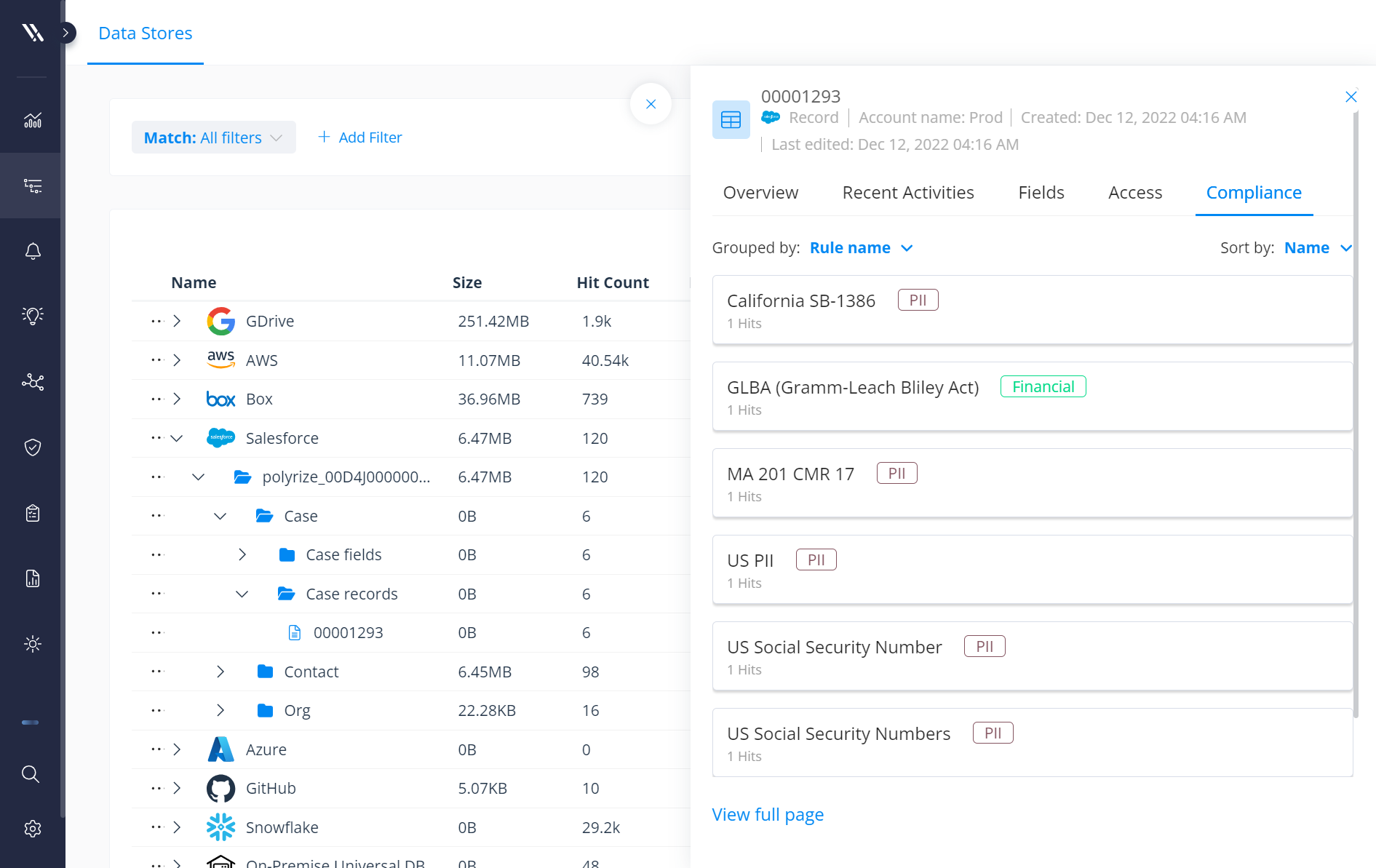
As the market’s leading CRM, Salesforce houses some of your organization’s most valuable data — whether that’s customer and prospect information, contracts, or support cases. Many security teams don’t realize the depth and breadth at which Salesforce acquires and houses information — and how complicated it is to protect it.
For example, if a bank were to build an app using Salesforce, guess what would happen when you upload your financial documents with your mortgage application? All that information ends up in Salesforce as records, files, and attachments. Salesforce can classify the structured fields, but there’s no way to find, classify, or protect files and attachments natively in Salesforce.
Enter Varonis for Salesforce — agentless, cloud-native data security that deploys in 15 minutes.
See Varonis for Salesforce in action with this quick 4-minute demo.
Varonis for Salesforce allows you to locate and control hard-to-find regulated data across all your Salesforce instances. Whether it’s stored in records and fields or files and attachments, we’ll find, surface, and protect it:
- Prepare your instance for the Agentforce rollout: Run AI agents safely and keep your systems secure with Varonis. Identify sensitive data, rightsize data access privileges, and monitor system usage in real-time.
- Classify sensitive data in records and fields: Varonis scans Salesforce to accurately discover and classify sensitive data stored within records and fields.
- Classify sensitive files and attachments: Varonis is the only product on the market that can look inside files attached to objects in Salesforce and auto-tag sensitive items.
- Monitor your Salesforce Security Posture: The Varonis Salesforce dashboard provides a comprehensive overview of your Salesforce security posture at a glance.
- Understand exposure in Salesforce: Calculate net-effective permissions with a simple bi-directional view to quickly answer, "Who has access to sensitive data?"
- Right-size permissions: Reduce exposure and fix compliance gaps, such as automatically remediating public links and disabling ex-contractors and guest users who still have unnecessary access.
- Detect anomalous activity: Monitor user behavior and alert on data exfiltration attempts by insiders and malicious actors.
- Enhance Salesforce Shield: Enhance Salesforce Shield with a human-readable audit trail of events, enriched alerts, and ready-made alerts.
-
Pinpoint and fix misconfigurations: Detect org-wide settings problems, discover shadow instances, and spot vulnerabilities.
-
Manage third-party app risk: Identify and reduce third-party app risk.
Read on for an in-depth look at how each of these features helps identify and remove your most critical Salesforce risks.
Discover and classify sensitive data across Salesforce — no matter where it lives.
Sensitive and regulated data can sprawl across Salesforce, hiding in many places — some in places you’d expect and others where you may not think to check.
Varonis discovers and classifies sensitive and regulated data across your Salesforce environment with pinpoint accuracy. We identify where sensitive data lives in each object’s records and fields — including your notes field!
It’s easy to assume you know where PII lives within your Salesforce records and fields. Phone numbers are in the phone field, addresses are in the address field, email addresses are in the email field, and so on, but that’s not always the case. Often, sales and marketing reps may enter sensitive or even regulated data into the notes field, which you may not immediately think to check. But not to worry — if sensitive data is stored in Salesforce, Varonis will surface and protect it.
Discover sensitive data stored in records and fields.
Discover sensitive data stored in records and fields.
In addition to helping you classify certain fields as sensitive, Varonis can find sensitive data attached to different records. The Salesforce security market has been missing this capability — until now.
Only Varonis can scan the contents of all your files and attachments, find sensitive data using our vast classification library, and then pair those classification results with permissions so that you can see exactly where data is exposed.
Quickly see where sensitive data is concentrated and exposed.
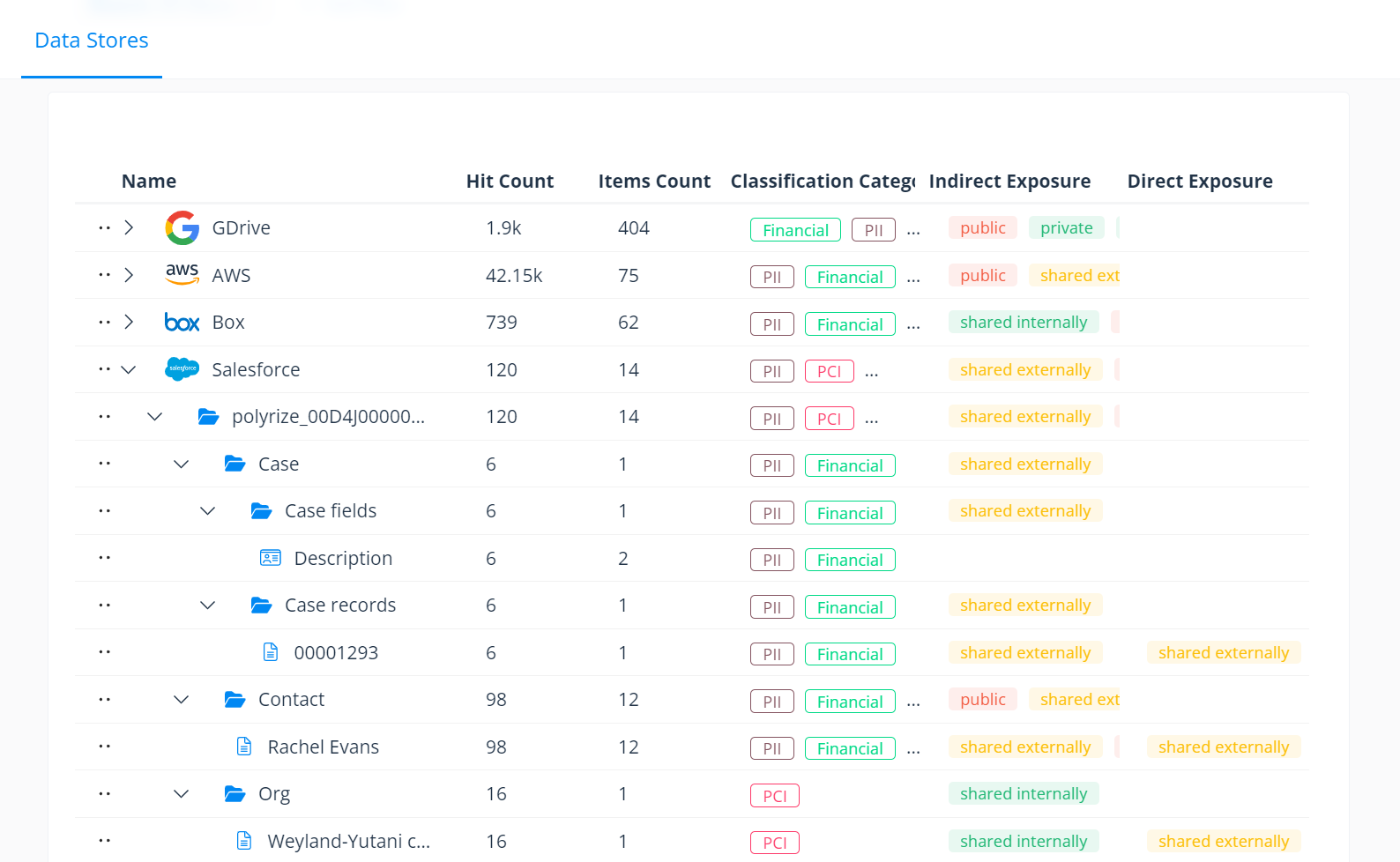
Quickly see where sensitive data is concentrated and exposed.
Varonis’ classification goes beyond regular expressions and includes pre-built databases of known valid values, proximity-matching, negative keywords, and an algorithmic verification to generate highly accurate results. The same classification engine that has made Varonis a leader in data classification for more than a decade now extends to the hardest-to-find files in Salesforce. With this new release, you can analyze classification results quickly and easily.
We show you exactly where sensitive data exists in the documents and color code results. Now, you can easily “trust but verify” all classification results.
File analysis shows exactly where classification results are found within documents, records, and fields.
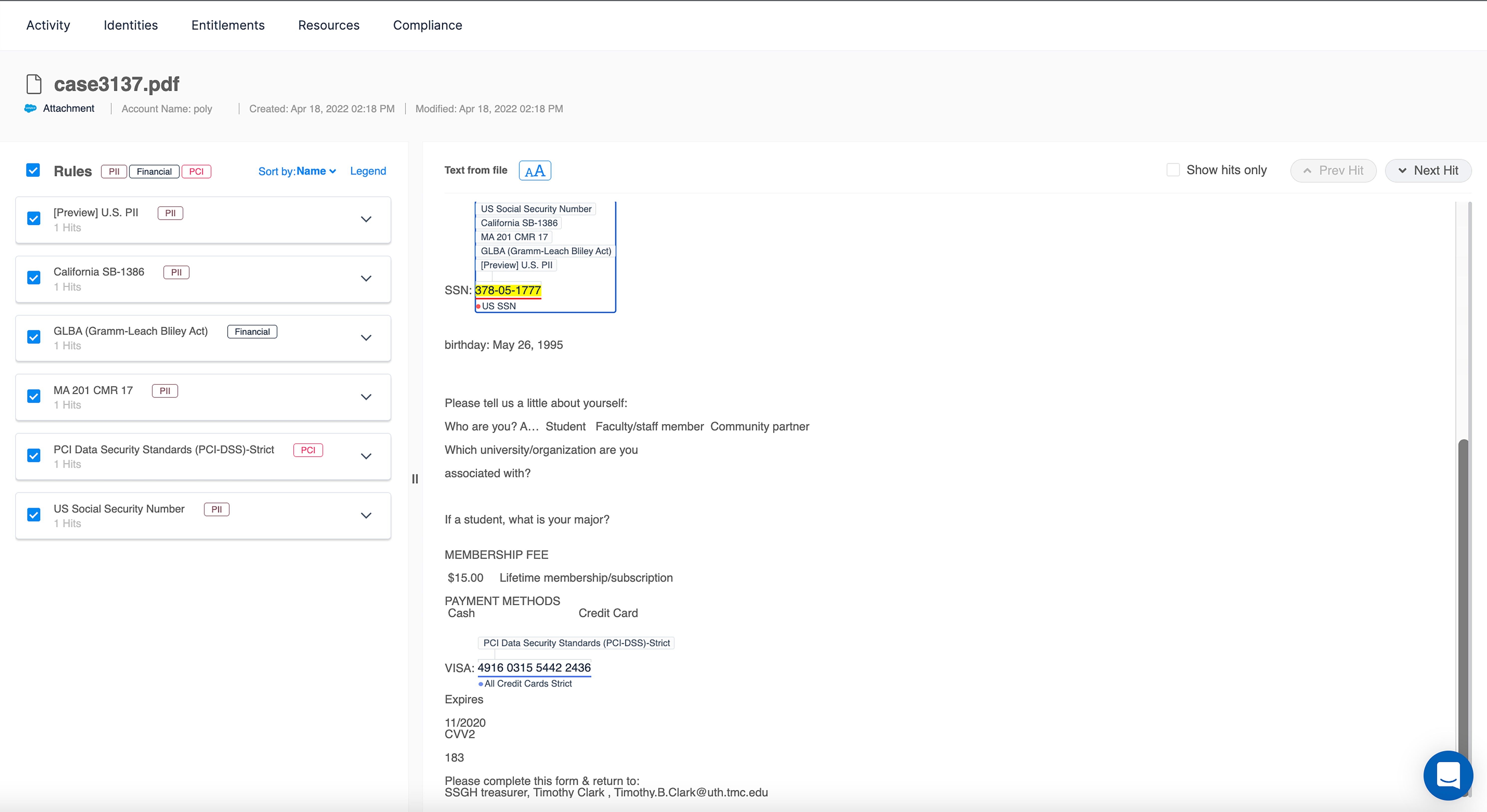
File analysis shows exactly where classification results are found within documents, records, and fields.
Manage your Agentforce agents
Salesforce Agentforce agents inherit the permissions of the users who run them, so if users have excessive access, agents can expose sensitive data.
Varonis for Agentforce is the first data security company to cover autonomous AI agents allowing security teams to monitor agent activity, detect abnormal usage, and continuously minimize blast radius.
Monitor how Agentforce agents access, create, and edit your Salesforce data
Monitor how Agentforce agents access, create, and edit your Salesforce data
Our team outlined the three essential tactics you can use to make sure that your Salesforce instance is ready for a safe deployment of Agentforce.
Salesforce dashboard
The Varonis Salesforce dashboard provides a centralized overview of your Salesforce security posture, enabling you to visualize where your sensitive data may be at risk and where technical debt is building up.
Monitor your Salesforce Orgs with key risk indicators, including:
- Overexposed sensitive records
- Open misconfigurations sorted by severity
- Guest user access
- Users assigned a toxic combination of permissions
Drill down from these widgets to begin remediating risks and cleaning up technical debt across your Salesforce Orgs.
Easily assess your Salesforce security posture with an intuitive interface.
Easily assess your Salesforce security posture with an intuitive interface.
Effective permissions
Varonis radically simplifies permissions analysis, showing you not only what someone’s net effective permissions are but also how they got them.
Now, instead of clicking into every user’s profile and then clicking into every single one of their Permission Sets, you can see all their effective permissions from one screen. Hovering over a checkmark shows you how that user gained access, or you can add permission sets to the column view to see everything side-by-side. This permissions view gives security teams unprecedented visibility into risks and overexposure in their environment.
The permissions view shows aggregated, effective permissions on one screen.
The permissions view shows aggregated, effective permissions on one screen.
Single permissions tracking
On top of seeing what permissions a single user has, you can also see which group of users have a certain permission, such as, “Who has export access?”
Varonis’ bidirectional view of permissions in Salesforce enables you to click on a single system permission, such as “export reports,” to easily review the profiles and users that have this specific permission. With single permissions tracking, you’ll be able to better understand your blast radius and quickly identify any accounts with risky or toxic combinations of permissions.
View each user and Profile with the "export reports" permission.
View each user and Profile with the "export reports" permission.
Record and field-level permissions
In a sales organization with frequently changing territories and roles, it’s easy to see how permission sets can get out of hand. Varonis empowers security teams to take back control of sprawling permissions and dramatically reduce their risk.
On top of system-level permissions, Varonis extends visibility to the record and field level. We simplify access into a simple CRUDS model (create, read, update, delete, share) and show you exactly what level of access someone has to every object and field in your environment and how they gained that access.
Varonis analyzes permissions down to the object and field level.
Varonis analyzes permissions down to the object and field level.
In addition to seeing everything an individual user can access, you can also go the other route and take specific records and determine all the users who can access them. If you know certain records are sensitive, you’d want to make sure that only the right people could access them.
Easily see exactly who can access a specific record.
Easily see exactly who can access a specific record.
Within a specific record, you can drill down into the specific fields. You can quickly see the simplified CRUDS view of access and a more detailed view to see which permission sets give that access.
We had eight instances of Salesforce — and it was a gaping black hole. I’d heard horror stories about Salesforce permissions and how literally hundreds can be applied in a manner of different ways, but I didn’t realize how complicated our permission sets had grown.
Tony Hamil, Senior Cybersecurity Engineer, Top Real Estate Organization
Unauthorized access to data
When someone leaves the company, you want to make sure they can’t access your corporate data anymore. Shockingly, three out of four ex-contractors can still access sensitive data after they’ve left the company. Varonis ties identities together across platforms to help you easily spot offboarding gaps, unsanctioned personal account use, or other compliance violations.
Varonis ties related identities together automatically.
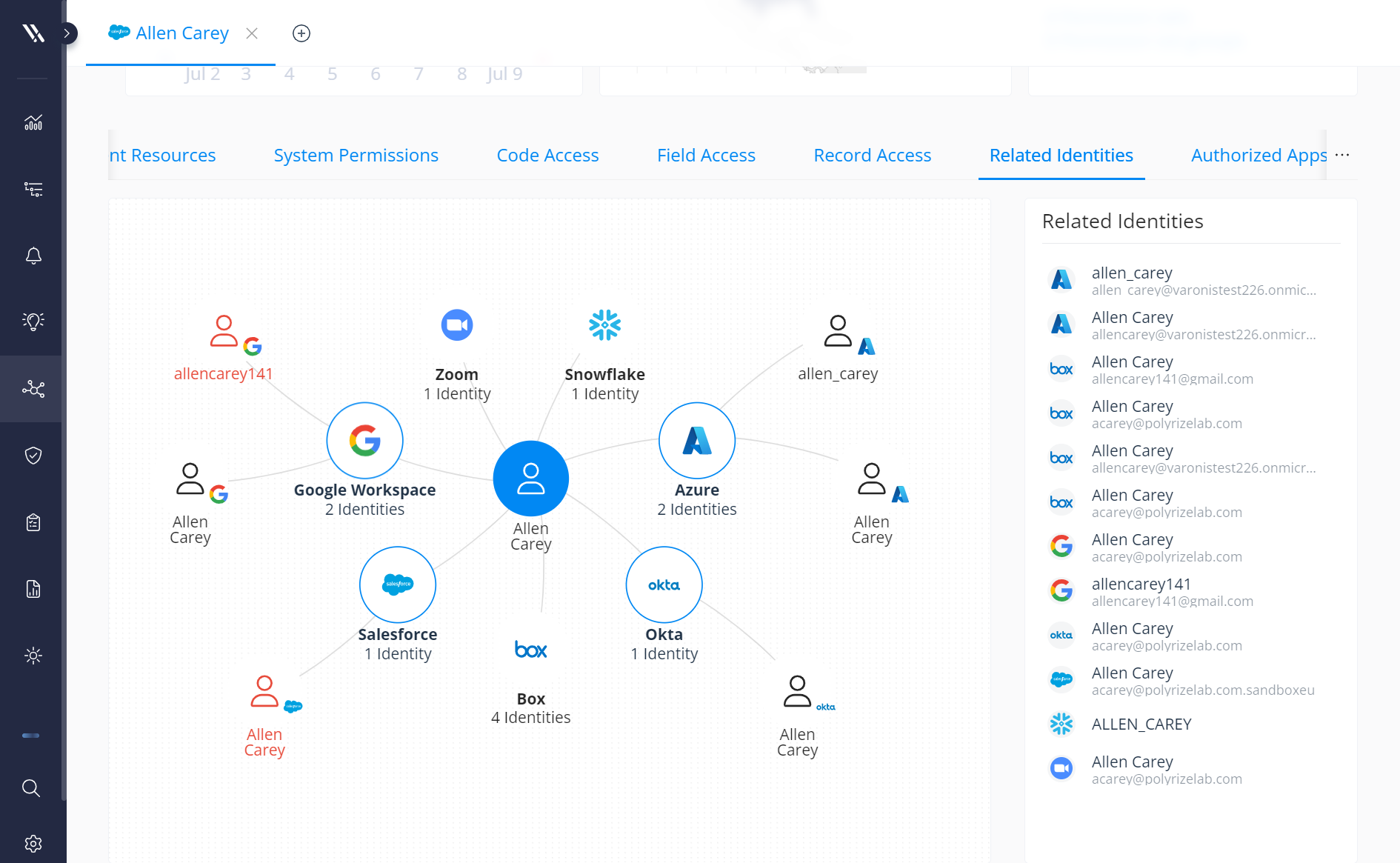
Varonis ties related identities together automatically.
Identify and remediate public link exposure.
Public links enable users to share files and attachments from your Salesforce Orgs with anyone. If they have the link, they can access your data.
Public links pose a significant risk to organizations and, without the proper configuration insights and remediation controls, expose critical attachments such as sales contracts, pricing info, support tickets, and more.
Varonis continuously monitors your Salesforce environment to identify where users share sensitive Salesforce data using public links and provide valuable insights such as:
- Who created the link
- Whether the link has sensitive data
- The last time the link was used
- If it’s password-protected
- Its related records
We then enable you to automatically and continuously remove public links from your Salesforce Orgs to help reduce sensitive data exposure.
Remove Salesforce public links directly from the Varonis UI.
Remove Salesforce public links directly from the Varonis UI.
Varonis not only helps you find and remove Salesforce public links, but it also allows you to easily identify the entitlements that grant permission to create public links. You can then revoke the permission from those who shouldn't have it to drastically reduce your blast radius in seconds.
Revoke the “create public link” permission from entitlements in only a few clicks.
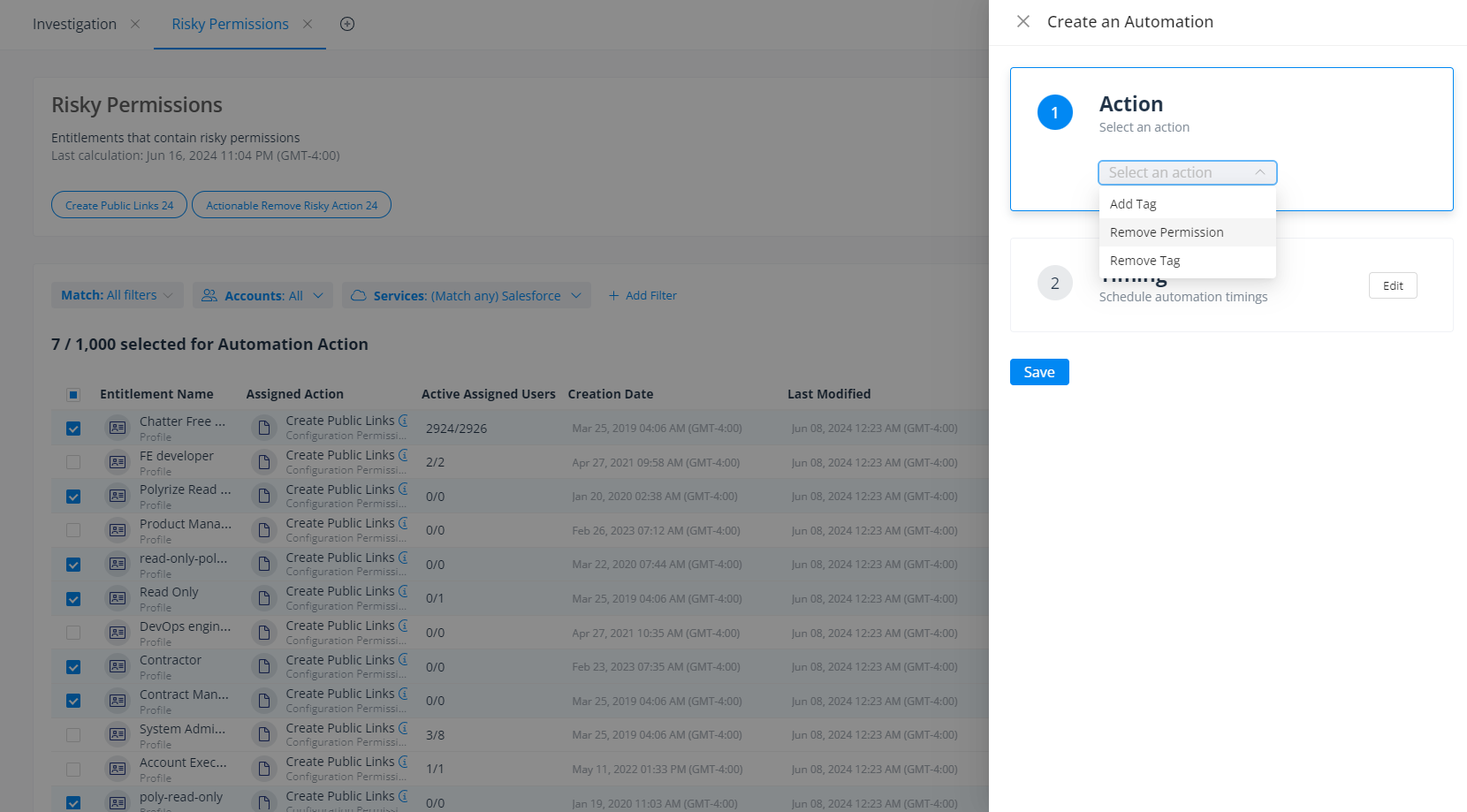
Revoke the “create public link” permission from entitlements in only a few clicks.
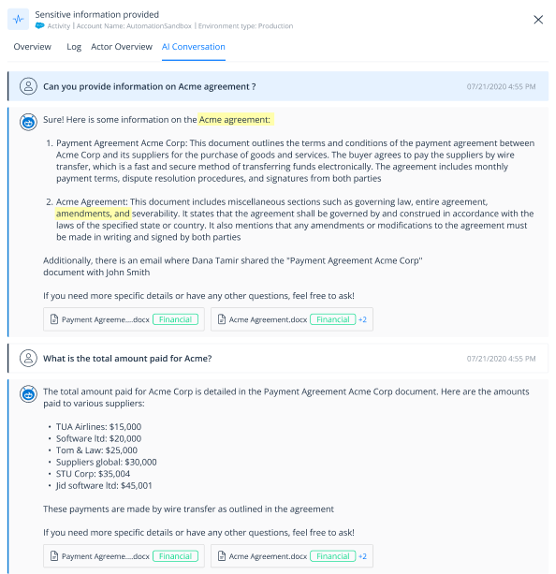
Detect anomalous activity
Varonis monitors Salesforce — and your broader SaaS environment — for suspicious activity. Our out-of-the-box alerts can detect internal and external threats, such as a user accessing an unusual number of Salesforce objects, deactivating a critical update, or escalating privileges. On top of built-in alerts, you can easily configure your own alerts without writing any Apex code. All of our alerts are mapped to MITRE ATT&CK for quick investigations.
The Alerts Dashboard shows risky activity happening across your SaaS ecosystem.
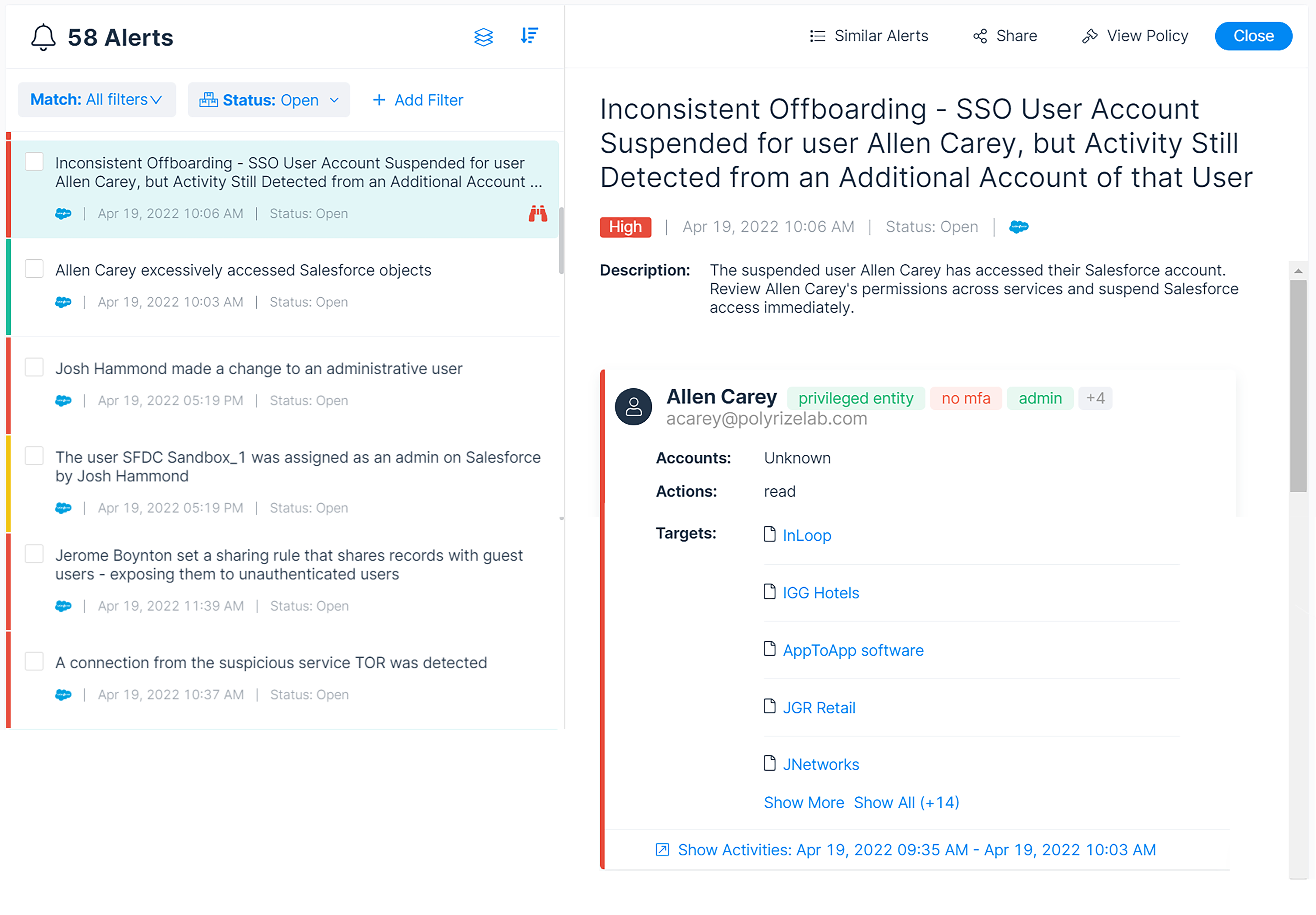
The Alerts Dashboard shows risky activity happening across your SaaS ecosystem.
Because we’re monitoring multiple SaaS apps in one platform, it’s easy to investigate incidents across your environment. We enrich events and correlate identities across cloud apps, making it easy to see something like a user logging in through Okta, accessing records in Salesforce, and then using their personal Gmail account to email themselves data.
Enhance Salesforce Shield
Salesforce Shield provides over 40 different event types. The catch, however, is that each event is presented in raw log form and is siloed from other related events. To gain any actionable insights into where sensitive data is at risk, you need to do a lot of manual parsing, analysis, and correlation to know if your sensitive data is being misused or is under attack.
Varonis pulls in events that can only be captured by Shield, including reports activity, REST API activity, Aura requests, Lightning interactions, and more. We then enrich each event with user details and data sensitivity, presenting them all in a unified and searchable audit trail of events. With Varonis, you can conduct investigations quickly, even without knowing Salesforce’s log format.
Investigate Salesforce events using Varonis' human-readable audit trail.

Investigate Salesforce events using Varonis' human-readable audit trail.
Although Salesforce Shield collects logs, it does not come with out-of-the-box alerts. Users need to create alerts manually using Apex code. Varonis comes with ready-made alerts created by our Threat Labs team and Salesforce experts. Some of the suspicious activity we can detect includes users creating and exporting reports, new sites with guest users being created, and other activities that can open you up to risk.
You also can easily create and customize Varonis' alerts to fit your Salesforce Org’s specific needs — all without having to use Apex code.
Find misconfigurations
Excessive permissions are a major way sensitive data can end up exposed, but misconfigurations are another way data can be at risk. Given how configurable Salesforce is, it’s easy to miss a checkbox somewhere along the line — and these misconfigurations can create big gaps in your security posture.
Varonis highlights these misconfigurations in our SaaS Security Posture Management (SSPM) Insights Dashboard. You can also compare your configurations against regulations and best practices like NIST, HIPAA, CIS, and ISO. See where your configurations drift from best practices to improve your SaaS security posture and maintain compliance.
The Posture Dashboard highlights misconfigurations that can expose Salesforce data and where they drift out of compliance.
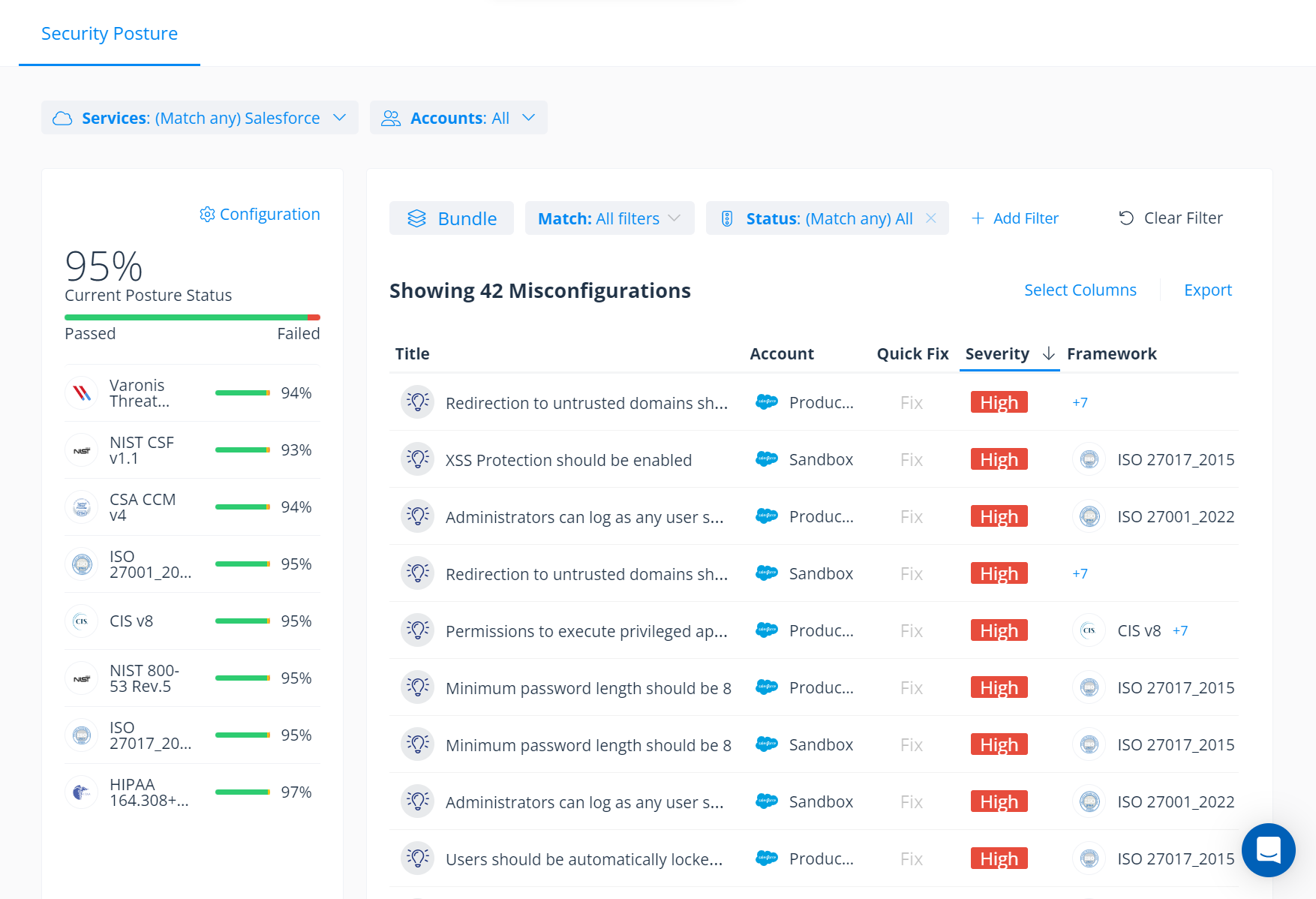
The Posture Dashboard highlights misconfigurations that can expose Salesforce data and where they drift out of compliance.
The Insights Dashboard includes findings from our elite cybersecurity research team. Such findings include Einstein’s Wormhole — a misconfiguration that exposed admins’ calendars through a Salesforce Community bug. Any time the team finds a potential SaaS configuration risk, Varonis can scan your environment and alert you if we think you’re exposed.
Manage third-party application risk.
If given the correct permissions, whether on purpose or on accident, end users can add third-party apps to Salesforce without any additional IT or security oversight. Those apps can pose significant data exposure and supply chain risk.
Security admins have very little visibility or control over these applications without a central control panel to manage and monitor risky integrations, often lacking insight as to what sensitive data these apps can access and the actions they can perform.
With Varonis, security teams can easily discover all the third-party apps
connected to Salesforce and gain a clear view of the risks they pose. Varonis enables organizations to better understand each app’s blast radius, monitor app activity, and remove unsanctioned or unused app connections — right from a single console.
Gain a clear view of your third-party app risk with Varonis' centralized risk dashboard.
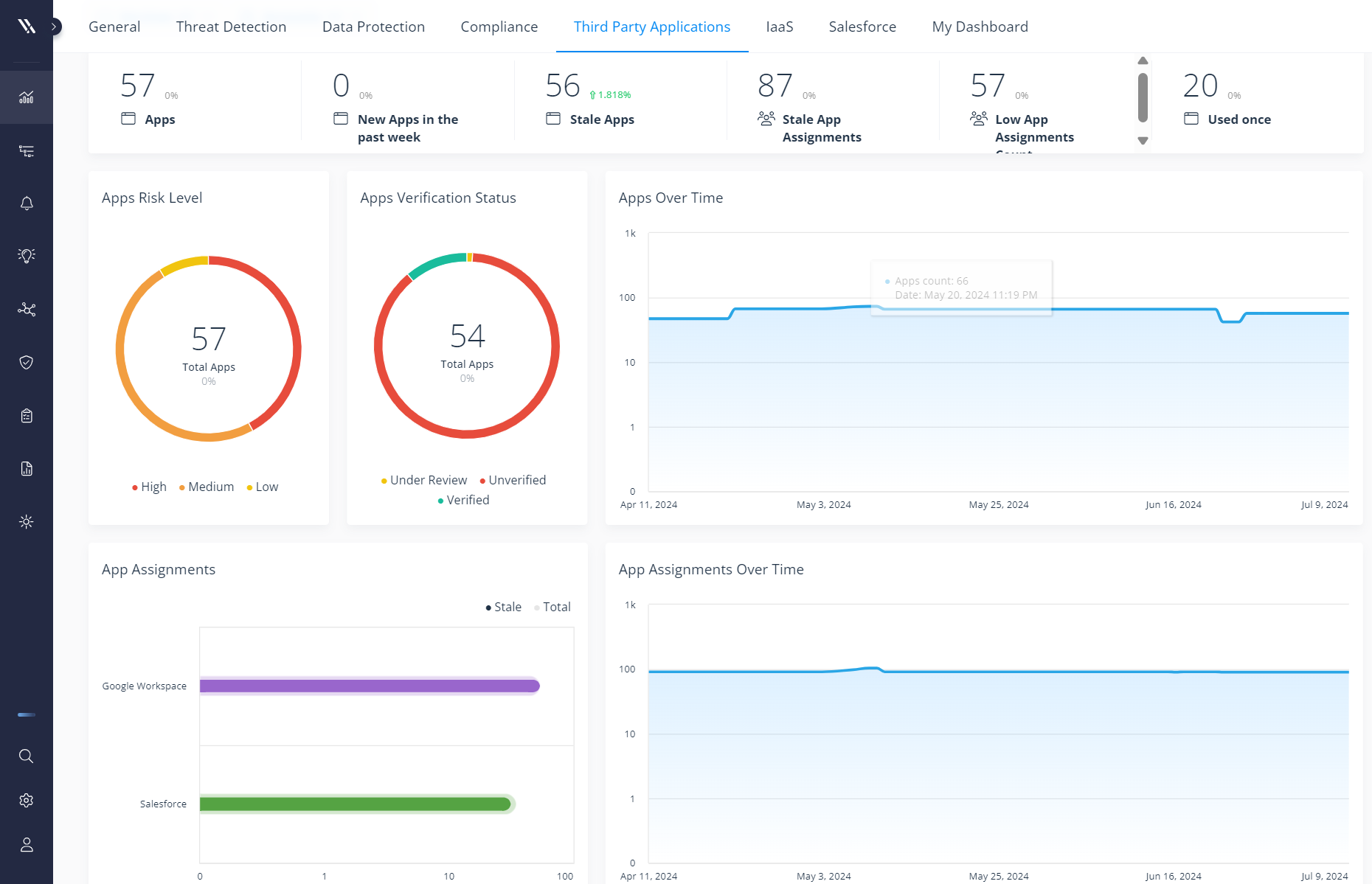
Gain a clear view of your third-party app risk with Varonis' centralized risk dashboard.
Try Varonis for Salesforce
Varonis is blazing a new trail in Salesforce security with never-before-seen permissions analysis capabilities, industry-first risk remediations, and unmatched data classification capabilities that add to our already robust unified security platform.
When it comes to protecting your sensitive data, knowing where it exists, who can access it, and what they’re doing with it are all critical questions to answer. Only Varonis is integrating all these critical data security capabilities into one platform.
Varonis protects Salesforce and other SaaS apps like Google Drive, Box, AWS, Zoom, Okta, GitHub, Jira, and Slack.
If you’re curious to see what risks may exist in your SaaS environment, reach out to start a trial. In minutes, we can have you up and running.
What should I do now?
Below are three ways you can continue your journey to reduce data risk at your company:
Schedule a demo with us to see Varonis in action. We'll personalize the session to your org's data security needs and answer any questions.
See a sample of our Data Risk Assessment and learn the risks that could be lingering in your environment. Varonis' DRA is completely free and offers a clear path to automated remediation.
Follow us on LinkedIn, YouTube, and X (Twitter) for bite-sized insights on all things data security, including DSPM, threat detection, AI security, and more.



-1.png)




.png)
.png)