and what the security posture of the data store is.
Varonis is the leader in DSPM, recognized by analyst firms and customers alike. Varonis was rated #1 DSPM on Gartner Peer Insights, Winner of Most Innovative DSPM by Cyber Defense Magazine, and received top scores for DSPM in GigaOm Radar for Data Security.
Key DSPM capabilities include automated data discovery and classification, risk prioritization, permissions anlaysis, cloud and SaaS visibility, compliance reporting, remediation workflows, and AI risk detection.
Advanced DSPM platforms, like Varonis, go beyond just discovery and also correlate data sensitivity with user behavior and threat activity to prioritize the highest-risk exposures first.
DSPM Resources
Go beyond DSPM.
Ready to see the #1 Data Security Platform in action?
Ready to see the #1 Data Security Platform in action?
“I was amazed by how quickly Varonis was able to classify data and uncover potential data exposures during the free assessment. It was truly eye-opening.”
Michael Smith, CISO, HKS
"What I like about Varonis is that they come from a data-centric place. Other products protect the infrastructure, but they do nothing to protect your most precious commodity — your data."
Deborah Haworth, Director of Information Security, Penguin Random House
“Varonis’ support is unprecedented, and their team continues to evolve and improve their products to align with the rapid pace of industry evolution.”
Al Faella, CTO, Prospect Capital