ShinyHunters is behind a new wave of data theft attacks on Salesforce instances.
Attackers are deploying a modified version of AuraInspector, an open-source tool developed by Mandiant (owned by Google). The tool itself is designed to help Salesforce admins audit for misconfigurations; however, ShinyHunters is abusing an exploit to find misconfigured sites that grant guest users access to more data than intended.
In this article, we'll share guidance on defending against this new attack.
Details about Salesforce Aura data theft attacks
Varonis Threat Labs discovered this misconfiguration exploit technique back in 2021, underscoring the need for security teams to continuously assess their exposure risk.
Misconfigured Salesforce Experience sites expose sensitive data
Publicly available Salesforce Experience (formerly Salesforce Community) sites can be misconfigured, leaving unauthenticated “guest users” with excessive permissions.
When this happens, anyone on the internet can query Salesforce objects that may contain sensitive data such as customer lists, support cases, contacts, users, and employee email addresses.
This attack is not a Salesforce Vulnerability
This attack is deemed a configuration issue rather than a vulnerability. The exposure stems from overly permissive guest user profiles, not from a flaw in Salesforce itself.
That said, the attack highlights a broader SaaS risk: security responsibility is shared, and misconfiguration can lead to real incidents. Attackers can exploit undocumented Salesforce APIs and sites that rely on Salesforce’s Lightning (Aura) framework.
Anonymous users can also interact with backend endpoints (notably /s/sfsites/aura) using normal HTTP requests.
If permissions allow, attackers can:
- Enumerate objects and fields
- List and retrieve records
- Query sensitive Salesforce data without authentication
This illustration shows how an attacker doesn't need to exploit anything to receive sensitive data from an organization's Salesforce instance.

This illustration shows how an attacker doesn't need to exploit anything to receive sensitive data from an organization's Salesforce instance.
The damage this attack can cause
Exposure to this attack enables recon and data theft. At a minimum, attackers can perform reconnaissance on your CRM data. This could mean harvesting names and emails for future spear-phishing campaigns.
In a worst-case scenario, attackers can exfiltrate large volumes of sensitive business, customer, and partner data and, in some cases, pivot to other integrated systems.

How Varonis defends against Salesforce misconfigurations
Varonis can catch this misconfiguration in your Salesforce instance before any real damage can be done.
Varonis has the following policy for detection purposes:
Abnormal Behavior: Potential data exfiltration via Salesforce site scan attempt
This policy is designed to detect whether someone is probing a site in an attempt to steal data.
Salesforce customers can review the standard and custom objects shared with guests in Salesforce itself via:
Salesforce Setup —> Security —> Guest User Sharing Rule Access Report
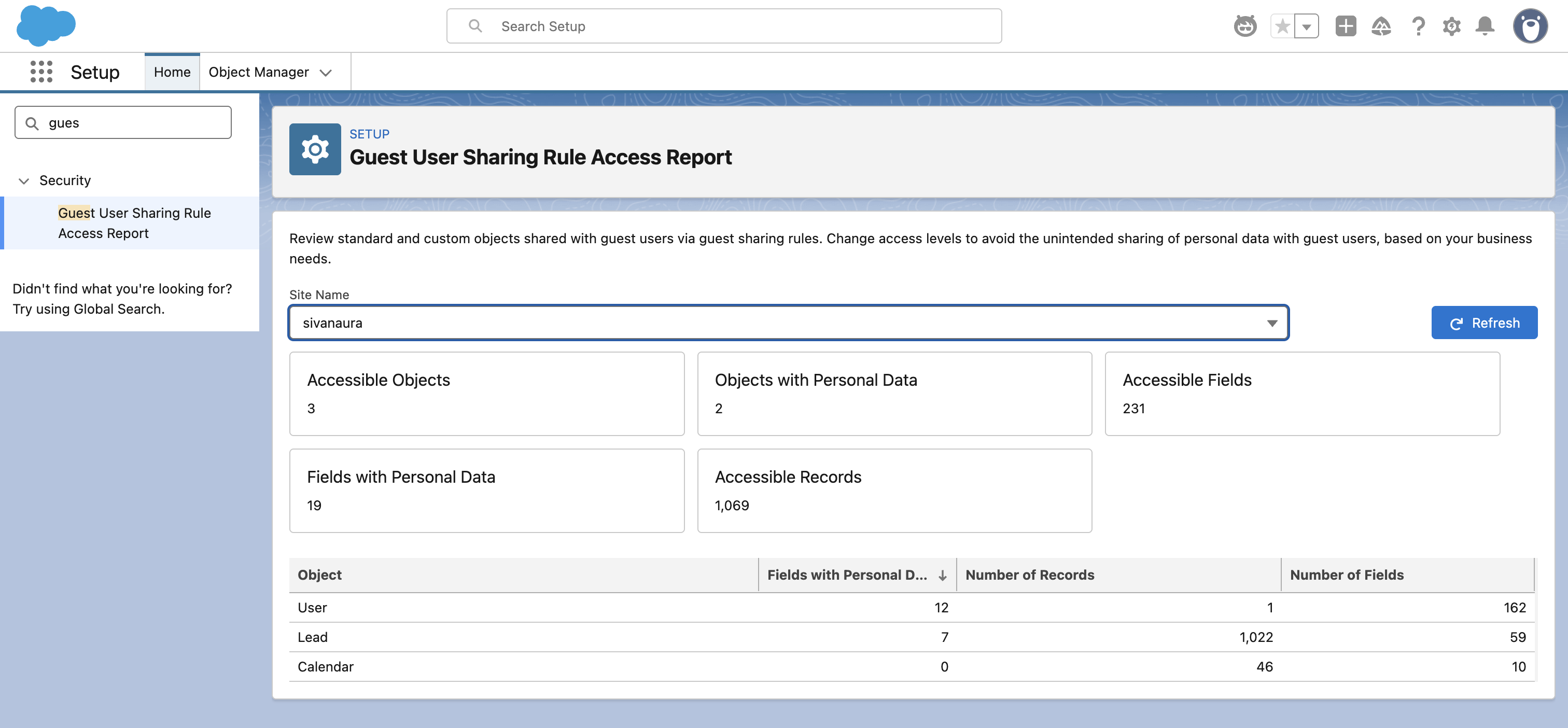
The risk itself will also be listed to Varonis users as:Salesforce guest users with access to records via Sharing Rules
For a deeper technical dive into the attack, you can read more in our discovery blog.
Worried about your Salesforce exposure?
To stay ahead of these attackers, organizations need to combine strong technical controls with effective user education. The best way to understand your Salesforce data security posture and assess whether these attacks pose a real threat is with a free Salesforce Data Risk Assessment from Varonis.
Varonis Salesforce Data Risk Assessments do more than highlight risk. They provide clear, actionable recommendations to simplify permissions and improve security. See what Varonis for Salesforce can do in this quick four‑minute demo.
What should I do now?
Below are three ways you can continue your journey to reduce data risk at your company:
Schedule a demo with us to see Varonis in action. We'll personalize the session to your org's data security needs and answer any questions.
See a sample of our Data Risk Assessment and learn the risks that could be lingering in your environment. Varonis' DRA is completely free and offers a clear path to automated remediation.
Follow us on LinkedIn, YouTube, and X (Twitter) for bite-sized insights on all things data security, including DSPM, threat detection, AI security, and more.


.png)




