Varonis Threat Labs uncovered 1Campaign, a full-service cloaking platform built to help threat actors run malicious Google Ads at scale. The tool passes Google's screening, filters out security researchers, and keeps phishing and crypto drainer pages online for as long as possible, funneling real users to attacker-controlled sites.
The developer behind it, operating under the handle DuppyMeister, has been maintaining the platform for over three years with dedicated Telegram channels for support. It combines real-time visitor filtering, fraud scoring, geographic targeting, and a bot guard script generator into a single dashboard.
1Campaign's login page with admin & guest access options.

1Campaign's login page with admin & guest access options.
What 1Campaign does
At its core, 1Campaign is a cloaker. Cloaking is a technique where malicious actors show different content to different visitors. Security researchers, ad platform reviewers, and automated scanners see a harmless "white page," while real victims see the actual phishing or scam content. This allows fraudulent Google Ads campaigns to pass initial review and stay active longer before being flagged.
The platform goes beyond basic cloaking. It includes real-time analytics, visitor profiling, fraud scoring, and the ability to block traffic from known security vendors, data centers, and VPNs. Operators can configure exactly who sees their malicious content and who gets redirected to a benign page.
The main dashboard, showing 4.3K visitors with 99.2% blocked.
The main dashboard, showing 4.3K visitors with 99.2% blocked.
Visitor filtering and fraud scoring
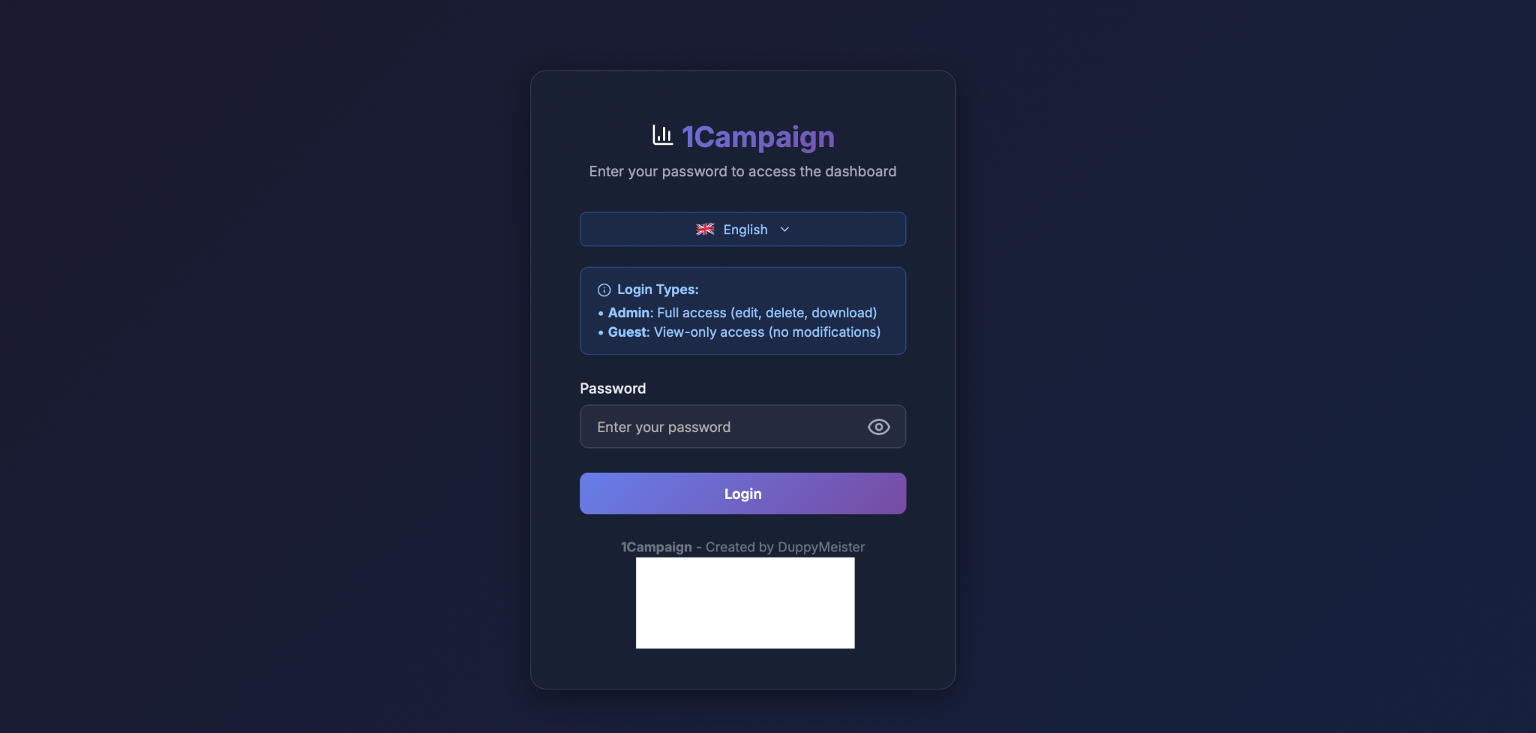
The dashboard shows detailed statistics on every visitor. In the screenshots we analyzed, one campaign called "Blockbyblockchain" targeting bitcoinhorizon.pro had processed 1,676 total visitors but only approved 10, a 0.6% success rate. The other 99.4% were blocked.
Each visitor is assigned a fraud score from 0 to 100. Visitors from Microsoft Corporation, Google, Tencent Cloud Computing, OVH Hosting, and other cloud providers are automatically flagged with high fraud scores and blocked. The system identifies security scanners by their IP ranges, ISPs, and behavioral patterns.
Visitor logs showing IP addresses, locations, fraud scores, & block status.

Visitor logs showing IP addresses, locations, fraud scores, & block status.
The visitor log captures IP address, geographic location, company or ISP, device type, security flags, fraud score, action taken, and destination URL. Entries from Microsoft Corporation in Amsterdam show fraud scores of 0 but are still blocked, indicating the platform recognizes these as automated scanners regardless of score. Traffic from security and cloud providers like 3xK Tech, GSL Networks, Level 3 Communications, and Tencent is blocked with fraud scores of 100.
Geographic and device targeting
Operators can restrict their campaigns to specific countries and device types. The analytics show traffic distribution across the US, Netherlands, Canada, China, Germany, France, Hungary, Albania, and Japan. Device breakdown shows the split between desktop and mobile visitors.
This selective targeting serves two purposes. First, it allows attackers to focus on victims in regions where their phishing content is relevant. Second, it filters out traffic from countries where security researchers and automated scanners commonly operate.
Geographic distribution & device breakdown of campaign visitors.
Geographic distribution & device breakdown of campaign visitors.
Google Ads launcher
For operators running Google Ads campaigns, 1Campaign includes an assistant platform that helps launch both "black" (malicious) and "white" (benign) search campaigns. The developer claims this feature allows users to bypass Google Ads policy limitations and launch ads "as anyone using any text or words" in advertisement headings and descriptions.
The official advertisement listing 1Campaign's capabilities.
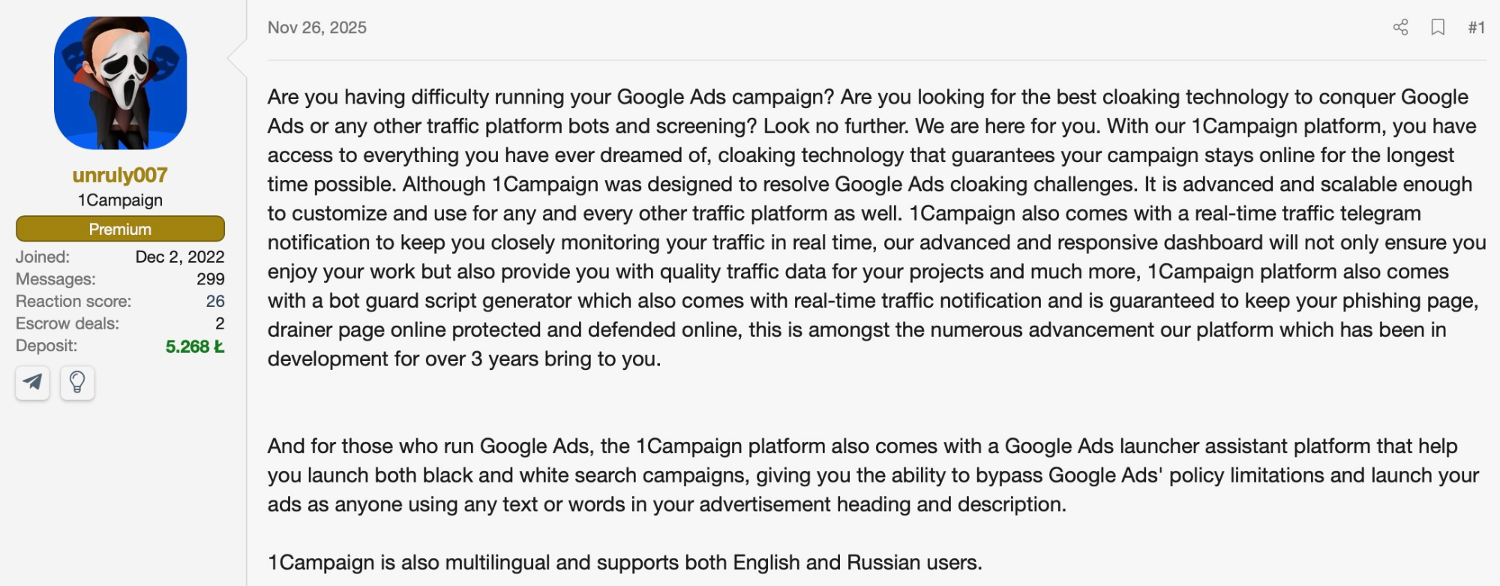
The official advertisement listing 1Campaign's capabilities.
This directly enables ad fraud at scale, allowing attackers to impersonate legitimate brands and services in their Google Ads campaigns while evading automated policy enforcement.
Part of a growing trend
1Campaign fits a pattern we continue to see across phishing infrastructure. Feature-packed toolkits are making it easier than ever for attackers to launch campaigns without technical expertise. We've covered similar platforms in recent research, including Spiderman, a phishing kit targeting European banks with built-in ISP whitelisting and geo-blocking, FishXProxy, which leverages Cloudflare infrastructure to evade takedowns, and AI-powered cloaking services that use machine learning to distinguish real victims from security scanners.
What makes 1Campaign different is its explicit focus on Google Ads abuse. While other tools cloak phishing pages from scanners, this platform is built specifically to help malicious ad campaigns pass Google's review process and stay active longer. The combination of ad fraud tooling and phishing infrastructure protection in a single platform represents a dangerous convergence.
The core distribution method enabled by 1Campaign is malvertising, where attackers purchase legitimate ad placements on Google, Bing, or social platforms to drive traffic to phishing pages, fake software downloads, or malware droppers. Because the cloaking filters out Google's ad reviewers and security scanners, the malicious ads pass inspection and run until victims report them or the campaign is manually flagged. By the time the ads are taken down, the attacker has already captured credentials, distributed malware, or drained crypto wallets.
Implications for defenders
Cloaking platforms like 1Campaign directly undermine traditional phishing detection workflows. URL scanners, brand protection services, and automated crawlers are being fingerprinted and filtered before they ever see malicious content. The 99%+ block rates visible in these dashboards demonstrate how effectively these tools identify and exclude security infrastructure.
The filtering logic targets multiple layers: IP reputation (blocking known data centers, cloud providers, and VPN exit nodes), ISP identification (flagging Microsoft, Google, Tencent, and security vendors by ASN), device fingerprinting (detecting headless browsers and automation frameworks), and behavioral analysis (flagging rapid page loads, missing JavaScript execution, or inconsistent user-agent strings).
For detection teams, this means static URL scanning is more unreliable for cloaked infrastructure. Effective analysis requires realistic browser fingerprints, and human-like interaction patterns. Automated systems should rotate through diverse IP pools and user-agent configurations to avoid consistent fingerprinting.
This is exactly where Varonis Interceptor changes the equation. Interceptor's phishing sandbox follows the user's path to the very end, going past every form fill, CAPTCHA, and authentication gate. By emulating real user behavior rather than acting like a scanner, Interceptor sees what cloaking platforms are designed to hide. It analyzes over 100 million URLs daily and often identifies malicious sites before any other security tool or human analyst, catching the malicious web pages that 1Campaign is built to protect.
Indicators of compromise
Phishing Domain (observed in campaign):
bitcoinhorizon.pro
Developer Username:
DuppyMeister
What should I do now?
Below are three ways you can continue your journey to reduce data risk at your company:
Schedule a demo with us to see Varonis in action. We'll personalize the session to your org's data security needs and answer any questions.
See a sample of our Data Risk Assessment and learn the risks that could be lingering in your environment. Varonis' DRA is completely free and offers a clear path to automated remediation.
Follow us on LinkedIn, YouTube, and X (Twitter) for bite-sized insights on all things data security, including DSPM, threat detection, AI security, and more.









