Hackers are getting savvier. They’re constantly finding new ways to abuse system vulnerabilities and sneak into our networks. The worst part? The likelihood of a cyber attack is now higher than a home invasion. Most people don’t notice when their data has been compromised until it’s too late. The silver lining is that the rise in attacks allows us to analyze the patterns hackers follow and strengthen our defenses.
Major cybersecurity attacks of the past have taught us hard lessons, including the need for CSOs to embrace data-centric security. Massive breaches like the Marriott data breach also taught us the importance of effectively managing mergers and acquisitions, especially when the company you’re acquiring has a recent history of breaches and hacks.
We took a look at hacks in the past years and identified the most important trends you should watch to ensure your business’s safety. We’ve also included a few tips to make sure your company doesn’t become another victim.
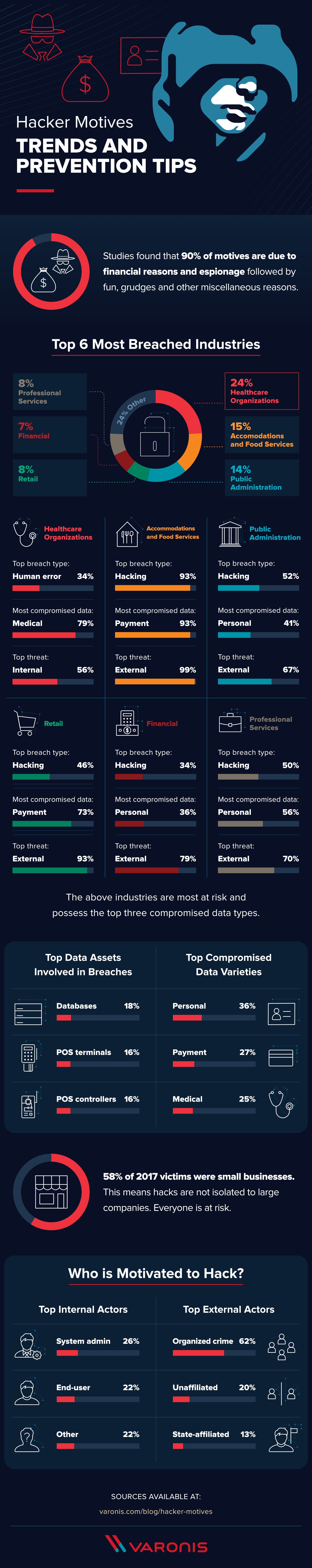
Every company has data to protect. Whether you’re a multi-million dollar enterprise or a 6-month-old startup, each business has its own set of vulnerabilities. Larger companies have complex systems and lots of data to monitor, thus making it easier for hackers to infiltrate and persist for long periods of time while staying undetected. Small businesses, on the other hand, are likely less prepared to handle a cyber attack due to a lack of resources or staff. Take a look at some of our tips below to see what you can do to stay ahead of these hacker trends.
Preparation and a quick response time are essentials for any security team. It’s smart to start with engage in effective threat modeling and create a comprehensive incident response plan to keep your team vigilant and ready for threats. Taking advice from other professionals through cybersecurity TED talks or podcasts can also jump start your security planning to see what threats and solutions are top-of-mind for others in the industry. To get started, take our data risk assessment to see where your vulnerabilities lie and what steps you need to take to keep your company safe.
Sources: Verizon | HackerOne | IBM
What should I do now?
Below are three ways you can continue your journey to reduce data risk at your company:
Schedule a demo with us to see Varonis in action. We'll personalize the session to your org's data security needs and answer any questions.
See a sample of our Data Risk Assessment and learn the risks that could be lingering in your environment. Varonis' DRA is completely free and offers a clear path to automated remediation.
Follow us on LinkedIn, YouTube, and X (Twitter) for bite-sized insights on all things data security, including DSPM, threat detection, AI security, and more.










-1.png)