In Varonis’ latest update of DatAdvantage Cloud, we’re layering MITRE ATT&CK tactics and techniques over our cloud alerts to aid in faster incident response. Mapping alerts to MITRE ATT&CK helps security teams better understand the alert's context, impact, and phase. Additionally, it can help inform how best to guard against attacks in the future.
The MITRE ATT&CK framework is a widely accepted framework for tracking various tactics and techniques that adversaries use throughout the different stages of a cyberattack. This framework helps security teams figure out how attackers gained access, what methods they used, and what their next move might be.
If you are a current DatAdvantage Cloud customer, you already have this additional layer of intelligence incorporated into your Alerts Dashboard.
Get a Free Data Risk Assessment
Improve response times
The MITRE ATT&CK framework helps organizations implement a common language and understanding of potential cyber threats within an organization. That way, when teams are communicating about exfiltration or lateral movement, for example, members know specifically which tactics are covered under those umbrellas and can better coordinate mitigation and prevention.
These new features will help you know which specific techniques and tactics attackers are most likely to use, along with how they'll probably behave, all from the console where you’re already doing your investigation.
.png?width=1034&name=MicrosoftTeams-image%20(5).png) Quickly see the relevant MITRE tactic and technique associated with each alert.
Quickly see the relevant MITRE tactic and technique associated with each alert.
Search by MITRE ATT&CK tactics and techniques
From the alert dashboard, you can filter alerts based on the MITRE ATT&CK tactic or techniques. This makes it easier to see where attackers are trying to penetrate and allows you to respond faster.
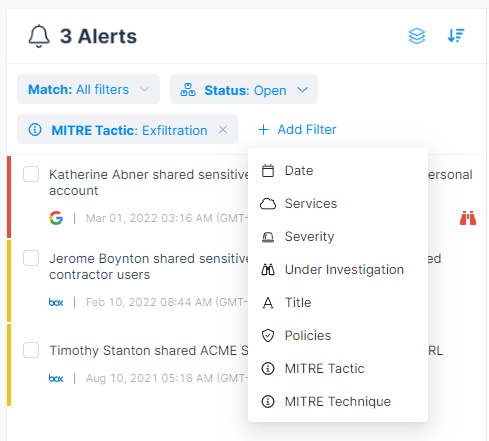 Easily filter your alerts by MITRE ATT&CK tactics and techniques.
Easily filter your alerts by MITRE ATT&CK tactics and techniques.
The full release notes and other product documentation are available in our customer community.
Threat detection across your cloud ecosystem
These new enhancements bolster Varonis’ already rich threat detection. Our detections include built-in alerts for specific cloud services (like a user accessing an abnormal number of records in Salesforce), pre-built alerts that span the cloud ecosystem (like a contractor accessing data after a long period of time), and custom alerts.
On top of alerting, DatAdvantage Cloud also finds sensitive data, analyzes effective permissions, pinpoints misconfigurations, and can help you close these security gaps across your cloud ecosystem.
Try DatAdvantage Cloud for free
DatAdvantage Cloud is free to try and easy to set up. Simply point DatAdvantage Cloud at your existing cloud services and identity providers without any complex architecture changes or proxies.
DatAdvantage Cloud correlates identities with privileges and activities across cloud apps, including AWS, Box, GitHub, Google Drive, Jira, Okta, Salesforce, Slack, and Zoom. Organizations can see and prioritize their biggest cloud risks in a single pane of glass. Get alerts on suspicious activity and policy violations and prevent cloud account takeovers, insider threats, and inadvertent policy violations with cross-cloud auditing and alerting.
What should I do now?
Below are three ways you can continue your journey to reduce data risk at your company:
Schedule a demo with us to see Varonis in action. We'll personalize the session to your org's data security needs and answer any questions.
See a sample of our Data Risk Assessment and learn the risks that could be lingering in your environment. Varonis' DRA is completely free and offers a clear path to automated remediation.
Follow us on LinkedIn, YouTube, and X (Twitter) for bite-sized insights on all things data security, including DSPM, threat detection, AI security, and more.




-1.png)


.png)
.png)