Sometimes when I speak with organizations about sensitive data risk, I hear things like, “All of our data is sensitive,” or “We’re sure PII is only in X system.” But it’s not what you know that might be your biggest problem — it’s always what you don’t know.
Discover your weak points and strengthen your resilience: Run a Free Ransomware Readiness Test
Meta, the parent company of Facebook, was recently fined €1.2 billion by the Irish Data Protection Commission (DPC) for transferring European PII to the United States, violating the General Data Protection Regulation (GDPR). Totaling about $1.3 billion, this marks the largest-ever fine under GDPR.
Read on to find out who falls under this EU regulation, why it’s so important to track PII data, and how with continuous discovery and data monitoring, you can protect your organization against fines and risk.
Why is tracking PII important?
The General Data Protection Regulation (GDPR) is a European Union law that applies to any organization that processes the personal data of individuals located in the EU, regardless of where the organization is located.
One of the key provisions of the GDPR is that organizations must take appropriate measures to protect personal data from unauthorized access, use, disclosure, alteration, or destruction. The GDPR also sets forth strict requirements for transferring personal data outside of the EU, and it’s because of the GDPR that Meta found itself in hot water.
The DPC found that Meta had failed to implement adequate safeguards to protect European user data from being accessed by U.S. law enforcement agencies. The DPC also found that Meta had not obtained the necessary consent from European users for the transfer of their data to the United States.
This fine, which Meta has said that it will appeal, is a significant development in the ongoing debate over the transfer of personal data between the European Union and the United States. The GDPR has been criticized by some for making it too difficult for businesses to transfer data between the two regions. Now, the fine could lead to more businesses taking steps to comply with the GDPR, or it could lead to changes to the GDPR itself.
Organizations that store personal data on U.S. servers should be aware of the risks involved. The GDPR allows for fines of up to €20 million or four percent of global annual turnover, whichever is greater, for organizations that violate the GDPR.
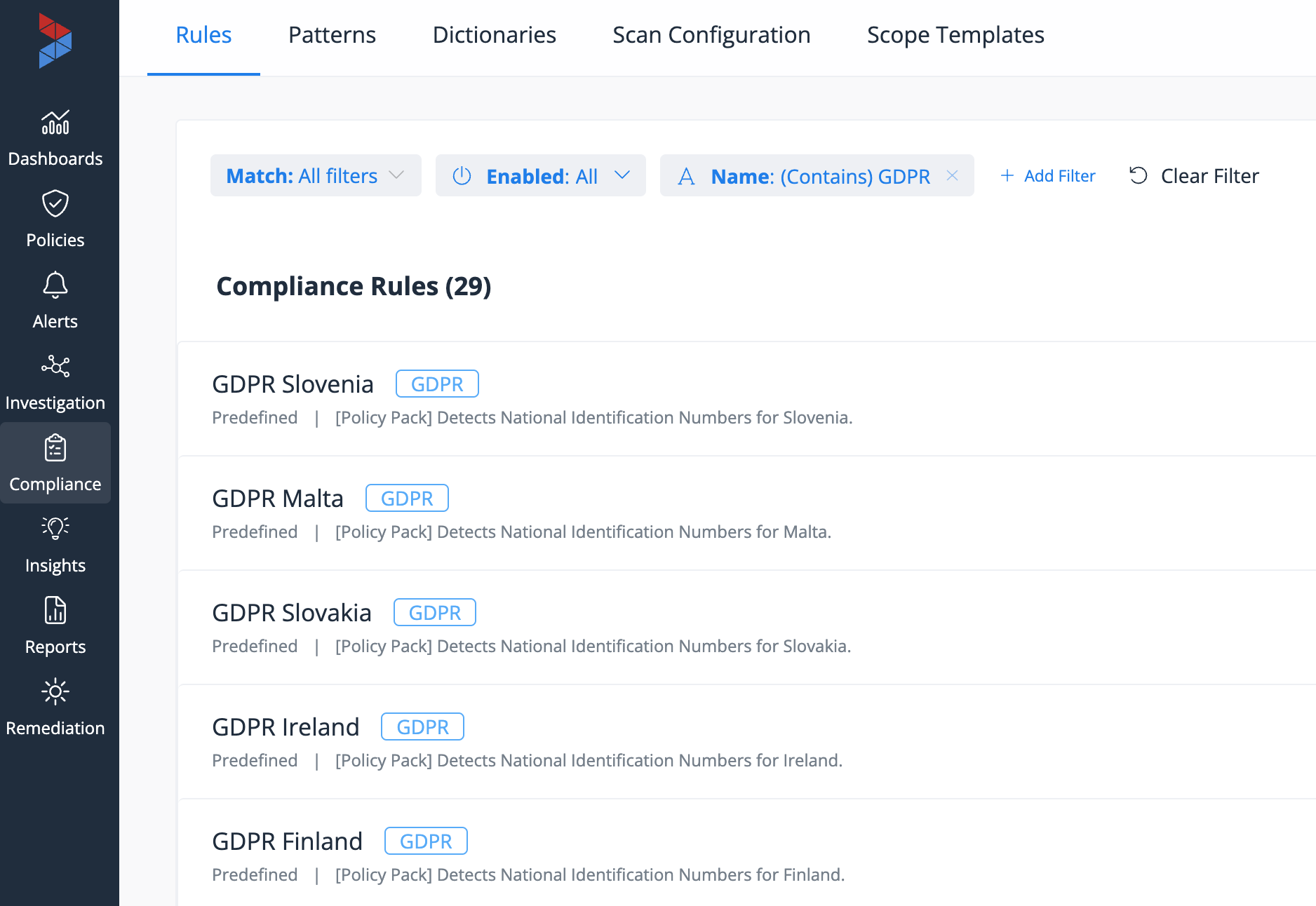 A sample of Varonis' built-in policies to accurately identify EU citizen PII.
A sample of Varonis' built-in policies to accurately identify EU citizen PII.
How can you protect yourself?
To reduce the risks of storing personal data on U.S. servers, organizations should continuously monitor their data to identify where all of their PII is — once you start looking, you’ll find PII and other sensitive data in places you don’t expect, accessible by people you don’t expect, and often being used in ways you don’t expect. Continuous monitoring also helps you quickly detect and respond to security incidents and identify and address risks before they lead to a data breach.
 It's important to have a centralized inventory of PII across cloud apps, cloud infrastructure, and on-prem data stores to quickly identify misplaced or exposed data.
It's important to have a centralized inventory of PII across cloud apps, cloud infrastructure, and on-prem data stores to quickly identify misplaced or exposed data.
By taking these steps, organizations can help to protect personal data, while reducing the risk of fines under the GDPR.
Continuous discovery and data monitoring can also help you:
- Identify and eliminate security vulnerabilities in your systems and applications. Once a vulnerability is identified, it can be remediated to prevent unauthorized access to data.
- Detect and respond to data breaches. If a data breach does occur, continuous discovery and data activity auditing can help organizations detect the breach quickly and respond effectively, minimizing the damage caused by the breach.
- Comply with regulations. Many regulations, such as the GDPR, require organizations to have processes in place to discover and monitor data. By complying with these regulations, organizations can help to protect themselves from fines and other penalties.
You can’t properly protect data if you can’t find it, and you can’t fix risks you don’t know about. Continuous discovery and data monitoring is a critical part of any organization's data security program. By implementing these processes, organizations can help to protect their data, comply with regulations, and reduce the risk of fines.
What should I do now?
Below are three ways you can continue your journey to reduce data risk at your company:
Schedule a demo with us to see Varonis in action. We'll personalize the session to your org's data security needs and answer any questions.
See a sample of our Data Risk Assessment and learn the risks that could be lingering in your environment. Varonis' DRA is completely free and offers a clear path to automated remediation.
Follow us on LinkedIn, YouTube, and X (Twitter) for bite-sized insights on all things data security, including DSPM, threat detection, AI security, and more.



-1.png)




