Automatically enforce data governance, lifecycle, and compliance policies without writing any code.
- Automated
- Secure
- Scalable

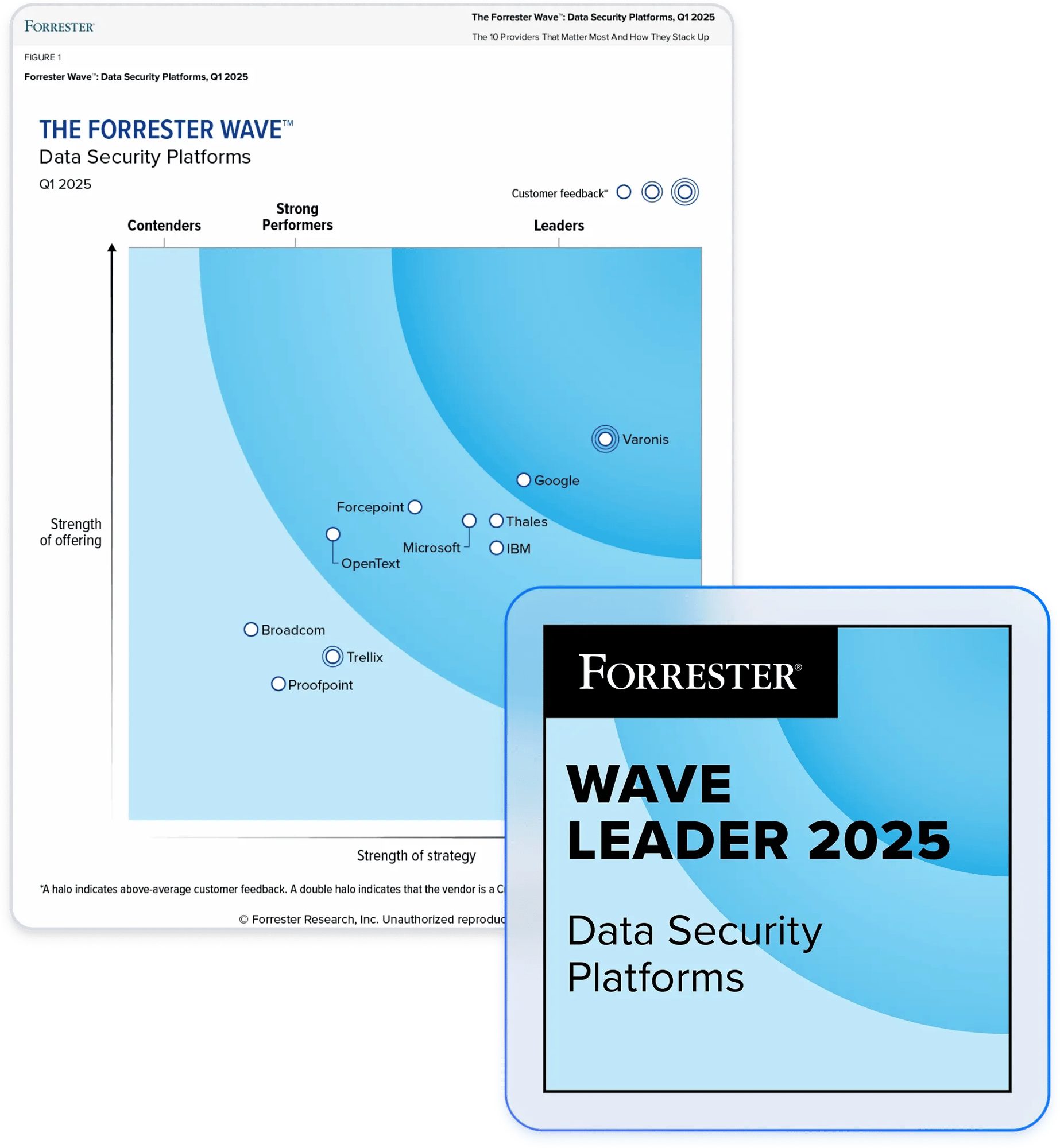
Partner with the leader in data security.
Automate your data governance and compliance efforts.
Automate data governance
- Enforce lifecycle policies
- Migrate data at scale
- Reduce storage costs
Streamline compliance
- Detect compliance violations
- Enforce retention and residency
- Comply with privacy laws
Reduce the blast radius
- Quarantine out-of-location data
- Eliminate sensitive data exposure
- Prevent risky AI access
“We have the responsibility to protect any type of local government data that you could imagine. Anything from credit card information to healthcare information of our citizens, to critical infrastructure, including traffic lights, water, sewer — and even 911 call operations.”
CISO
Read case studyAutomated policy enforcement
Automatically enforce lifecycle, retention, and residency requirements for different departments, servers, data types, and sensitivity levels. Create and enforce custom data governance and compliance policies without writing code.

Blast radius reduction
Varonis continuously monitors your data and enforces quarantine rules when it detects a policy violation. Automatically relocate data to a pre-determined secure location to reduce data risk and minimize the impact of a breach.

Domain consolidation and cloud migrations
Consolidate domains and handle large-scale cloud data migrations efficiently, ensuring data security and maintaining least privilege access. Take full control of naming conventions, permission structures, and collision behavior to ensure consistency as data moves.

Storage optimization
By continuously monitoring data activity, Varonis identifies stale and obsolete files and automatically transfers them to a designated location for archival or deletion – optimizing storage and reducing costs.

Our customers have spoken
Protect your data, wherever it lives.
One platform for complete data security across multi-cloud, SaaS, hybrid, and AI.
Additional Governance and Compliance Resources
Go beyond data governance.
Varonis tackles hundreds of use cases, making it the ultimate platform to prevent data breaches and ensure compliance.
Ready to see the #1 Data Security Platform in action?
Ready to see the #1 Data Security Platform in action?
“I was amazed by how quickly Varonis was able to classify data and uncover potential data exposures during the free assessment. It was truly eye-opening.”
Michael Smith, CISO, HKS
"What I like about Varonis is that they come from a data-centric place. Other products protect the infrastructure, but they do nothing to protect your most precious commodity — your data."
Deborah Haworth, Director of Information Security, Penguin Random House
“Varonis’ support is unprecedented, and their team continues to evolve and improve their products to align with the rapid pace of industry evolution.”
Al Faella, CTO, Prospect Capital






