Discover and classify sensitive data across your AWS resources and workloads, fix misconfigurations, enforce least privilege, and detect threats with Varonis.
- Scalable
- Automated
- Actionable

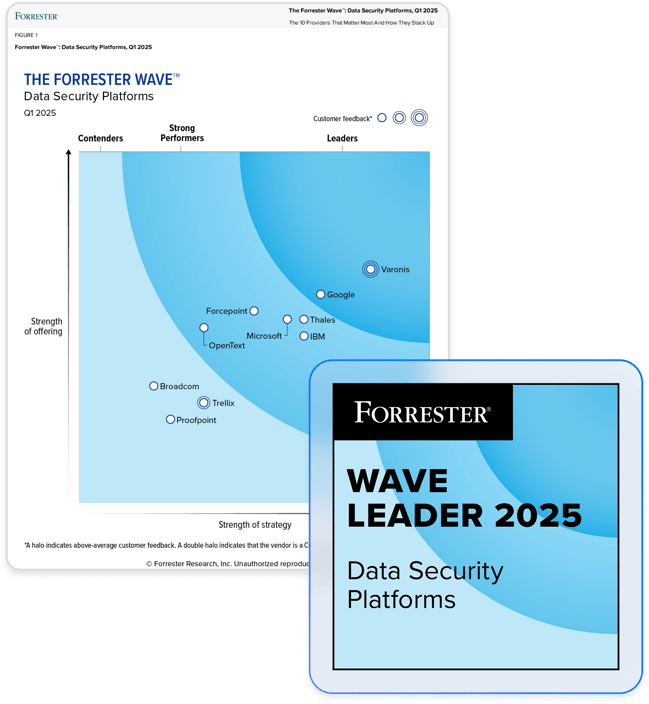
Partner with the leader in data security.
A proactive approach to AWS data security
Identify sensitive data in hard-to-find places
Varonis scans AWS to automatically discover and classify sensitive data across unstructured and structured resources with pinpoint accuracy and flags where data is at risk through excessive access and misconfigurations.
Map identities to data
Varonis provides a bi-directional mapping of identity data access, enabling you to visualize the AWS blast radius, identify exposure, and block access paths to data automatically.
Stop attackers and rogue insiders
With behavior-based detection, Varonis identifies suspicious activity – such as deleting S3 buckets, unusual access, escalating privileges, or disabling critical updates – that could put your AWS data at risk.
Limit data exposure in AWS
Varonis continuously surfaces security risks and misconfigurations that could expose your sensitive AWS data and broader cloud environment to risk. With automated remediation policies, Varonis fixes security issues, misconfigurations, and risky permissions to greatly reduce your blast radius.
“Without a solution like Varonis, achieving the level of data protection we needed would have required a lot of complex scripting and additional headcount.”
IT Manager
Read case studyVaronis solves common AWS data security challenges.
Data exposure from public AWS resources
- Automatically locate publicly exposed sensitive data across structured and unstructured AWS resources
- Visualize pathways to sensitive data and track third-party and external data access
- Create policies to automatically apply public access blocks and close pathways to sensitive data
Misconfigured APIs, buckets and accounts
- Find and automatically fix critical misconfigurations, including public data exposure
- Get a clear view of effective permissions in AWS with recommendations to consolidate privileges
- Remove unused admin accounts, stale privileged users, and terminated external contractors
Too many logs, not enough threat detection
- Easily correlate user activity across AWS and your entire cloud environment, all in a single interface
- Behavior-based threat policies detects abnormal activity, unauthorized access, and risky misconfigurations
- Track enrollment of new admins, admin account changes, and segregation of duty violations by admins
Varonis for AWS Demo
Protect your data, wherever it lives.
One platform for complete data security across multi-cloud, SaaS, hybrid, and AI.
AWS Security Resources
Ready to see the #1 Data Security Platform in action?
Ready to see the #1 Data Security Platform in action?
“I was amazed by how quickly Varonis was able to classify data and uncover potential data exposures during the free assessment. It was truly eye-opening.”
Michael Smith, CISO, HKS
"What I like about Varonis is that they come from a data-centric place. Other products protect the infrastructure, but they do nothing to protect your most precious commodity — your data."
Deborah Haworth, Director of Information Security, Penguin Random House
“Varonis’ support is unprecedented, and their team continues to evolve and improve their products to align with the rapid pace of industry evolution.”
Al Faella, CTO, Prospect Capital



.png)