GitHub repositories are high-value targets for threat actors. Repos can contain critical secrets, such as passwords, API keys, and tokens that can unlock the door to your most important apps and infrastructure.
Varonis is extending our world-class data classification capabilities to discover secrets, keys, and other sensitive data embedded in your GitHub repositories and source code.
Get a Free Data Risk Assessment
Varonis helps you identify and protect exposed GitHub secrets by:
- Automatically and continuously scanning public and private GitHub repositories for secrets
Our automatic, accurate classification engine discovers and classifies a massive range of secret types and sensitive data, such as PII, living across your corporate repositories — down to the branch and file level. - Prioritizing risky repositories based on exposure
Varonis correlates classification results with permissions to give you a complete and real-time picture of your internal and external exposure, allowing you to prioritize and fix critical issues before they become breaches. - Unifying sensitive data discovery across your SaaS, multi-cloud, and on-prem ecosystems
Secrets can end up anywhere! Varonis lets you control your discovery and classification policies, reporting, and remediation from a centralized control panel. Get a consistent experience with GitHub, Jira, Box, Amazon S3, and other cloud and on-prem data stores. - Detecting and stopping threats targeting your corporate repositories
Varonis continually monitors your corporate repos for risky or suspicious activity in real-time to detect threats and protect your critical source code from malicious actors.
Find secrets, PII, and other sensitive information in GitHub.
Varonis can discover hundreds of unique secret patterns in your source code. We use expert-built patterns and proximity matching to scan your environment for hundreds of popular secret types for apps and services such as Google OAuth 2.0, Twitter, Atlassian, LinkedIn, elliptic curve cryptographic keys, or cloud database credentials.
Some of the categories of secrets we detect include:
- Passwords
- Database credentials
- Connection strings
- Private keys
- Encryption certificates
- API keys
- Authentication tokens
- Encryption keys
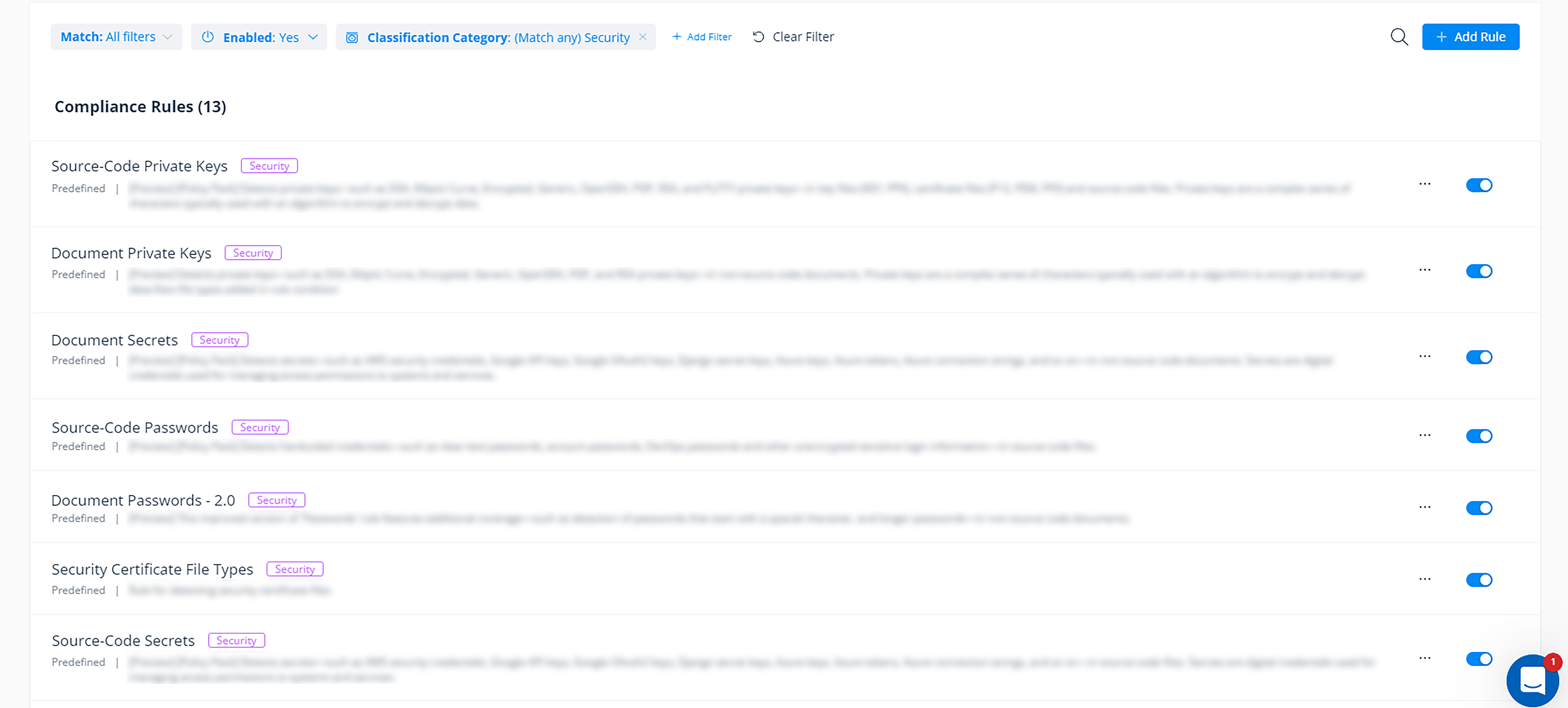 Easily select which types of exposed secrets you want Varonis to discover in your cloud data stores.
Easily select which types of exposed secrets you want Varonis to discover in your cloud data stores.
Varonis discovers more than just secrets.
Along with secrets and keys, Varonis also discovers and classifies sensitive data such as PII, PCI, and other regulated data that can end up in your repositories.
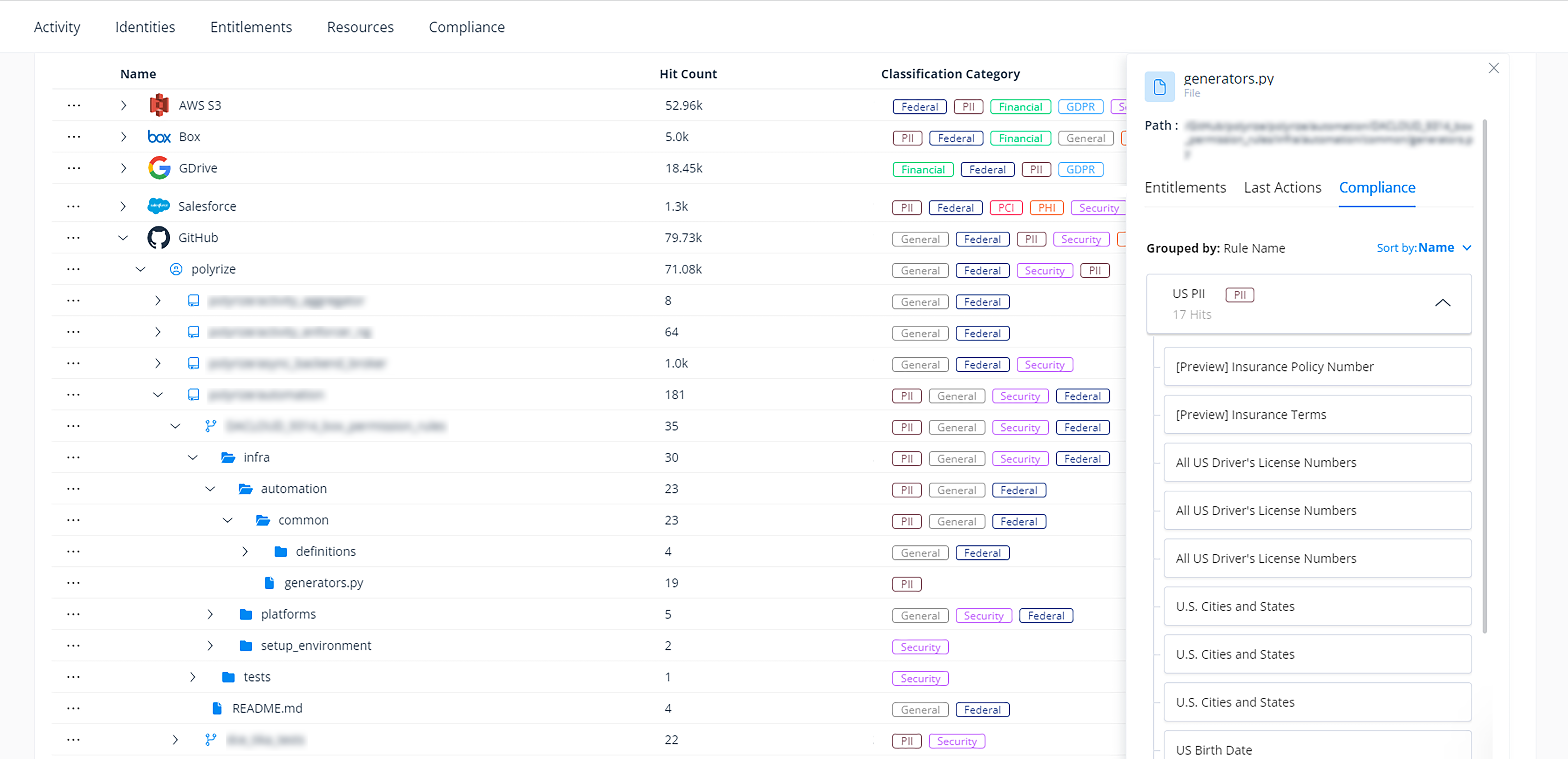 Varonis finds sensitive and regulated data stored in your repositories.
Varonis finds sensitive and regulated data stored in your repositories.
We’ll show you where this data lives and is potentially overexposed so you can lock down your repositories. With Varonis, only those who need access have it, helping you better manage regulatory compliance and avoid potential penalties or fines.
Understand where your sensitive GitHub repositories may be exposed.
Finding where secrets and sensitive data are hiding within your repositories is a great first step, but to truly understand and control risk, you need to know who has access to them and where sensitive data could be exposed.
Varonis maps user and group access to your corporate GitHub repositories down to the individual file level within each branch. We simplify permissions into an easy-to-read CRUDS model (create, read, update, delete, and share), so you can quickly identify who can access your sensitive GitHub resources and their permissions to better understand where your environment may be exposed.
See where external users have access to your GitHub resources and if any repositories containing secrets or other sensitive data have been made public, so you can take immediate steps to remediate any problems.
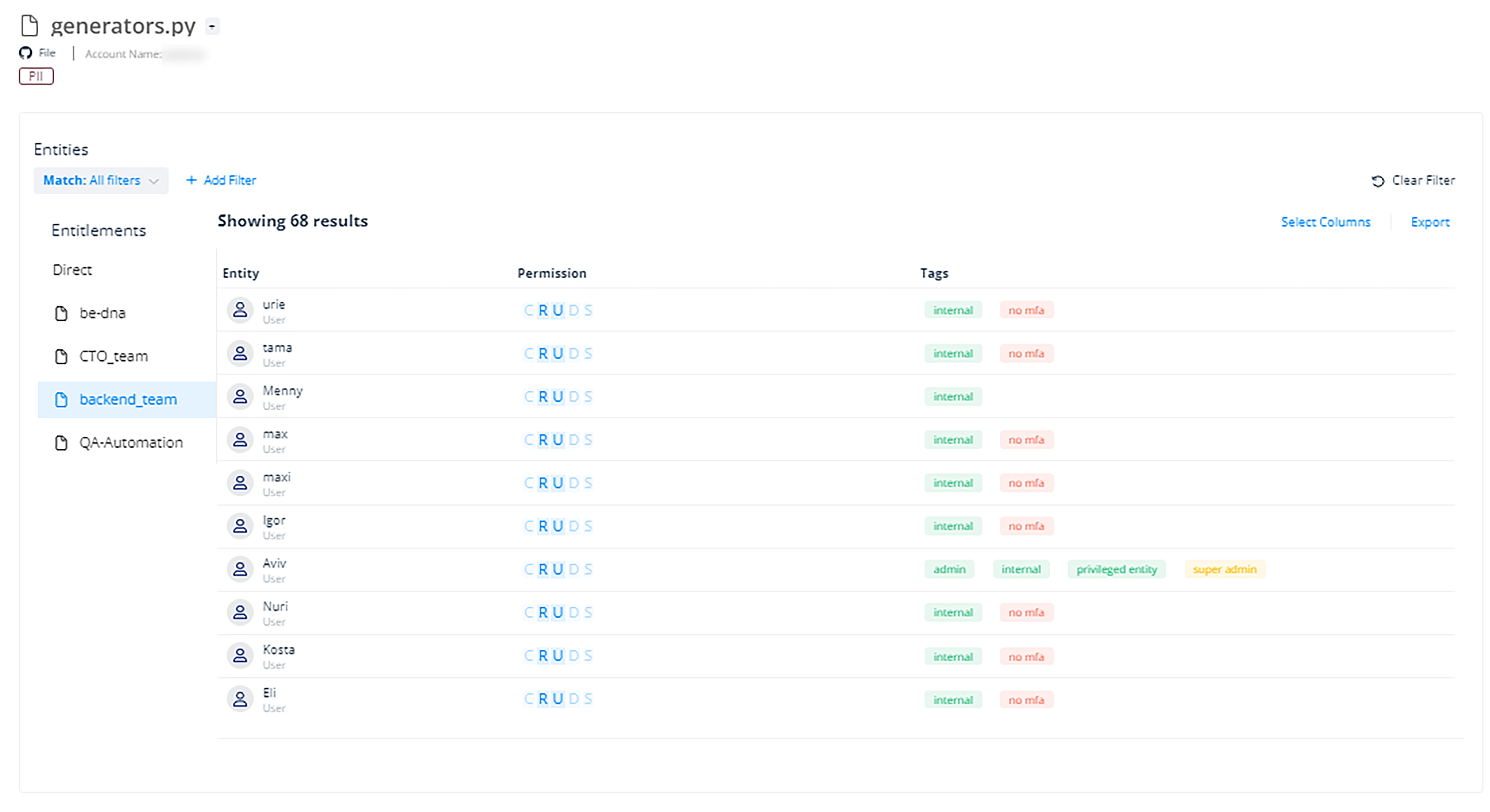 Varonis shows you who has access to your resources and their permissions down to the file level.
Varonis shows you who has access to your resources and their permissions down to the file level.
Varonis further identifies where your environment may be at risk by surfacing critical misconfigurations that open your corporate repositories up to risk, such as multi-factor authentication not being enabled for your org or all members having the right to create public pages or repositories by default. We then provide you with recommendations on how to take immediate steps to remediate any issues and reduce risk to your corporate repositories.
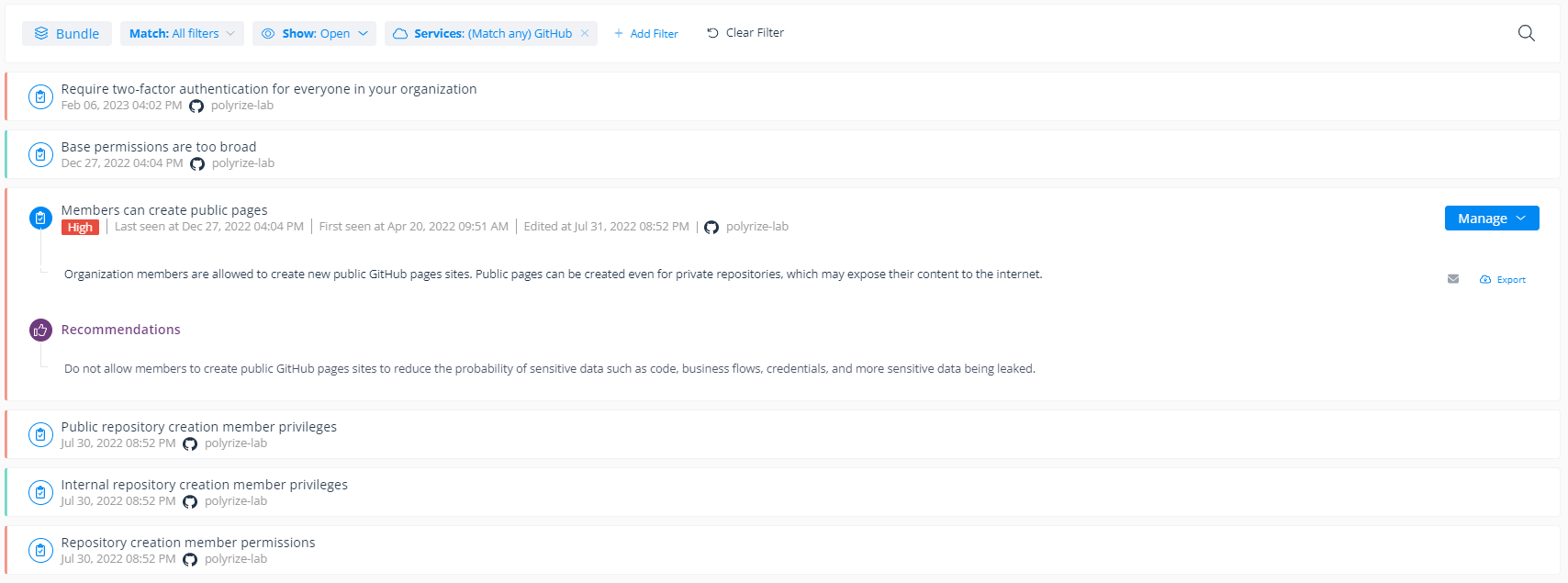 Varonis surfaces critical security gaps and misconfigurations to help improve your security posture.
Varonis surfaces critical security gaps and misconfigurations to help improve your security posture.
Detect and stop threats to your sensitive GitHub repositories.
To help mitigate risk and combat threats to your repositories, Varonis monitors user activity, including push events, file updates, repo creation and deletion, and more, to detect potentially risky behavior that may indicate an active threat to your sensitive GitHub repositories.
We’ll alert you to activity such as when external users are granted access to your sensitive private repositories, if they reshare them, and when your private repos are made public or deleted.
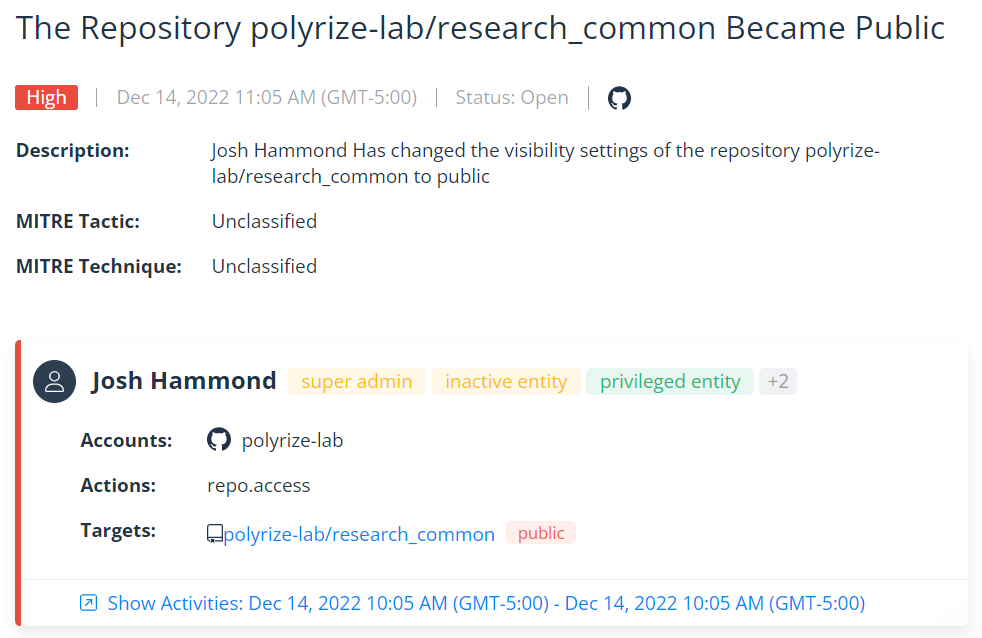 Varonis automatically detects risky or malicious behavior in your repositories.
Varonis automatically detects risky or malicious behavior in your repositories.
If an incident does occur, Varonis provides a complete and easy-to-read audit trail of events, so you can quickly investigate, pinpoint any affected resources, and begin any necessary recovery efforts.
Varonis’ audit trail tracks activity across your supported SaaS platforms to identify lateral movement and detect if any secrets or other sensitive data stored within your other SaaS platforms — like Google Workspace or Amazon S3 — were compromised.
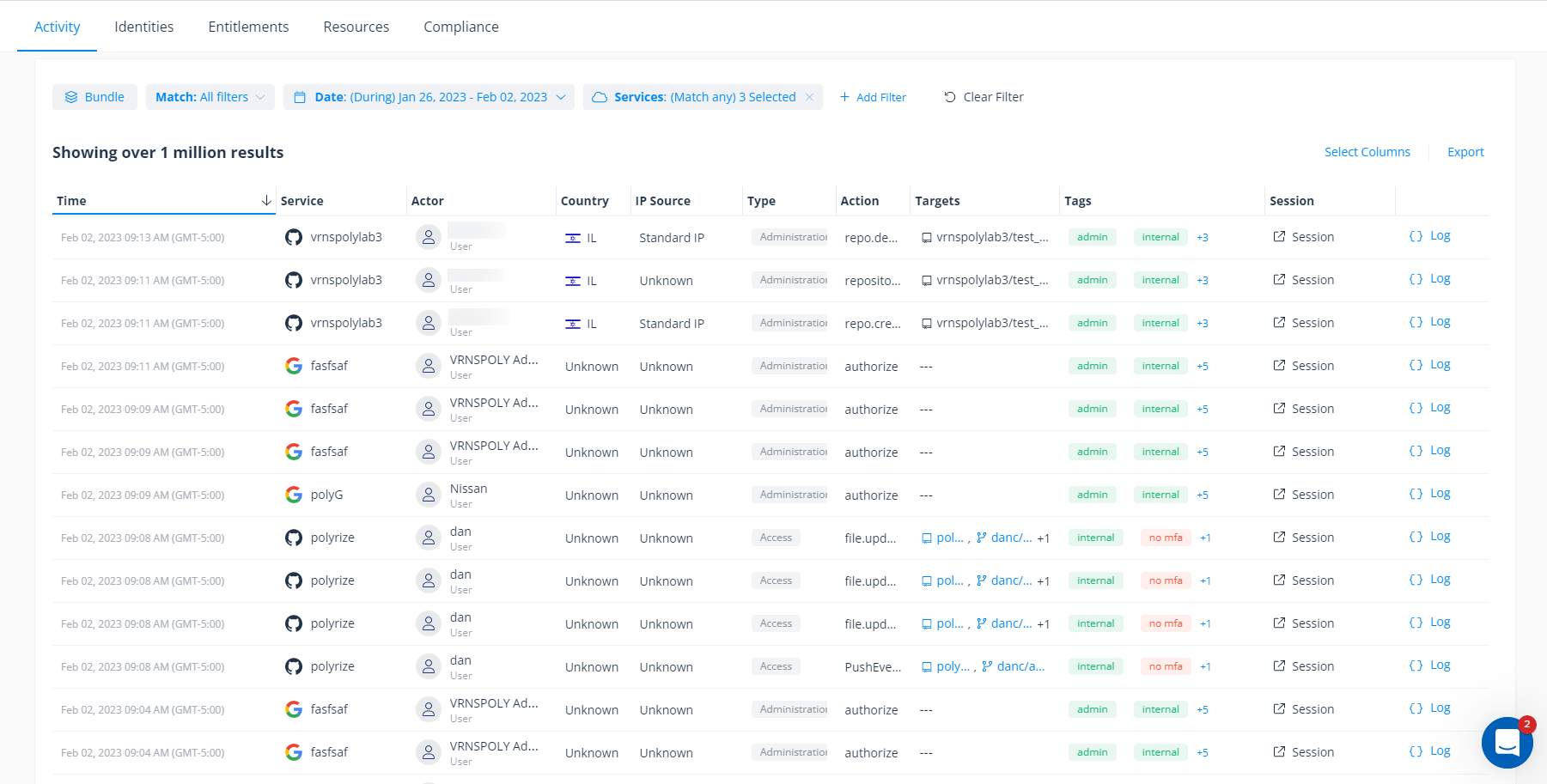 Varonis keeps a complete cross-cloud audit trail of events.
Varonis keeps a complete cross-cloud audit trail of events.
Secrets can hide in many different places, not just in your repositories.
Varonis doesn’t just scan your GitHub repositories to discover secrets. We also discover secrets exposed in plain-text files, such as Word documents, Excel spreadsheets, and Google Docs.
By scanning your code files — such as those stored in Amazon S3 buckets— Varonis can catch security issues like hardcoded private keys and credentials, or secrets stored improperly (like in a log file).
Request a Data Risk Assessment.
Varonis is quick and easy to set up. If you’re curious about where your secrets and other sensitive data may be exposed, request a free Data Risk Assessment.
In minutes, our engineers can get Varonis up and running to show you where your data is at risk and the steps you can take to lock it down.
What should I do now?
Below are three ways you can continue your journey to reduce data risk at your company:
Schedule a demo with us to see Varonis in action. We'll personalize the session to your org's data security needs and answer any questions.
See a sample of our Data Risk Assessment and learn the risks that could be lingering in your environment. Varonis' DRA is completely free and offers a clear path to automated remediation.
Follow us on LinkedIn, YouTube, and X (Twitter) for bite-sized insights on all things data security, including DSPM, threat detection, AI security, and more.

.png)





-1.png)