Phishing campaigns do not always rely on spoofed domains, compromised accounts, or obvious impersonation. Rather than building trust, some attackers are borrowing it—blending seamlessly into expected enterprise workflows by abusing legitimate SaaS infrastructure.
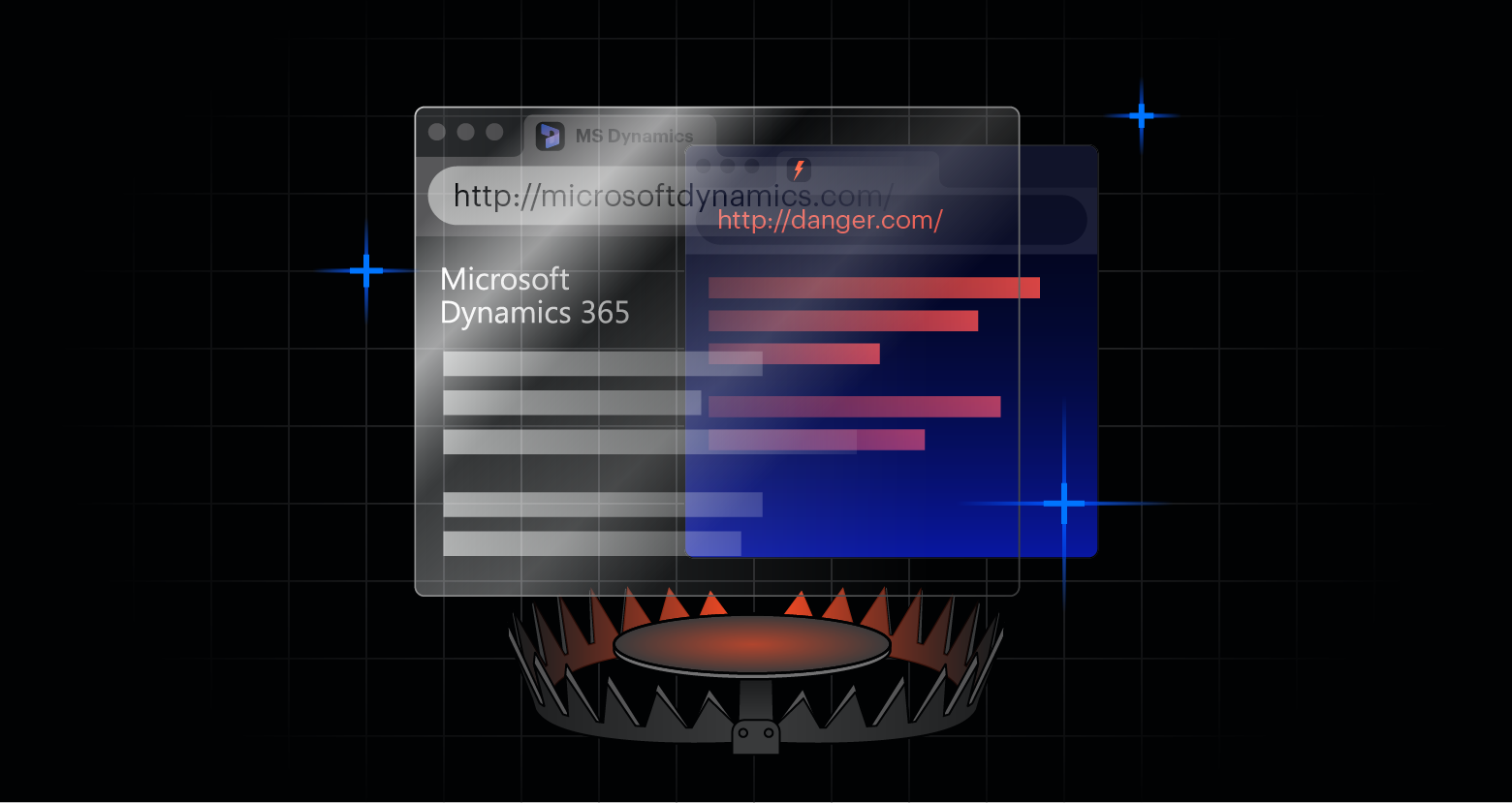
In a 2026 campaign using Microsoft Dynamics 365 Marketing redirect functionality, one group of attackers delivered phishing payloads by leveraging the reputation of a Microsoft‑owned domain. This approach allowed malicious links to bypass many traditional email security controls without exploiting a vulnerability or compromising a user account.
Varonis Interceptor detected and stopped this activity across dozens of accounts, blocking 862 phishing emails originating from a single Dynamics tenant.
The anatomy of the attack
What made this campaign noteworthy was not just its scale, but how cleanly it operated—demonstrating how trusted platforms can be weaponized without breach, compromise, or misconfiguration.
Redirects as delivery infrastructure
Every phishing email in this campaign contained a Microsoft Dynamics Marketing click‑tracking URL hosted on mkt.dynamics.com. These URLs are designed to measure user engagement for legitimate marketing campaigns, redirecting recipients to downstream destinations while recording attribution data.
In this case, attackers used that same mechanism to deliver phishing payloads.
Each link followed the same structural pattern, pointing to a Dynamics API endpoint intended for redirection. Importantly, this was not a look‑alike domain or typo‑squat. The URLs were hosted entirely on Microsoft‑owned infrastructure, allowing them to pass basic domain reputation checks and appear legitimate to both users and security scanners.
Per-recipient tokenization and tracking
Rather than reusing links, the attacker generated unique redirect tokens for every recipient - even when multiple victims were sent to the same final destination.
This design served two purposes. First, it prevented reuse‑based detection and simplified blacklist avoidance. Second, it enabled per‑victim tracking, leveraging native Dynamics analytics parameters such as msdynmkt_digest and related fields.
From the URLs alone, Varonis could infer that the attacker was tracking who clicked, when, and which payload was delivered—behavior that is characteristic of professionally operated phishing frameworks, not commodity phishing kits.
Concealed payload delivery
The true phishing destination was embedded inside double‑encoded URL parameters. Without decoding those parameters, email security tools would see only a legitimate Microsoft redirect.
Final payloads were hosted on external, attacker‑controlled domains, including domains registered in multiple regions. This separation of delivery infrastructure (Microsoft) from payload hosting (attacker) allowed the campaign to rotate malicious destinations without altering its trusted surface.
Impact analysis
Interceptor observed this campaign across dozens of accounts, spanning a wide range of industries:
- Manufacturing & Industrial - 23%
- Public Sector and Education - 19%
- Financial Services & Insurance - 14%
- Construction and Engineering - 13%
- IT, Cloud, and Cybersecurity - 12%
- Healthcare - 3%
- Other sectors - 8%
The widespread impact of this attack reinforces a key point: no industry was uniquely targeted. Instead, the campaign appears to have been designed for broad, cross-sector impact.
Why Dynamics 365 keeps appearing in phishing campaigns
Microsoft Dynamics has appeared in phishing campaigns before and has become attractive to attackers for the same reason it’s valuable to enterprises: deep integration, high trust, and broad adoption. Consistently, these campaigns are not exploiting any software vulnerabilities in Dynamics, instead taking advantage of the implicit trust the platform holds.
Microsoft itself warned about phishing emails impersonating Dynamics‑related invoices as early as 2018, noting attackers sending fake Microsoft invoices to lure victims into payment or credential theft. While less sophisticated than modern SaaS‑abusecampaigns, this established Dynamics as a recurring phishing theme.
Other attacks have included fake document delivery via Dynamics-hosted PDFs, embedding real and fake Dynamics 365 Customer Voice links, and portal and page abuse inside Dynamics 365 environments.
Where traditional Email Security solutions failed
This campaign succeeded by exploiting several common assumptions in email security:
- Trusted domains are low risk
- Redirects from SaaS platforms are benign
- Static reputation signals are sufficient
Because the malicious behavior occurred after a legitimate redirect, many other solutions never inspected the final destination or did so too late to prevent delivery. Additionally, per‑recipient tokenization limited the usefulness of shared indicators of compromise. Even when one link was identified as malicious, that knowledge did not easily transfer to other recipients.
The result was a campaign that blended into normal business traffic while quietly delivering malicious content downstream.
How Varonis Interceptor stopped the attack
Varonis Interceptor successfully detected and blocked this campaign across all observed customers by evaluating behavior beyond initial trust signals.
Rather than relying solely on sender reputation or domain allow‑lists, Interceptor followed links through the entire redirect chain and detonated them in its AI Phishing Sandbox, analyzing post-redirect behavior, destination content, and downstream activity. This depth and breadth of analysis allowed Interceptor to determine where links ultimately led and how those destinations behaved, even when the delivery mechanism itself was trusted, legitimate, and widely used in enterprise environments.
Interceptor also maintained consistent detection even as redirect tokens, URLs, and payload domains varied on a per-recipient basis. By correlating behavioral indicators across individualized links rather than relying on reusable indicators of compromise, Interceptor identified the campaign as a coherent phishing operation despite its high degree of variability.
Defensive outlook for modern Email Security
For security teams, the key lesson is not that Microsoft Dynamics was uniquely vulnerable, but that implicit trust in widely used SaaS platforms has become a structural blind spot. Redirects, tracking links, and tokenized URLs are now routine components of business communication, and attackers are deliberately designing campaigns that are indistinguishable from normal workflows at the point of delivery.
Security teams should assume that attackers will continue to weaponize legitimate features of trusted services, particularly those designed to scale, personalize, and track user interaction. Addressing this challenge requires visibility through trusted infrastructure, not just around it.
Varonis Interceptor is designed for this reality. By inspecting post‑redirect behavior and evaluating where links from trusted sources ultimately lead, Interceptor helps security teams detect phishing campaigns that operate entirely within legitimate SaaS ecosystems—closing the gap between assumed trust and actual risk.
What should I do now?
Below are three ways you can continue your journey to reduce data risk at your company:
Schedule a demo with us to see Varonis in action. We'll personalize the session to your org's data security needs and answer any questions.
See a sample of our Data Risk Assessment and learn the risks that could be lingering in your environment. Varonis' DRA is completely free and offers a clear path to automated remediation.
Follow us on LinkedIn, YouTube, and X (Twitter) for bite-sized insights on all things data security, including DSPM, threat detection, AI security, and more.


-1.png)