- Cloud-native
- Continuous
- Automated
Trusted by thousands of companies
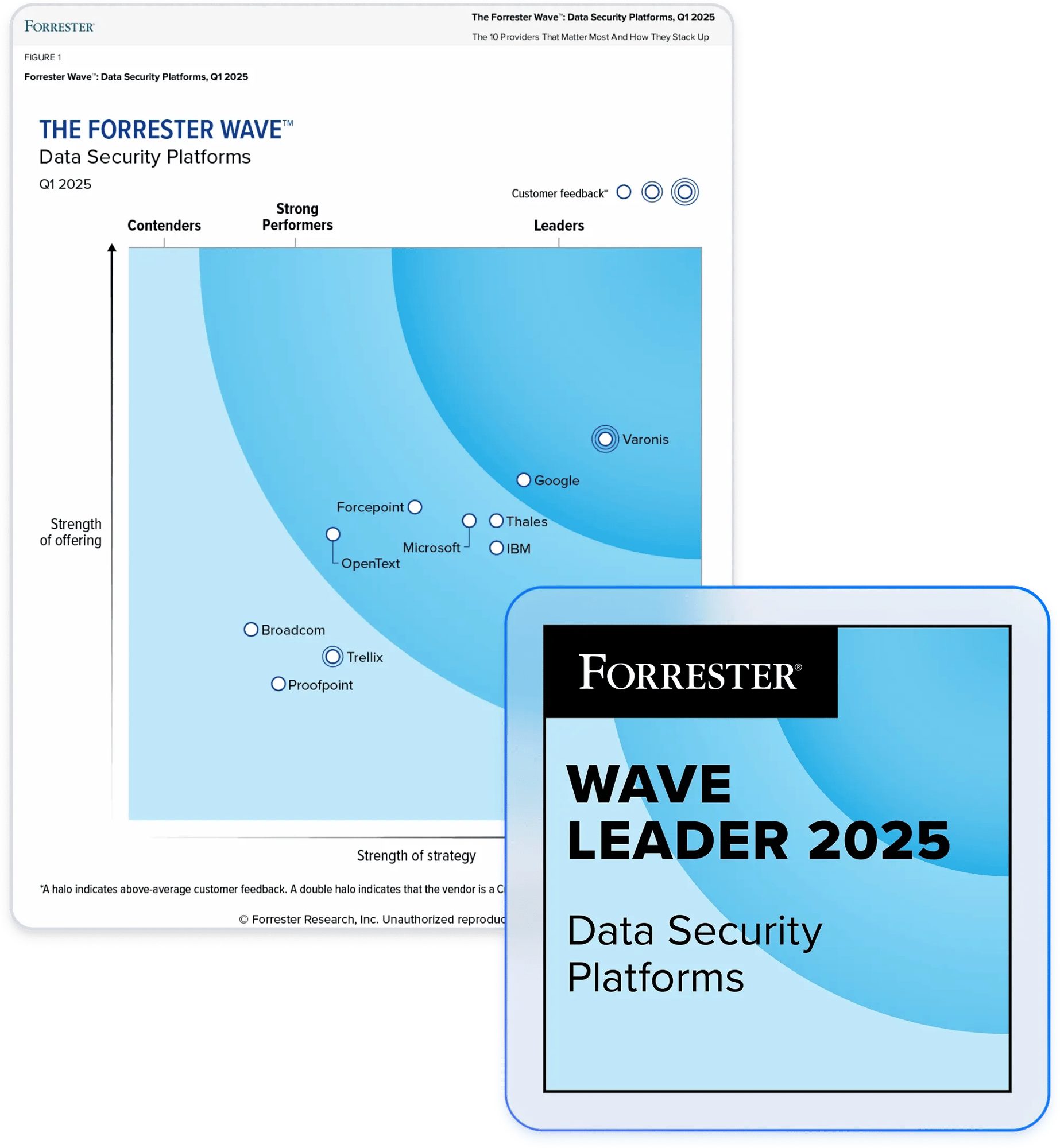
Partner with the leader in data security.
Agentless DLP that stops cloud data breaches.
Discover everything, everywhere
- Structured databases and data warehouses
- Unstructured data in files, folders, and buckets
- Semi-structured data in SaaS apps and email
Secure exposed sensitive data automatically
- Reduce your blast radius
- Detect public exposure
- Spot misconfigurations
Detect and stop data exfiltration
- Alert on abnormal behavior
- Automate responses
- Get 24x7x365 MDDR coverage
“Most solutions focus on data loss prevention. But detection, prevention, and investigation are all interrelated. No other solution does all three as well as Varonis."
Senior Security Engineer
US Energy Provider
Read case studyCross-cloud policy enforcement
Varonis fully integrates with your SaaS and IaaS platforms to create policies that work across your cloud environment, automatically fix posture, and create and re-label files as your data changes — making downstream DLP controls more effective.
Posture control automation
Cloud-first organizations must maintain robust data and identity security controls across each cloud service. Varonis consistently maintains posture for each data store with automated detection and remediation.
Data lifecycle automation
Varonis manages data from creation to retention and removal. Varonis allows you to seamlessly copy and move data – cross-domain or cross-platform – without the risk of breaking permissions or interrupting business.
Data privacy automation
Battle-tested in complex multi-petabyte environments, Varonis provides complete, current, and contextual data privacy classification. Restrict visibility of sensitive data with dynamic data masking and flag overexposed files for remediation.
Our customers have spoken
Protect your data, wherever it lives.
One platform for complete data security across multi-cloud, SaaS, hybrid, and AI.
DLP Resources
Go beyond DLP.
Varonis tackles hundreds of use cases, making it the ultimate platform to prevent data breaches and ensure compliance.
Ready to see the #1 Data Security Platform in action?
Ready to see the #1 Data Security Platform in action?
“I was amazed by how quickly Varonis was able to classify data and uncover potential data exposures during the free assessment. It was truly eye-opening.”
Michael Smith, CISO, HKS
"What I like about Varonis is that they come from a data-centric place. Other products protect the infrastructure, but they do nothing to protect your most precious commodity — your data."
Deborah Haworth, Director of Information Security, Penguin Random House
“Varonis’ support is unprecedented, and their team continues to evolve and improve their products to align with the rapid pace of industry evolution.”
Al Faella, CTO, Prospect Capital