DNS TTL (time to live) is a setting that tells the DNS resolver how long to cache a query before requesting a new one. The information gathered is then stored in the cache of the recursive or local resolver for the TTL before it reaches back out to collect new, updated details.
For example, if the DNS TTL is set to 1800 seconds (30 mins), the resolver will have to regather the details around a website like varonis.com every 30 minutes. If 100 users visit the site in that period, they will all see the same thing, until the resolvers update their TTL. Time to live is the least understood in regards to the overall DNS strategy. In the following guide, we will learn about all the details around how DNS TTL operates and also some strategy best practices.
Get the Free Pentesting Active
Directory Environments e-book
If you would like to jump directly to the specifics, use the menu below:
- What is a DNS TTL?
- What is DNS TTL Used for?
- How to Choose DNS TTL Values
- Reasons for Long & Short DNS TTLs
- DNS TTL Troubleshooting
- DNS FAQs
- DNS TTL Best Practices
DNS TTL Considerations + Basics
Some high-level considerations need to be understood regarding DNS TTL strategy. A noticeable positive is the quick turnaround time on DNS lookups, thus speeding up your internet browsing experience overall. It is much faster to check a cached version against your local resolver than it is to perform a DNS record lookup.
Now we have to point out some of the pitfalls of TTL, starting with something called DNS Propagation. DNS Propagation is essentially the time it takes for ISPs to update their caches with your new DNS changes. We will get into this in more detail later in the article.
What is a DNS TTL?
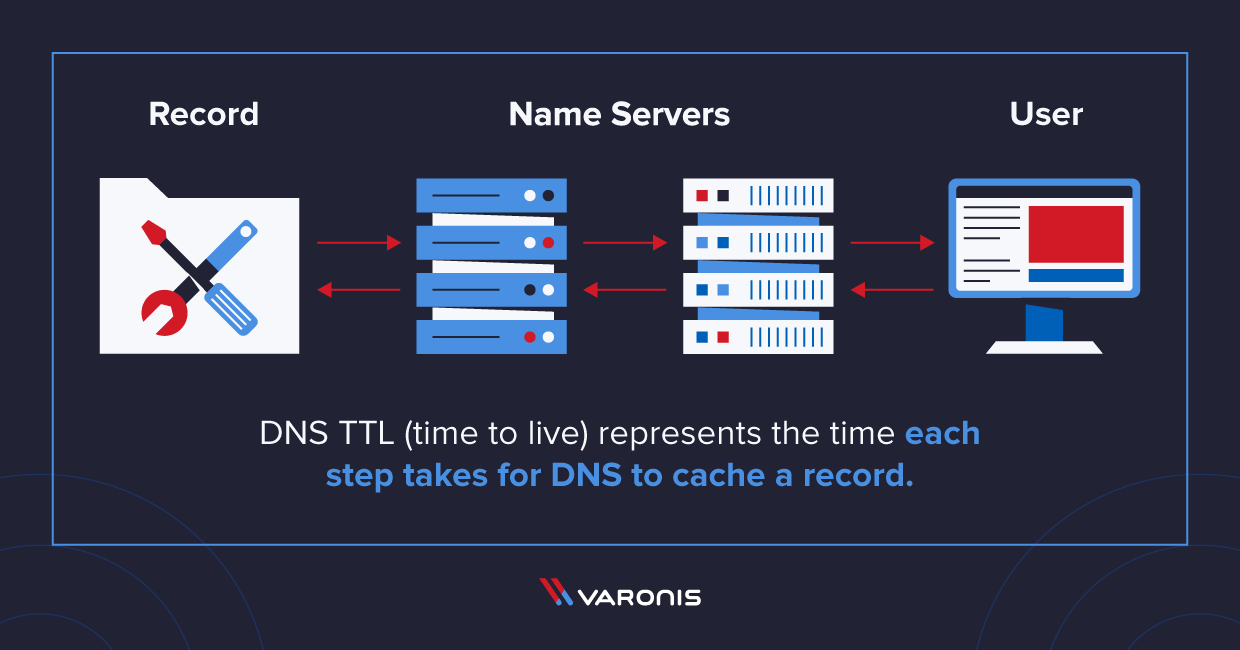
DNS TTL (time to live) represents the time each step takes for DNS to cache a record. The TTL is like a stopwatch for how long to keep a DNS record.
It is essential to understand how you are implementing your TTL. You want it to be the perfect balance between “quickly updating” and “resource savvy.” Straying too far in either direction it will cost you both time and resources to accommodate.
What is DNS TTL Used for?
DNS TTLs are vital to websites that make constant changes and updates frequently. By having a lower TTL, you can ensure that you are receiving the most recent updates in a given timeframe.
Your time to live is critical in controlling your resolver caching directly. For example, your DNS resolver will pull a DNS record from its authoritative server every hour. Then for that hour, every user that queries that DNS site will receive a cached version of the website until the resolver pulls another update copy from the authoritative server again. This process of utilizing the resolver’s cache significantly improves your end-users’ overall experience.
What is a DNS Record?
A Domain Name Server (DNS) record is ultimately a simple message that specifies which destination a request should be directed to and how long this specific destination should be cached for before being updated (TTL).
What are typical TTL times for DNS records?
TTL times are always represented in seconds; for example, 300 seconds equals 5 minutes to live. The following TTL times will give you a rough estimate of what typically is set in DNS configuration:
300 seconds = 5 minutes = “Very Short” – Websites within this timeframe use a low TTL focus to make fast changes but still can utilize some level of caching to help reduce resource consumption.
3600 seconds = 1 hour = “Short” – Websites within this timeframe use a low TTL focus to make fast changes but still can utilize some level of caching to help reduce resource consumption.
86400 seconds = 24 hours = “Long” – The opposite applies for websites using a 24 hour TTL as the focus shifts more towards a daily cache utilization.
604800 seconds = 7 days = “Very long” – Weekly TTLs are not as common, but may be used for sites that contain publish or reputable information that does not change all that often (ex. Library resources, reference sites, etc.)
Common Record Types
It is essential to understand the different record types and how they might apply to your situation. Having a good understanding of what is vital to your website will play a critical role in selecting an appropriate time to live. Below, we outline some considerations to take into account.
- A or AAAA Record: Your A records should be set to a faster pace TTL as IP address lookups change frequently. A standard baseline would be around the 1-hour mark but may need to be adjusted depending on how often changes need to be made on an emergency basis (30 seconds here is not crazy).
- CNAME Record: Your main website URL, for example (www.example.com), should usually never change. It is recommended that you set your TTL for something longer than the average session time (which is between 2-3 minutes).
- TXT Record: Widely used for DKIM records, email security and verifying domain ownership. TXT records are rarely changed so anywhere within the 1 – 12-hour timeframe should suffice.
- MX Record: Your mail exchange TTL can be set between the 12-24 hour range, but you may want to consider placing it lower in case of emergencies; somewhere in the 1-4 hour range would be useful as well.
Why is DNS Cached?
The ultimate goal of DNS caching is to speed up internet load times and decrease the load on the DNS servers. Having a cached DNS allows for the end-user to quickly resolve DNS requests without much delay. The only downfall to caching is if your TTL is set too long for the updates required for your site, the end-users may have a delay in receiving the updated site until the TTL has expired.
Why DNS is about Network Connections, not Devices
Another complexity added is in all the different devices and network connections that happen on a corporate network. Each device on a network may need to update its records at different times or demand more depending on the job at hand. This is where TTL must be accurately set as if you are making a network-level change, but if the TTL on these devices is still on a cached copy, you could cause a panic that “the system is broken” or its “not in sync.” Ensuring that proper tuning is made to all the common records is vital to obtaining an overall network experience that is fast and timely.
How to Choose DNS TTL Values
Now that we have a general idea of what these values are responsible for, we are going to dig in to introduce ways to select values that are fitting to your environment.
What are typical TTL times for DNS TTL Values?
Knowing a baseline for implementing correct TTL for your DNS values is crucial to the overall responsiveness. The following will give you an idea of what the ranges are for the top 500 websites and their averages. Sites included on this list range from local news sites to google.com.
| Lowest TTL: | 1 |
| Highest TTL: | 129,540 |
| Domains Resolved: | 485 |
| Average TTL: | 6468 |
| Median TTL: | 300 |
See Moz’s Top 500 Websites and download the CSV.
Reasons for Long & Short DNS TTLs

There are many reasons why you may consider to go long or short with your DNS TTLs. Below, we have outlined some popular reasons for each to help show you that TTLs can help benefit all different aspects of the business.
Reasons for Long:
- Security availability: Availability of service if the DNS server is ever down for a time (DDoS), still available on the local resolver cache
- Infrastructure: Static site that doesn’t often change, less of a burden on your DNS servers
- User Experience: Faster responses from cache
Reasons for Short:
- Network: Network-wide changes that need to be implemented quickly
- End-User: Frequent updates or changes made to websites
- Infrastructure: DNS based load balancing
Recommendations for DNS TTL Values
Digging deeper, you may be curious how different TTLs are distributed across different professions. The following are some of our recommendations based on a person’s responsibility in regards to DNS availability.
- “For general zone owners”: Longer TTLs are advised (1,4,8 and 24 hours) based around planned maintenance windows to maximize cost benefits.
- “For registry operators”: Longer TTLs (around 1 hour) to allow public registration of domains.
- “For network engineers”: DNS load balancing using short TTLs to ensure quick turn over in the event of system failure or outage.
- “For security engineers”: DDoS prevention by utilizing short TTLs to provide most recent DNS updates are available when implementing blocking controls.
DNS TTL Troubleshooting

It is imperative to understand all the ins and outs involved with troubleshooting DNS issues. Proper tuning of TTL at certain times could save your money and time.
How Long Will it Take My DNS to Update?
To honestly know that everyone is seeing an updated DNS record, it is essential to calculate how long it will “actually” take to propagate across DNS. This is accomplished by using the following formula
TTL X (number of steps) = Fully propagated
For example, if your set TTL is 1800 seconds and there are five steps (not counting the authoritative server), then your fully propagated time would be 9000 seconds or no longer than 2 hours and 30 minutes.
What Factors Affect DNS Propagation Time?
As described above, the number of steps is one key factor to consider with calculating propagation time. But the following hidden factors are also things to consider when calculation propagation.
- Network connection bandwidth speeds
- Global load or outages
- Caching or not caching
Speeding Up DNS Propagation
There are several ways to speed up DNS propagation. The first is to ensure you switch your TTL to a short time frame to ensure the distribution happens sooner, rather than waiting for your long TTL to expire.
Next would be to ensure your DNS provider supports dynamic changes. This allows you to change your records globally.
Lastly is to test DNS propagation by utilizing several different propagation checkers to ensure the change has taken.
DNS Propagation Check and DNS Lookup
Using several different DNS propagation tools is highly recommended to ensure your changes have taken hold globally. Most of the propagation tools available are free to use and allow you to check against all record types. This check is critical to assess the timing and whether or not any problems have arisen during the rollout.
How Do DNS Lookups Work?
When a DNS request is initiated, the first action that is performed is a local cache check to see if this record has been searched before? If not, then DNS moves on to requests a record. If yes, the DNS then determines if the cache TTL is still active.
These two steps ( checking record cache and checking the TTL) are the first thing to happen with every DNS request guaranteed. If neither of these two questions can be answered with a yes, then a new request is generated to collect a new record.
How much does a DNS lookup cost?
DNS lookups are generally a free service in terms of money, but what you should be most concerned with is how much time it is going to cost you. Each request typically takes around 150 milliseconds to complete. You may be thinking, “that’s nothing,” but when you have thousands of these happening a second, it adds up pretty quickly. Every time someone loads your webpage or resource without caching enable, you are adding another 150 milliseconds to that time bill. Let’s break down an example of this time cost.
Naive DNS Cost Calculations
The following is a detailed example of loading a typical webpage with caching enabled and one without cache enabled. You will notice that the end cost is almost double that without caching. This is why it is so important to find that perfect balance with your TTL setting.
With Caching
(30 image files * 50ms to download each) + (100 ms one-time lookup of the DNS which is then cached) = 1600ms
Without Caching
(30 image files * 50ms to download each) + (30 * 100ms DNS lookups) = 3000ms
DNS TTL Best Practices
See some different DNS TTL best practices for change management listed below.
How do I know when a client will request the updated DNS record?
It is essential to understand that DNS TTL is not an instant change or an expiry date. Think of it as a rollercoaster ride. When you get on a rollercoaster, the tenets of the coaster must walk by and check that everyone’s seatbelt and bar are correctly placed. They start and one end and work their way to the end of the coaster, they can check everyone all at once on demand.
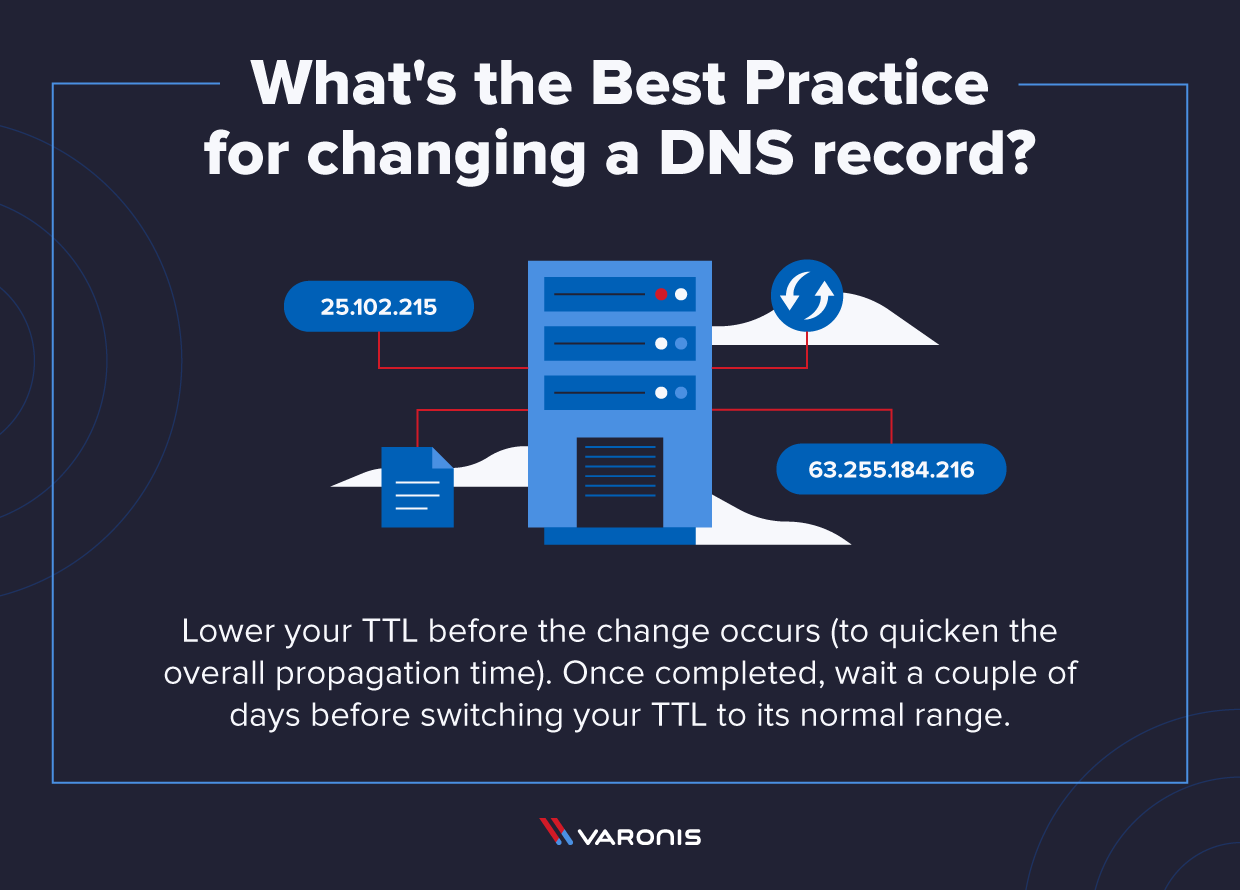
What’s the Best Practice for adding a new DNS record?
Adding a new record is much easier than modifying an existing one. Still, the same best practice is encouraged for lowering your TTL before and then raising back to normal levels shortly after the new record is created.
What’s the most common TTL setting?
Earlier in the article, we reviewed the averages for the top 500 Moz domains, comparing their TTLs. It is safe to say that a solid long TTL is around 1 hour (3600 seconds) and a short TTL of 5 minutes (300 seconds).
Hopefully, this article will be insightful in helping organizations fine-tune their DNS TTL to optimize performance and availability across its resources.
If you are concerned about your network perimeter now with everyone working from home due to the COVID-19 crisis, check out what the professionals are using to ensure data exfiltration is not happening on their watch.
DNS TTL FAQs
Below we’ve included commonly asked questions around using DNS platform tools.
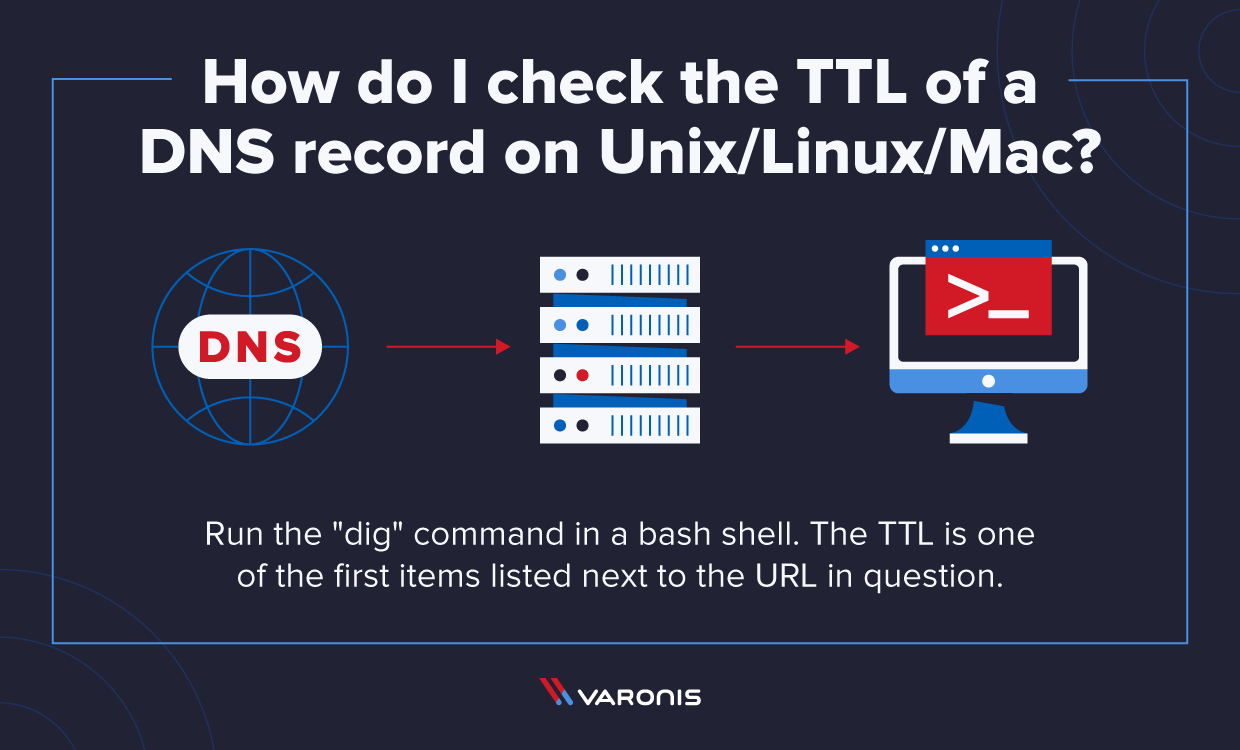
How do I check the TTL of a DNS record on Windows?
Simple, you probably have run this command before and didn’t even realize it. From your command prompt (CMD) run “nslookup” then the name of your URL to resolve. You can get specific and check things like the CNAME or even produce different levels of information straight from this one-line command. Below is an example of performing a nslookup in Windows:
Example: C:\>nslookup -type=cname -debug www.varonis.com
- Example: C:\>nslookup -type=cname -debug www.varonis.com
Example: C:\>nslookup -type=cname -debug www.varonis.com
Example:
dig www.varonis.com
The TTL is shown outlined in red.
How do I check a DNS record from the Web?
There are tons of DNS record checking websites and tools available for on the go DNS checking. Google has a free version of its DNS checker that is very lightweight and effective.
Is there any way to force a client to update their DNS record remotely?
Unfortunately, there is not a way to “force” a DNS record update remotely. The best advice is to plan ahead of time and change your TTL to a short time before making a significant change.
What should I do now?
Below are three ways you can continue your journey to reduce data risk at your company:
Schedule a demo with us to see Varonis in action. We'll personalize the session to your org's data security needs and answer any questions.
See a sample of our Data Risk Assessment and learn the risks that could be lingering in your environment. Varonis' DRA is completely free and offers a clear path to automated remediation.
Follow us on LinkedIn, YouTube, and X (Twitter) for bite-sized insights on all things data security, including DSPM, threat detection, AI security, and more.




-1.png)